Presenoker
Presenoker is a malware program that gets detected by Windows Defender on computers that have BitTorrent or uTorrent installed on them. Presenoker is categorized as a Trojan Horse virus and can result in unusual browser behavior, installation of unwanted software, and unwanted browser changes.
If Windows Defender on your computer has detected Presenoker, this may not always mean that you are dealing with an actual malware infection of the system. As we said, it seems that the presence of certain versions of uTorrent and BitTorrent on the computer could trigger Presenoker warnings from Windows Defender without the Trojan actually being in the system. There’s probably a certain file or files that those two torrenting programs create when they get installed that Windows Defender flags as potential threats and labels them as Presenoker. However, it’s obviously still possible that the warning from Windows may not be a false positive and that you may indeed have the Presenoker Trojan in your system. Therefore, if you see the warning message on your screen, you’d better take the necessary precautions to check your system for malware and delete anything that may be a potential threat to the computer.
Pua:win32/presenoker
PUA:win32/presenoker is a Windows Defender warning designed to notify you about potentially unwanted and/or dangerous software in the system. The PUA:win32/presenoker warning doesn’t always mean your computer is under attack but also shouldn’t be ignored if it appears.
PUA stands for Potentially Unwanted Application and programs such as BitTorrent and uTorrent (or elements of those programs) are sometimes flagged as potentially unwanted by Windows Defender and other security tools. This is actually understandable seeing as how certain versions of those programs may attempt to introduce browser changes or show obstructive ads on your screen.
It is unclear which exact versions of uTorrent and BitTorrent trigger the PUA:win32/presenoker warning but if you have either of these programs and Windows Defender notifies you about the presence of unwanted software in the system, chances are that it is referring to those programs.
Presenoker – what is it?
Presenoker is a Trojan Horse component that’s typically bundled with torrent programs like BitTorrent and uTorrent. Windows Defender might flag BitDefender and uTorrent as unwanted because they might add the Presenoker Trojan to your system, in which case you should make sure to remove it.
If this warning gets shown on your screen, there’s no reason to get panicked because your system is likely not in any immediate danger. The Presenoker Trojan is not the most dangerous representative of the Trojan Horse category and though it may try to make some browser changes and/or spam you with ads, that is probably not going to bring about any direct harm to the system. One thing you should consider, though, is that it’s possible that Presenoker could end up making your system an easier target for more harmful threats – other (more aggressive) Trojans, Spyware, Ransomware, etc. By displaying ads and making unauthorized browser changes, Presenoker could decrease the security of your PC, thus exposing it to the aforementioned types of malware. Because of this, it is better to delete it from your computer. Usually, Windows Defender should be able to take care of it but to help you make sure that the Presenoker is truly gone from your computer, we suggest following the guide provided down below.
Presenoker virus
The Presenoker virus is a malware component that sometimes gets detected in BitTorrent and uTorrent by Windows Defender. The Presenoker virus is usually not damaging to the system, but it shouldn’t be allowed to stay as it might be exploited by actual threats.
Thus far, the main complaints that users have about Presenoker is that it messes with the settings of the browser, installs hijacker extensions, spams the screen with ads, and displays other similar forms of intrusive behavior. Unlike other Trojans, Presenoker doesn’t target the system trying to damage it and/or the files that are saved in it. The problem, though, is that the changes that it may make in the browsers or the system could significantly decrease the security of your computer both directly and indirectly. One example of that is the fact that some of the ads this software may show on your screen may not be what they seem and may actually serve as redirects to less-than-reliable sites where Spyware, Ransomware, and other dangerous viruses may lurk. Considering this, it really is better to take the matters into your own hands and eliminate Presenoker.
Since uTorrent, BitTorrent, and other similar programs seem to sometimes carry Presenoker (or at least data that gets detected as Presenoker by Windows Defender), it seems that uninstalling those programs could help remove the Trojan. However, if you have either of those programs on your PC, you probably use them and would like to keep them. Fortunately, it may be possible to get rid of Presenoker without actually deleting your torrenting program. The way to do this is shown in the guide below, and we suggest you follow it to secure your computer and eliminate the unwanted Trojan Horse.
SUMMARY:
| Name | Presenoker |
| Type | Trojan |
| Detection Tool |
Presenoker Removal
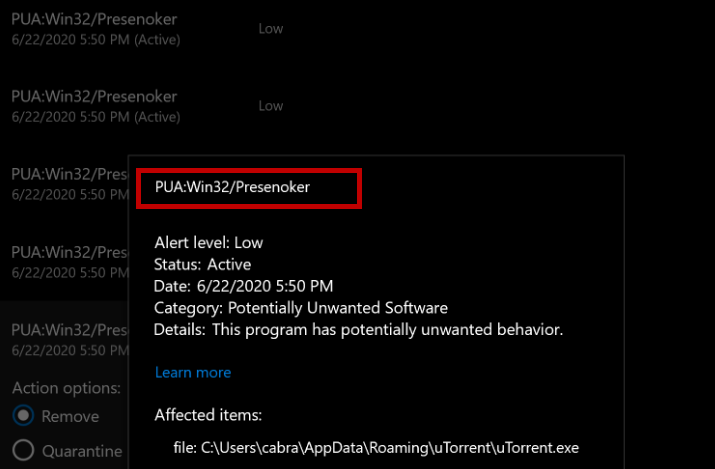
To remove Presenoker, you should first try using the help of Windows Defender.
- If the Windows Defender Presenoker warning appears on your screen, write down the location of the malware file shown in the warning message
- Select Remove from the Action Options.
- Click on Start Actions – Windows Defender will remove Presenoker.
- Restart your computer and go to the location that you wrote down to check if the malicious file(s) is gone.
If after you do this the Windows Defender warnings stop, there won’t be a need to try anything else because Presenoker is probably no longer in the system. However, it is highly likely that this won’t be enough to fully clean your computer. For starters, the Presenoker file might return after you restart your computer. Also, if the Trojan has made changes in the system and your browsers, you will have to revoke said changes manually because Windows Defender might not be able to help you with them. In either of those cases, you should follow the more advanced steps shown below to make sure that nothing related to Presenoker is left in the system.
Advanced Removal
Step 1: Check the processes in the Task Manager
- Press the Ctrl, Shift, and Esc keys from your keyboard to open the Task Manager, and access Processes.
- Look for a process labeled Presenoker or something similar and if you see it there, right-click on it, select Open File Location.

- Select the Presenoker process and then click on the End Process button (bottom-right).
- Go back to the File Location and delete the entire folder with all the files that are in it.
- If there isn’t a process labeled Presenoker, look for other items that have unusual and unfamiliar names and that consume large portions of your system’s resources (CPU and RAM).
- If you single out a suspicious process, open your browser and look up its name to gather more information.
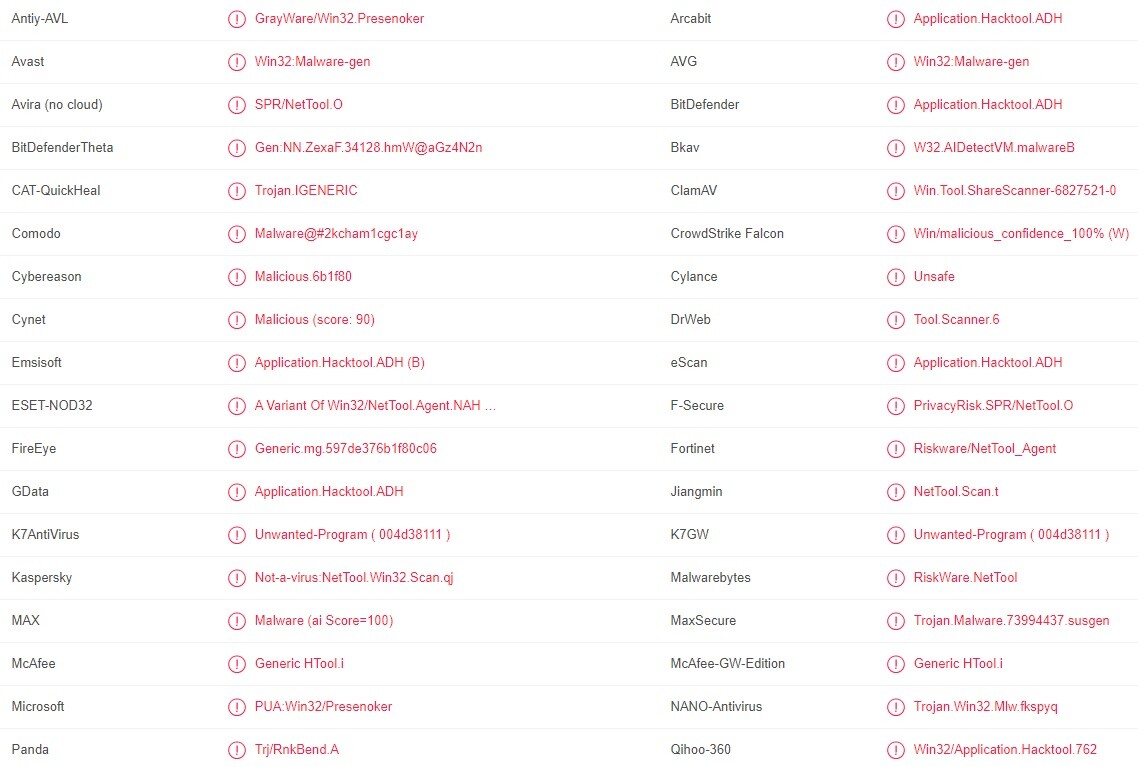
- If your online research reveals that this process may be linked to Presenoker, open the process’ file location and scan the files in it with the following free online scanner:Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is free and will always remain free for our website's users.This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.Drag and Drop File Here To Scan
 Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared. - If malware is detected in any of the files, quit the suspected process and then go back to the location folder and delete it.

If any of the files in the location folder cannot be deleted for some reason, delete what files you can and move on to the next step. After everything else from this guide has been completed, you should be able to delete the remaining files alongside the location folder itself so be sure to do this once you are finished with the rest of the guide.
Step 2: Put your PC in Safe Mode
Safe Mode is important as it helps you prevent unwanted and problematic programs from hindering your troubleshooting attempts, so we suggest getting into Safe Mode before you continue. The link we’ve provided will redirect you to separate “how to enter Safe Mode” instructions in case you need help with that.
Step 3: Clean your Hosts file
Every Windows PC has a file called Hosts that is often targeted and modified by malware and unwanted software as this allows the undesirable/malicious programs to gain persistence in the system. Therefore, you should check that file and clean it from any unwanted modifications that Presenoker may have made in it.
- Place this file location in the Start Menu and hit Enter to open the Hosts file: notepad %windir%/system32/Drivers/etc/hosts.
- See if there are any IPs at the bottom of the text in the Hosts file – right below Localhost.
- If there are any lines of text there or any strange IP addresses, copy them and paste them in the comments below this post.
- Since not every time the Hosts file gets modified it is done by a malware or by another unwanted program, we must first take a look at the IPs you’ve sent us before we can confirm that they are from the Trojan.
- We will reply to you once we take a look at your comment and if we tell you the IPs are from Presenoker, you will have to delete them from the file.
- Lastly, press Ctrl + S after you delete the IPs to apply and save the change you’ve made in the file.
Step 4: Refresh the DNS Settings
To control your browser behavior, Presenoker might make changes to your computer’s DNS settings, so you should check those too and revoke any unwanted changes that may have been introduced to them.
- Type view network connections in the Start Menu and open the first icon.
- Right-click with the mouse on the icon of the network you are currently using (the one that doesn’t have an X next to its icon) and go to Properties.
- In the Properties window, select the Internet Protocol Version 4 (TCP/IPv4) item and the click on Properties.
- Make sure that the Obtain an IP address automatically option is checked and select Advanced.
- Go to the DNS tab and if there are any items shown in the list of DNS server addresses, remove them.
- Click on OK on every currently open window.

Step 5: Clean the Registry
You must now delete items related to Presenoker from your computer’s Registry but since there are many important settings related to the OS stored in there, you must be very careful with what you are deleting. If you are unsure if a certain item is linked to the Trojan and thus needs to be removed, always first consult us through the comments before you proceed with the deletion in order to avoid removing something that you shouldn’t.
- Type regedit.exe in the Start Menu and click on the first result that gets found.
- Click on Yes when Windows requests your Admin permission to open the Registry Editor.
- Once the Registry Editor opens, select Edit from the top and then select Find.
- Type Presenoker and hit Enter to start the search and if an item is found, select it, press Del, and then click on Yes to delete the item.

- Perform the same search, delete the next found item, and keep repeating this process until there are no more Presenoker items left in the Registry.
- Lastly, go to the next three directories in the Registry Editor by manually navigating to them in the left sidebar:
- HKEY_CURRENT_USER/Software
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
- Look in them for folders with names that seem unusual – for instance, a name that is much longer than the others and that seems to consist of random letters or numbers.
- Remember, if you are not sure about whether a given item should be deleted, ask us in the comments about it.
- Delete any such suspicious-looking items that you may find in those directories.
Step 6: Clean your browsers
In some cases, Presenoker may make changes in the browser and/or install unwanted extensions in it that can obstruct your browsing experience and even expose you to potential threats. Therefore, you should make sure to delete any such extensions from all your browsers and also refresh the browsers’ settings.
Deleting browser extensions is very similar for most browsers so below you can see a generalized guide on how you can do that:
- Start the browsers and select its menu (for most browsers it is an icon located in the top-right corner of the browser window, for Opera it is in the top-left).
- Select Extensions/Add-ons from the menu (if you are using Chrome, first select More Tools and then select Extensions).
- On the Extensions page, look for unfamiliar extensions that have been added to the browser without your permission and if you find any, Disable them and then Uninstall them (some unwanted extensions can’t be removed unless you disable them first).

- Lastly, visit this page and follow the instructions that are shown in it to refresh the settings of your browsers so that any changes made to them by Presenoker would get revoked.

You are amazing, only resolution here!!!