This page aims to help you remove Peta for free. Our instructions also cover how any .Peta file can be recovered.
.Peta
.Peta is ransomware of the STOP Decryptor strain that features .Seto, .Hese and .Gero among others. .Peta aims to extort from its victims money in the form of untraceable bitcoins.
In the event that a strange malware program has locked your files with a strong encryption, and has asked you to pay a ransom to access those files, then you most probably have become a victim of a Ransomware infection called Peta. The threat you are faced with is also known as cryptovirus and, in the next lines, we are going to assist you in better understanding how this infection operates, and how you can remove it in the best possible way. If you stay with us, you will find a helpful removal guide at the end of the article with instructions on how to clean your system from this malware. We will also share some alternatives that you can use to restore some of your encrypted records, as well as some useful prevention and protection tips.
The .Peta virus
The .Peta virus drops a _readme.txt in the users’ folders, as seen in the picture below. It encrypts folders one by one, so if you see it, is is possible to stop the .Peta virus in its tracks by shutting down the machine.
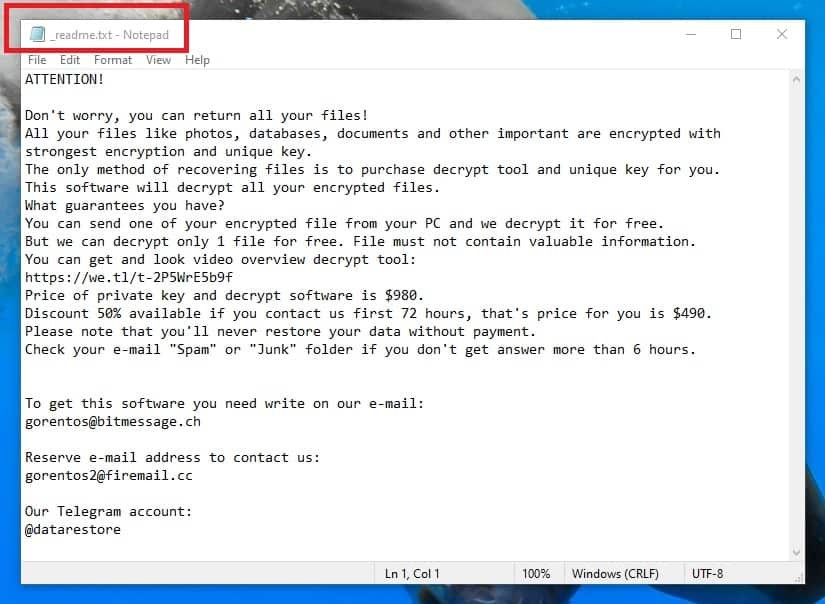
The readme.txt .Peta drops on victims’ desktops.
If you are faced with a Ransomware for the first time, you should understand that this is one of the web’s most malicious threats. We don’t want to scare you right from the beginning, but knowing what you have to deal with is the first step to get the problem resolved. Unlike other online threats, such as viruses, Trojan Horses, Worms, Spyware, etc., which can steal your information, damage your software, or hack the entire OS, an infection like Peta will not, in any way, damage, delete or corrupt your files, or your machine. Instead, it would apply encryption to your most valuable information, with the goal of blackmailing you. This particular malware uses a very powerful, and complicated algorithm of symbols to convert all the files on the infected device into unreadable pieces of data. After the encryption is applied to them, the files cannot be opened or used without the application of a unique, and secret decryption key. We should mention, though, that all the data is still present on the hard drive of the system, and it is not damaged. However, the files’ extensions are likely to get replaced by some unrecognizable ones, which no software can read. The Ransomware creators use this encrypted information as leverage, that allows them to blackmail their victims. They request a ransom from the victims in return for the special decryption key, which they hold in their servers. If the users want to access their files again, they are prompted to make an immediate payment to a given cryptocurrency wallet.
The .Peta file encryption
.Peta’s files appear only once the encryption is complete. They are easily discernible from normal extension by the “double” extension they have (see the picture below).
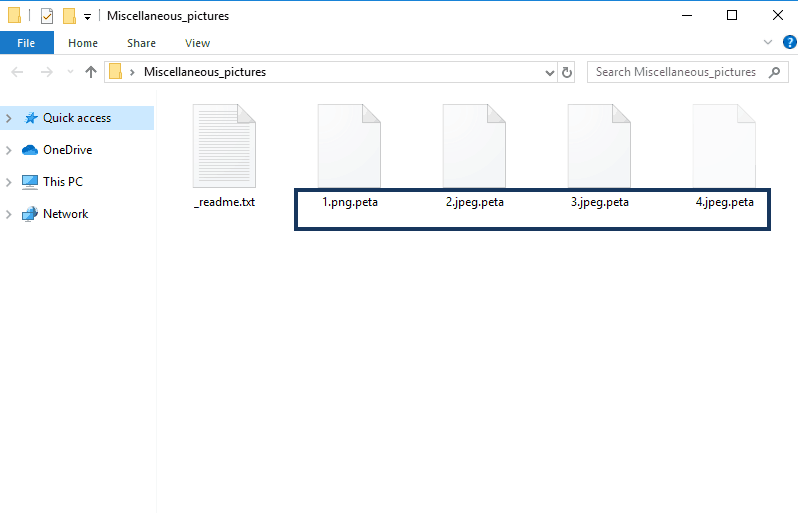
The .Peta virus as seen by the encryption.
The security experts recommend that the victims of Ransomware always look for alternatives means of restoring their information before resorting to the ransom. The reason is because, the more people agree to pay, the more common this type of Internet money extortion would become among the crooks, and they will continue to develop and spread more Ransomware infections with the aim of extorting more money. That’s why our suggestion is that you first check for some other methods which may help you avoid giving your hard-earned money to the hackers. For instance, you can take a look at our list of free decryptors, or go through our tips on how to get back some of your files from system backups. You can find those instructions in the second part of the removal guide below, but before you give them a try, make sure you remove Peta first, by completing the following removal steps. This is important in order to gain control over your device, and stop the hackers from exploiting it for their malicious actions.
SUMMARY:
| Name | Peta |
| Type | Ransomware |
| Detection Tool |
Peta Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

None of those methods in your guide decrypt the .peta files
Hello guys I am suffering with .Peta virus after formating my systems still my files are encrypted pls help me what to do with this?