Postimg.cc
If you landed on this page, chances are that your trusty browser has mysteriously transformed into an unfamiliar entity. Probably you’ve encountered a rogue’s gallery of unwanted toolbars and add-ons, or your browsing sessions are now frequently being interrupted by random web pages that appear out of the blue without your interaction. If you’re nodding in agreement, it appears you’ve crossed paths with a Browser Hijacker program, and more precisely an intruder known as Postimg.cc. This potentially unwanted software gives itself away by altering your browser settings without needing your consent. However, fret not, for the following sections will explain about what exactly Postimg.cc is and guide you towards its removal.
Postimg.cc is a Browser hijacker that does not pose a direct danger to your system but it has the capacity to cause significant browsing discomfort. For instance, it can weak your browser settings, redirect your searches, interrupt you with a stream of intrusive ads, and monitor your online activity. These actions may pose considerable risks to your online privacy, as they may expose you to potentially unsafe websites, and significantly degrade your browsing experience.
Postimg.cc Virus
Considering the disruptive behavior of Postimg.cc, it’s understandable that you might perceive it as a virus, a misconception shared by many. Hundreds of users refer to this hijacker as the “Postimg.cc virus”. However, this classification lacks precision because, unlike a traditional virus, capable of inflicting serious harm on your system, the so-called “Postimg.cc virus” is primarily a source of irritation, not a direct threat. It won’t corrupt your files, nor will it infect other devices or zombify your computer to join a botnet. That being said, its presence on the system, and especially its randomly generated pop-up ads and links could potentially provide a gateway for more severe threats like Ransomware or Trojans.
What is Postimg.cc?
Browser Hijackers such as Postimg.cc, g3news.biz or My Captcha Space are programs, designed to operate as advertising tools. They frequently sneak in with free software downloads or get distributed along with some other programs that promote themselves as useful and appealing. In their essence, such pieces of software are programmed take over your web browser, dictate what search results appear in your search engine, alter your homepage, and redirect your web searches towards specific sponsored websites. The rationale behind this intrusive activity is the relentless pursuit of revenue from pay-per-click and pay-per-view remuneration models. This explains why, once Postimg.cc nests itself within your system, you can expect an avalanche of notifications vying that won’t go away unless you click on them.
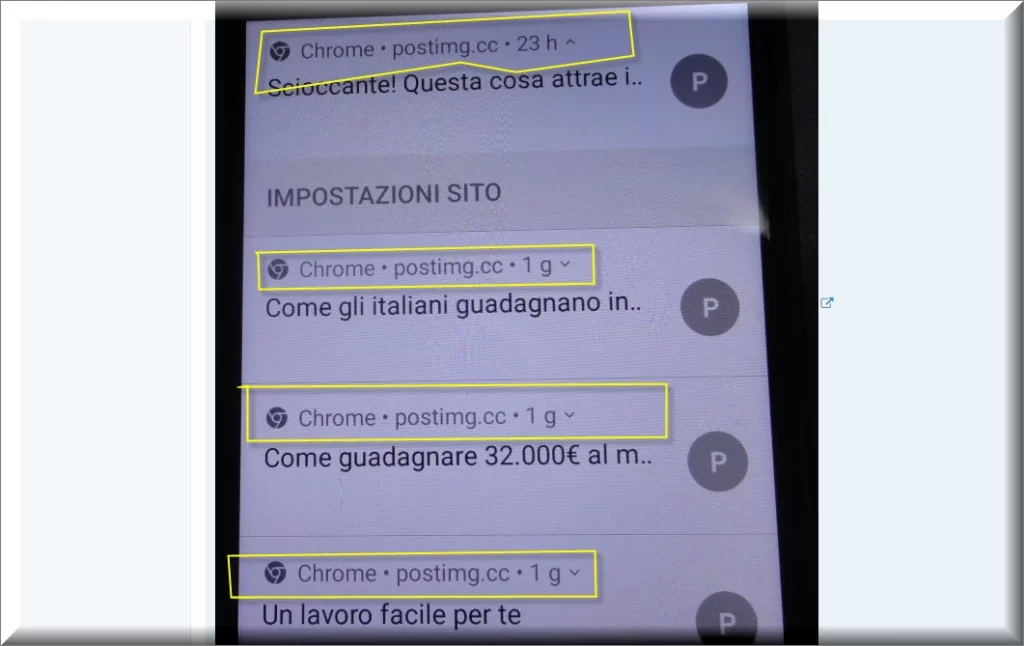
Postimg.cc Pop-ups
What Postimg.cc is typically known for, is the pop-up ads it generates during your browsing sessions. While some users may dismiss them as minor irritants, others may find them extremely hard-to-ignore, and even dangerous. That is because, as a matter of fact, the internet isn’t as safe as it seems. The online environment teems with dubious ads, deceptive links, and sites infested with viruses. Thus, when you are faced with a bunch of random Postimg.cc pop-ups and notifications, it is best to exercise caution and avoid interaction. Moreover, nobody guarantees that the Postimg.cc pop-ups that you see are legitimate. Among the regular notifications, there could be ads designed by criminals to deceive you into installing additional unwanted software or expose you to harmful content.
Postimg.cc on Chrome
If your Google Chrome is exhibiting signs of browser hijacking, such as an unwanted change of your homepage, search results that are irrelevant to your searchers, or a sudden appearance of toolbars that you can’t remember installing, it’s highly likely that Postimg.cc has attached itself on your Chrome. Regrettably, addressing the problem of Postimg.cc on Chrome isn’t as straightforward as a simple browser reset, and an ad-blocker, though helpful, is not an effective solution. The Browser Hijacker has the ability to nest itself deep in the system and alter Chrome’s settings to manipulate your browsing experience and redirect you to specific sites and ads. That’s why, to remove Postimg.cc on Chrome and reclaim your browser, you need to use a thorough guide and trustworthy security software.
Postimg.cc
Frequent, unauthorized redirects to the Postimg.cc website is a telltale sign of the Browser Hijacker’s firm grip on your system. The unwanted software manipulates your browser, forcing it to load the Postimg.cc.com site repeatedly without you doing nothing. This website, despite its seemingly legitimate facade, is a revenue-generating page, brimming with sponsored content and crafted to earn pay-per-click revenue by increasing its traffic. The moment Postimg.cc gets installed on your system, you start to experience those automatic redirects to the sponsored page and become part of the revenue-generating scheme. Fortunately, you can regain the control of your browser and put an end to these unwelcome redirects by removing the hijacker from your system.
SUMMARY:
How to Remove Postimg.cc
To try and remove Postimg.cc quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Postimg.cc extension (as well as any other unfamiliar ones).
- Remove Postimg.cc by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Postimg.cc and any other suspicious items.
If this does not work as described please follow our more detailed Postimg.cc removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Postimg.cc app and kill its processes
Uninstall the Postimg.cc app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Postimg.cc. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Postimg.cc, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Postimg.cc.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Postimg.cc changes made to different system settings
Undo Postimg.cc changes made to different system settings
It’s possible that Postimg.cc has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Postimg.cc from your browsers
Remove Postimg.cc from your browsers
- Delete Postimg.cc from Chrome
- Delete Postimg.cc from Firefox
- Delete Postimg.cc from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
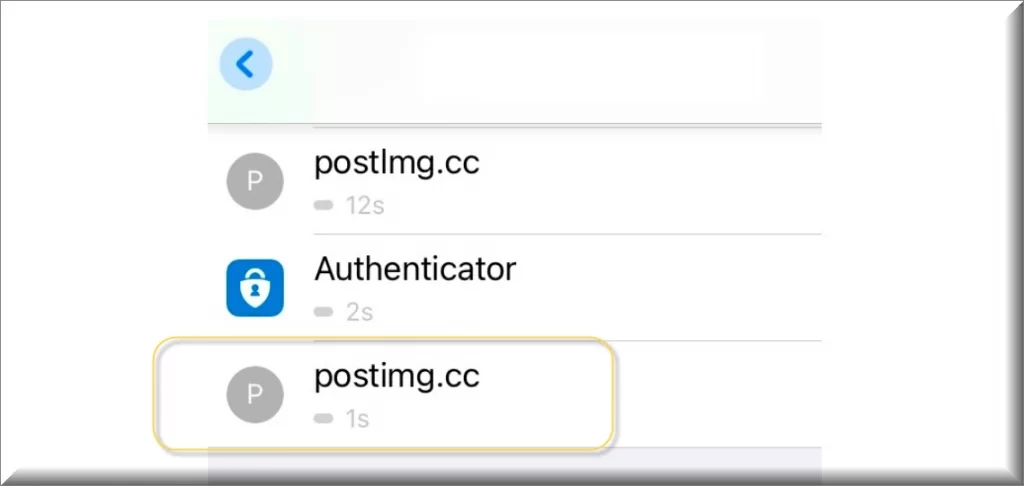
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.


Leave a Comment