The Phoenix ransomware
Phoenix ransomware is a virus program that infects Windows computers with the aim to make their users pay a ransom to release the files that it has locked. Phoenix ransomware stealthily encrypts the user’s data to make it inaccessible without showing any symptoms.
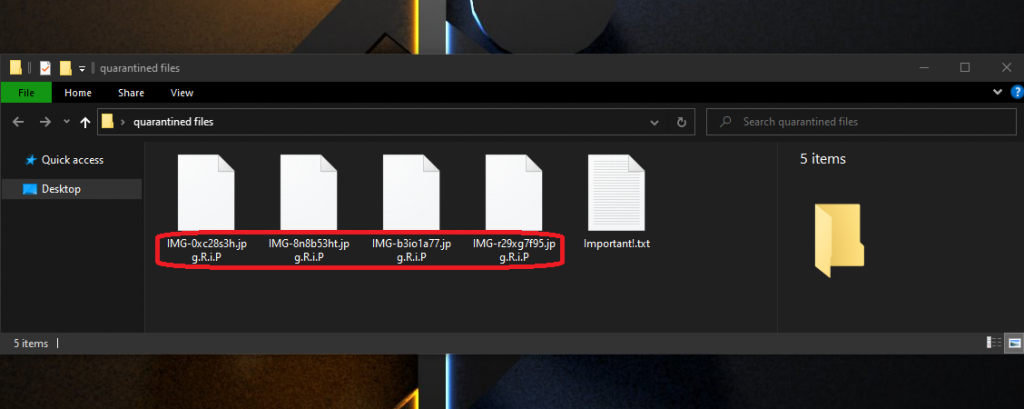
The Phoenix Ransomware will encrypt your files with the .R.I.P extension.
The threats of the Ransomware family are computer infections created for the sole purpose of blackmailing the attacked users by blocking the access to their most important data files. A typical Ransomware threat wouldn’t put your computer system in any danger as this isn’t its target. In general, the Ransomware infections don’t cause any actual damage. Even the files they target remain intact – it’s just that the user’s access to them gets restricted until they pay the requested ransom. Now, this may not seem like a very serious problem, especially to someone who doesn’t hold any overly valuable data in their computer, or to someone who has extensive backups of their valuable files. However, it seems that there are quite a lot of people who do have sensitive documents in their machines but have no backups for them. This is exactly the scenario in which a Ransomware attack can be particularly devastating. Many people have lost their life’s work or years worth of research and study due to one single attack by a Ransomware cryptovirus. If you are in a similar situation and there doesn’t seem to be anything that you can do to fix the problem, be sure to stay with us to learn more about your possible options.
The Phoenix virus is a form of Ransomware that takes its victims’ files hostage by encrypting them. The Phoenix ransomware’s goal is to get the user to pay the hackers a certain amount of money in exchange for the locked data’s release.
Of course, the hackers behind this threat offer their victims a way out of their unpleasant situation. They are given the option to pay for the decryption key for their files. However, such a payment isn’t affordable to everyone and, what’s even worse, even those who pay aren’t guaranteed that they would be give the decryption key. There are countless examples of people who have not been give any decryption solution even after having paid. That is why the payment option should really not be your first choice of action.
The Phoenix file extension
The Phoenix file extension is a unique series of symbols that replaces the regular extension suffix of the files that Phoenix ransomware encrypts. The Phoenix file extension cannot be removed manually and would only go away after the files get decrypted using the corresponding key.
Our advice for all of our readers who have had their data sealed by Phoenix ransomware is to first try to remove the malware using the instructions below and then, once the malware is gone, to explore the second part of the guide where they will find some alternative recovery suggestions which may help recover some of the locked-up data.
SUMMARY:
| Name | Phoenix ransomware |
| Type | Ransomware |
| Data Recovery Tool | Not Available |
| Detection Tool |
Phoenix Ransomware Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Phoenix ransomware files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment