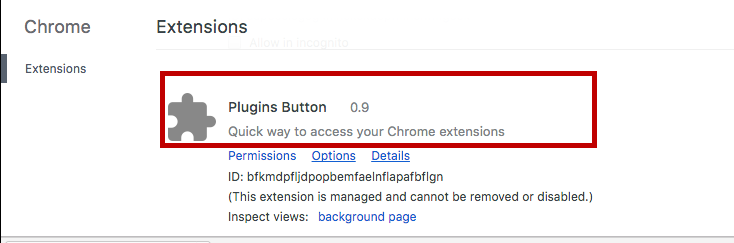
Plugins Button
An Adware program such as Plugins Button 0.9 is normally not something that you would want to have on your computer. The reason for that is the ability of Plugins Button 0.9 to get added to your Firefox, Chrome, IE or Edge browser as some sort of browser extension and start spamming it with all kinds of irritating ads or other promotional materials.
Once Plugins Button installs onto your system, it will start generating advertisements and you may even be redirected.
Usually,if a user gets Plugins Button 0.9 or some other Adware installed on their PC, it will not be long before they start noticing various banners, box-messages, pop-ups and even page redirects being generated inside their browser. Trying to close the ads manually by clicking on them is generally ineffective since even if one advert closes, more would soon appear to take its place. All in all, a pretty frustrating situation to be in. Luckily, here we can help you handle this issue by providing you with several simple steps that would take you no more than twenty minutes to complete. We have combined the Plugins Button 0.9 removal steps in a guide manual that you can find below. Go ahead and make use of the guide once you’ve finished reading the rest of this article’s paragraphs in order to uninstall the unpleasant software from your PC and ensure that it does not come back to bother you.
Plugins Button on Chrome
Usually, programs like Plugins Button 0.9 are used for earning money via a model called Pay-Per-Click. The ads displayed by the pesky software are made extra annoying in order to get users to click on them. Each click generates money for the Plugins Button 0.9’s developer and as long as the irritating software gets installed onto enough computers, the income gained from it should be quite sizable.
Of course, the regular user doesn’t benefit in any way from the intrusive ads, banners and pop-ups. Furthermore, most software that falls under the Adware category is actually rather useless or at least has very limited functionality. There are examples of when a program of this type might actually provide the customer with some actual useful feature but those instances are a rarity. The majority of Adware applications normally cause more problems that they solve, which is why removing them is the recommended way to go.
Why your PC might be at risk
Most programs like Plugins Button 0.9 aren’t harmful on their own. Despite their intrusiveness and unpleasant behavior, they are different from PC viruses like Trojan horses, Spyware, Worms or the infamous Ransomware. However, due to the fact that most Adware applications tend to execute tasks without being allowed to do so by the user, one should always assume that such software could potentially represent a security hazard.
One thing that users who have Plugins Button 0.9 on their computer should bear in mind is the fact that the ads that get generated by the Adware could sometimes be unsafe. If you happen to click on the wrong ad, your browser might get redirected to some shady and potentially hazardous web address. Know that a lot of malicious viruses like Ransomware and Trojans use sketchy ads or obscure websites to get to people’s computers. Therefore, it is simply better to keep away from the irritating banners and adverts that Adware programs display or else you might be putting your system at risk.
Browser Monitoring
One other particularly unpleasant trait that some Adware programs possess is the ability to keep tabs on the user’s online activity and record the gathered browsing data. This is normally used as means of improving the “quality” of the ads by making them more relevant to the personal interests of the individual. However, one can never be hundred percent sure what happens with their personal data once it gets extracted by an Adware program. There are a lot of examples where Adware developers would sell the data to third parties thus gaining additional profit from it. All in all, if you don’t want some sketchy software monitoring your activities on the Internet, you should probably not allow any Adware programs to remain installed on your PC.
Installation of Adware
If you want to prevent any unwanted applications like Plugins Button from getting installed on your machine, you have to make sure to be careful when surfing the Internet. There are a lot of different methods used for the distribution and installation of Adware. One very commonly used technique for spreading such unpleasant applications are the mandatory spam e-mails or spam social network messages, another method is the use of various forms of social engineering such as misleading Internet offers or deceptive online ads similar to those displayed by the Adware itself. Fake error warnings in your browser that directly tell you to download the unwanted program by making you think that it will actually resolve the error are also possible. File bundles where the Adware is added to another program’s setup file and gets installed along with the other piece of software are also frequently used. Be very careful when installing new programs on your PC and always try to determine whether there are any optional installs. If a program that you want to install has any additional applications bundled with it that seem potentially unwanted, do not forget to leave them out before launching the installation process.
SUMMARY:
| Name | Plugins Button |
| Type | Adware |
| Detection Tool |
Remove Plugins Button 0.9 from Chrome
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment