Pay2Key
Pay2Key is a malware program that has recently attacked a large number of users, locking their personal data and demanding a ransom to release it. According to researchers, Pay2Key can be found attached to spam messages and it can also be distributed via Trojan backdoor malware.
Ransomware is an incredibly dangerous and widely-spread category of PC viruses and the worst thing about it is the fact that currently there are still not any fully effective methods for handling this sort of infections. There are several different types of Ransomware such as screen-lockers, cryptoviruses and leakware but in today’s article, we will be focusing only on the most problematic of them – the infamous cryptovirus sub-category. One recently released cryptovirus Ransomware is going to be the main topic of the following lines. Its name is Pay2Key Ransomware and although it is a fairly new infection that hasn’t been around for too long the number of computers infected by it is already quite significant with more and more machines falling prey to this insidious virus each day.
The Pay2Key Ransomware
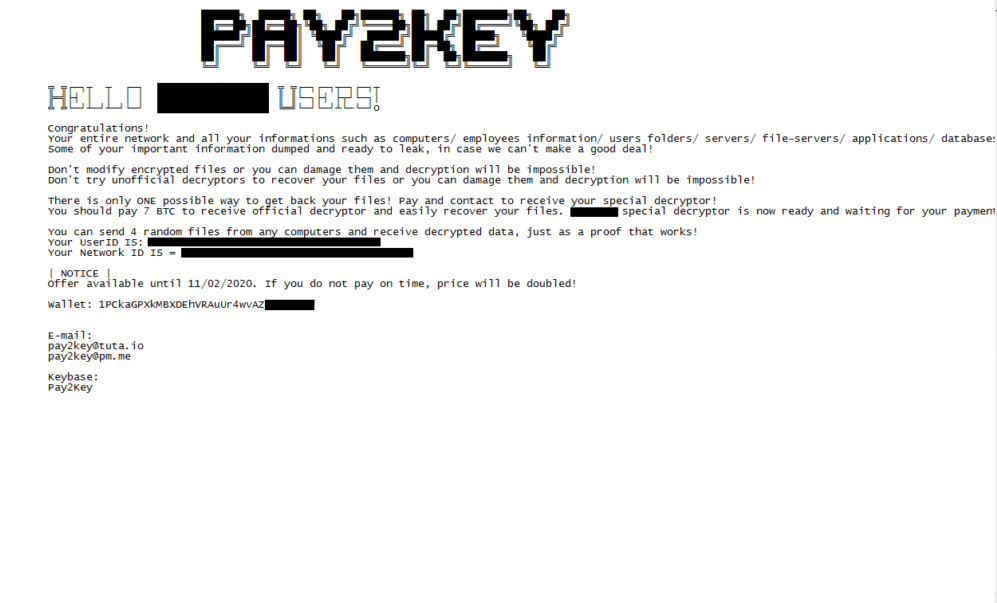
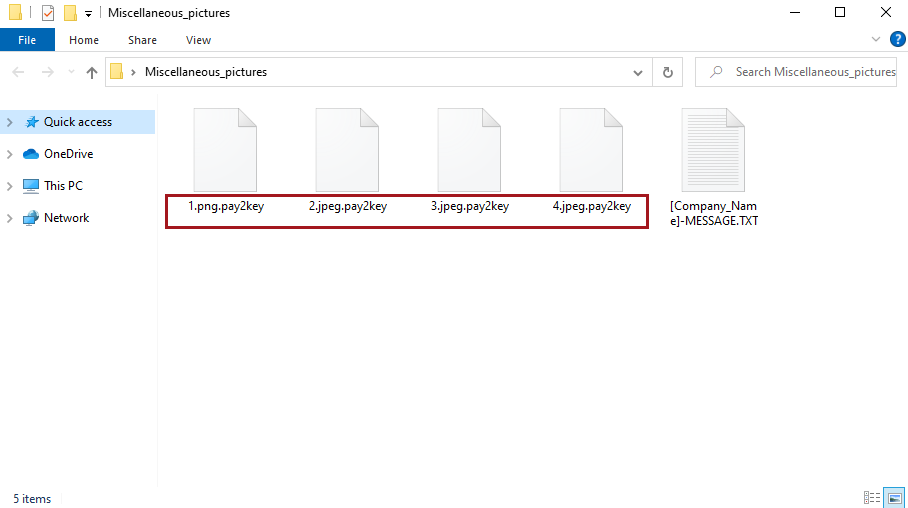
The Pay2Key ransomware is a typical representative of the file-encrypting Ransomware family – a category of threats known for their ability to encryption-lock all the data of their victims. Once the files are encrypted, the Pay2Key ransomware will require you to pay money to its creators for the private decryption key.
The typical thing about cryptoviruses like Pay2Key is that they use encryption to lock the personal files of the targeted victim so that their data would not be accessible without a key that only the cyber-criminal who controls the virus has. Naturally, once all data has been put under the virus’ encryption code, the user would be blackmailed into making a money transfer to the hacker. If the demanded ransom doesn’t get paid, the victim is threatened to lose access to their files for good as the key that the hacker holds is oftentimes the only method of recovering the data. This, however, is not to say that making the payment would guarantee the restoration of the files. Many who had chosen to pay have been eventually left with no means to regain access to the sealed documents since the hackers have refused to send the key. Such instances are commonplace and although it still needs to be said that in most cases such cyber-criminals do give their victims the key upon payment, the possibility of things going the wrong way should one take this course of action is quite real. It’s just inadvisable to directly go for the payment “solution” straight away if your data has been locked by Pay2Key Ransomware. Here, we might have an alternative way out of this for you and though we can’t promise you success, it is still better to first give a try to the method that we suggest as it won’t cost you any money.
In the guide provided within this page, you can find instructions regarding the removal of Pay2Key. Use them to get rid of the malware and then take a look at the section devoted to file-recovery. Follow the steps and try the suggested methods to see if they work for you. Sadly, as we mentioned already, the restoration of your files cannot be guaranteed irrespective of what course of action you choose to follow. However, if you are still considering the payment option, be prepared for the possibility of losing your money to the hackers without actually receiving a decryption key that will enable you to access your files again. If you really need the sealed data and no other option has worked for you so far (and there are no alternatives left), you can always try the ransom transaction variant (although we would advise against it).
The Pay2Key file
The Pay2Key file is an inaccessible file locked by this virus and, typically, the only way to unlock it is through the matching decryption key. The decryption key for the Pay2Key file is possessed by the hackers and they say they will only give it to you if you send them some money.
Viruses that fall under the Ransomware cryptovirus category are known for their stealthiness and their lack of symptoms during the encryption process. Detecting such a threat is can be really challenging as in most cases the only potential red-flags that a Ransomware virus would trigger would be increased RAM and CPU use but one can easily miss that one a computer with lots of virtual memory and a powerful processor. Another issue when about detecting infections like Pay2Key has to do with the fact that since the encryption used by the malware doesn’t really damage any of the files or any system components even a good antivirus may fail to spot the threat and intercept it before it’s too late. The third issue with the encryption of viruses such as Pay2Key is that even after the infection is removed, the data would likely remain locked – this is also the reason why we have separated our guide into two different sections, one for the removal of the virus and one for the restoration of the files.
It should be pretty clear just how devastating a threat such as Pay2Key, .Agho or .Vpsh could be and why one really needs to make sure to protect their computer from such viruses. To avoid future encounters with those noxious cryptovirus threats, we advise you to stay away form online addresses and download sources that are unreliable or illegal. Also, should you come across any type of suspicious-looking content while browsing the Internet, make sure that you avoid any contact and interaction with it so that you don’t put your PC at risk of getting infected. A great piece of advice that can greatly help you with potential future Ransomware attacks is to backup your important data – copy your most valuable files and place them on a separate device or upload them to a cloud storage and no Ransomware should be able to get to them even in the scenario that your computer gets infected by such a virus.
SUMMARY:
| Name | Pay2Key |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | In most cases a Ransomware infection will have little to no symptoms which makes those viruses really difficult to detect in time. |
| Distribution Method | Anything from malicious web spam and malvertising to backdoor Trojans and pirated program downloads. |
| Data Recovery Tool | [banner_table_recovery] |
| Detection Tool |
Pay2Key Ransomware Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Pay2Key files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment