PonyFinal
PonyFinal is a ransomware infection that launches a stealthy file-encrypting process on the contaminated computer and makes the found files inaccessible. After the encryption process is finished, PonyFinal places a text notification on the screen and requests a ransom payment to decrypt the encrypted files.
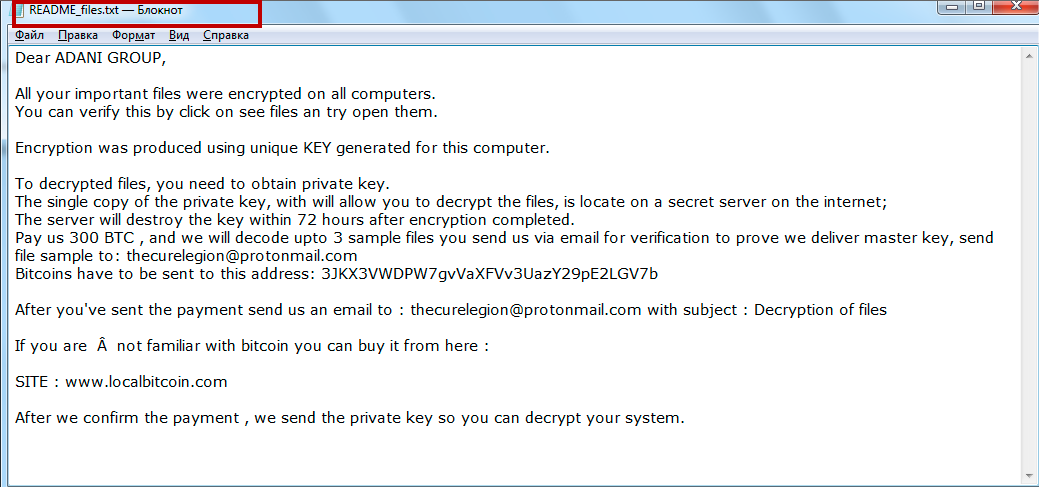
The PonyFinal Ransomware will encrypt your files and leave a README_files.txt file when it is done.
Usually, as soon as your computer has been compromised, PonyFinal can start encrypting your information without showing any visible symptoms of the process. The main problem with this ransomware is that its attack can result in a substantial loss of data, particularly if you store files with high importance on the infected computer.
On this page, however, we will talk about the alternative methods that the victims of PonyFinal can use in order to neutralize or at least to minimize the effect of the attack to some extent. That’s why, if you are seeking for other solutions to recover your files and to remove this nasty cryptovirus from your computer, take a look at the removal guide below and the suggested file-recovery options listed there. In the next paragraphs, we will also discuss ways of avoiding future encryption of new or recovered files and methods for system protection and prevention of potential attacks.
The PonyFinal Ransomware
The PonyFinal ransomware is a malicious piece of software that restricts users from access to the digital files they store on their computer. To regain access, the victims of the PonyFinal ransomware are required to pay a ransom for a file-decryption key.
PonyFinal can encrypt a variety of file types including images, text files, videos, audio files, archives, databases and more and turn them into unreadable bits of information that is kept unavailable or inaccessible until a ransom is paid for its decryption key. Basically, this malware seeks to blackmail the victims to send the hackers some money in order to obtain a decryption key from them. The crooks behind the ransomware typically give an ultimatum to the victims and demand a fixed sum, normally requested in Bitcoin or another cryptocurrency.
The PonyFinal file recovery
The PonyFinal file recovery is possible if the victims have copies of their encrypted files. Another possible way for the PonyFinal files to be accessed again is through the successful application of a decryption key.
Most users, however, often forget to create copies of their important files as frequently as they should. That’s why threats like PonyFinal may happen to encrypt vital data which the victims have no backups of. In this scenario, the only way to potentially undo the applied encryption is by applying a specially generated decryption key. However, no one can say whether such a key really exists or not.
The criminals behind PonyFinal promise that, once you transfer the ransom amount to their account, they will send you this mysterious key. There is no guarantee that you will actually get anything from them, though. This is why we do not typically advise ransomware victims to transfer money to the hackers, because it can only get worse if they fade away with the money. Instead, our suggestion is to figure out how to remove PonyFinal form your computer (for instructions, see the guide below) so you can later try some of the alternative file-recovery options.
SUMMARY:
| Name | PonyFinal |
| Type | Ransomware |
| Detection Tool |
Remove PonyFinal Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment