Place-web.com
Place-web.com is an aggressive ad-displaying and page-redirecting app that researchers label as a browser hijacker. Upon installation, Place-web.com attaches itself to the main browser in the system and begins to make changes to its toolbar, search engine, and homepage settings.
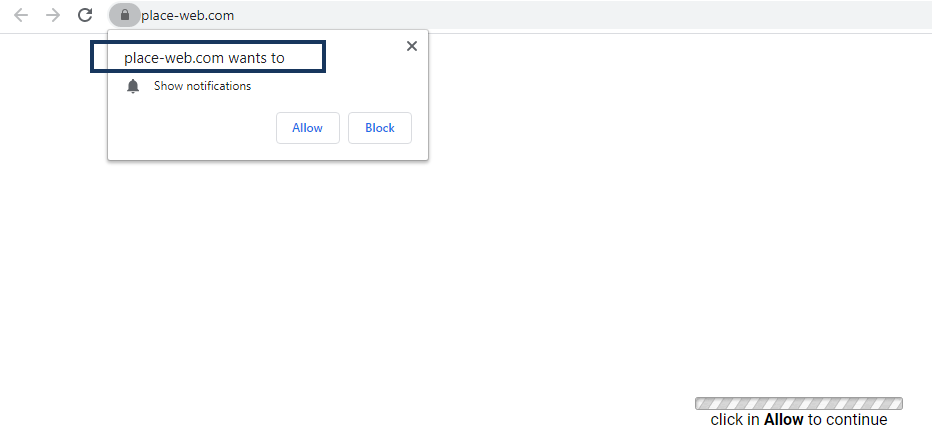
The Place-web.com Virus will display pop up ads and messages
Potentially unwanted apps like Place-web.com are very common and even though they aren’t as dangerous as Spyware, Trojan horses, or Ransomware, they are still better kept away from your computer. Since you are reading our article on Place-web.com, it is likely that you have already had this browser hijacker installed in your Edge, Firefox, or Chrome (or another) browser and are now trying to find more information about this unpleasant app. If that is the case, you should read the next lines in order to learn more about the abilities of Place-web.com and also about the way you can uninstall it from your computer. If you cannot wait to remove this browser hijacker, you can directly scroll down to the removal guide and follow its instructions to make the hijacker go away. However, it is still advisable that you also read the article itself to inform yourself about the characteristics of this undesirable app so that you know exactly what you have on your hands.
The Place-web.com Virus
The Place-web.com Virus is a piece of software that can change and modify the settings of a web browser without the user’s approval. Majority of people believe that Place-web.com is a virus or malware because it can the homepage or replace the default search engine without a warning and redirect the web searches to sites full of aggressive ads.
The main goal of most apps that belong to this software family is to promote and popularize different products and sites. They are able to do that by inserting themselves inside the users’ browsers and taking over their settings. Once in the browser, the hijacker would make different changes in it, such as the ones mentioned above, which would allow it to then display aggressive ads on the computer’s screen and to automatically redirect the user’s browsing to the sites that sponsor the hijacker.
For most users, the irritation alone that is caused by these advertising activities is enough to make them seek ways to uninstall the intrusive app. However, even if you can put up with the sudden page redirects and the obstructive advertisements, it is still best for the overall safety of your PC to get the browser hijacker removed.
How can Place-web.com compromise your computer’s safety?
In general, browser hijacker apps aren’t created to harm the computers they are installed on. As we said, the purpose of this kind of software is advertising, meaning that they don’t typically have any damaging abilities. However, since the ads that they show and the sites that they try to popularize may not always be reliable and safe, it is possible that your computer may get exposed to hazardous content such as phishing elements on scam pages, pirated software that contains hidden Trojans, and even Ransomware file-encrypting viruses that can lock up all of your most important files and keep them that way until you send some money to the hackers behind the virus. All in all, having such unwanted and unreliable ad-generating software on your computer is not good for the long-term safety of the machine so its best to use the instructions that we offer you to get rid of the intrusive hijacker app.
SUMMARY:
| Name | Place-web.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Place-web.com Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment