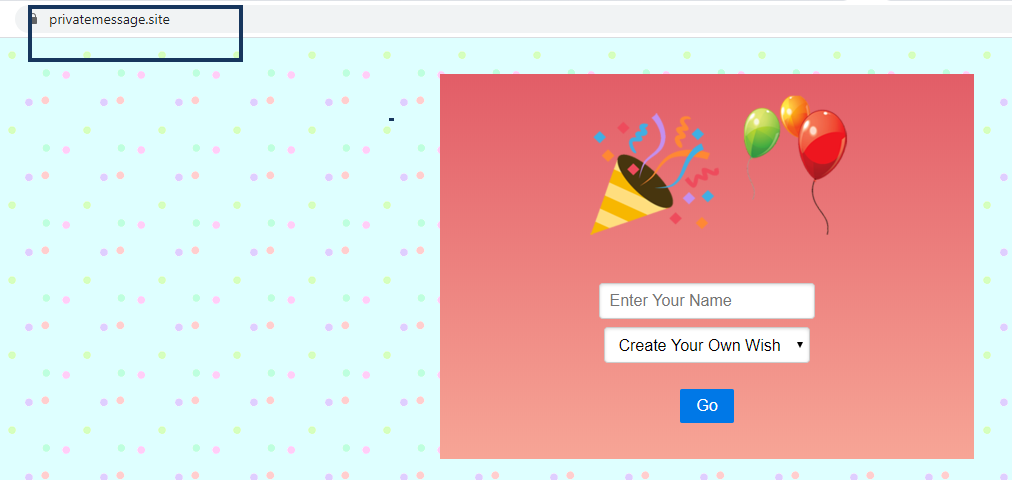
Privatemessage.site
Privatemessage.site is a page-redirect/browser hijacker that may appear in your browser without your consent. Privatemessage.site claims to be compatible with Google Chrome, Internet Explorer, Mozilla Firefox and other browsers and promises to provide you with some sort of free functionality.However, what Privatemessage.site really does is, it usually hijacks your default browser by imposing certain changes to its homepage or search engine.
The Privatemessage.site virus will display pop up ads and messages
Shortly after these changes take place you may start seeing tens of different ads, pop-ups and banners all over your screen every time you open a new browsing session. What is more disturbing, though, is the fact that your searches may frequently get automatically redirected to specific sponsored web pages and unfamiliar web locations that you never intended to visit. How to stop this activity and remove the annoying ads is what we are going to talk about in the next lines. If you have landed on this page because you want to learn more about that and uninstall Privatemessage.site, we suggest you read the information below.
Privatemessage.site on WhatsApp
Privatemessage.site on WhatsApp advertises itself as an excellent tool that helps the web users to make their online experience safer and more satisfying. Yet, these claims seem quite dubious, because Privatemessage.site on WhatsApp acts as a typical browser hijacker.
You can never know whether they are safe or if they may open insecure web pages or content that may contain viruses. So, do not waste your time thinking that Privatemessage.site can provide you with reliable search results. Better take care of removing it instead. This way, you will save yourself from the ads annoyance and the possible encounter with threats such as Ransomware or Trojans.
Another reason to consider removing this browser hijacker is the fact that it may disclose your tracking activities, the IP address of your computer, your location, and other browsing-related details, which could be transmitted to third parties or used for aggressive online advertising campaigns. This is a common online marketing tactic, which helps the web advertisers learn more about your recent preferences and target you with their ads accordingly. Additionally, when you have Privatemessage.site on your computer, you may experience dubious research suggestions for updating or installing new software, and suggestions to subscribe to unfamiliar web pages and services. If you have started confronting such pages while browsing the web, make sure you do not provide your personal information to them as you never know whether they are legitimate or compromised by fraudsters.
The Privatemessage.site Virus
The Privatemessage.site virus tends to impose certain browsing modifications and to manipulate the users’ web searches. For instance, the Privatemessage.site virus may monitor all search queries and redirect the customer to pages that provide sponsored results and earn pay-per-click revenue for the hijacker’s creators.
If you are experiencing something similar, we would advise you not to trust the links and ads that may get displayed on your screen by this browser hijacker.
To protect yourself, we recommend that you install a trusted anti-malware program and adhere to the basic principles of safe browsing. In addition, you can get rid of the browser hijacker manually. Currently, our team has prepared Removal Instructions, which you can find just a few lines below. Still, if you find them too difficult to follow, we recommend you use the professional Privatemessage.site removal tool that we have posted on this page. It can easily detect this and any other potentially unwanted program and uninstall it without any risk.
Preventing the hijacking of your browser
The majority of browser-hijackers claim to have official web pages, while their distribution methods oftentimes rely on a completely different means of getting installed onto user’s machines. Most of these suspicious programs are spread around the web through software packages (aka bundles), which allow them to get distributed inside the setups of popular free programs such as games, media players, download programs and other free software. Unfortunately, many users miss the ability to customize the installation of these packages by relying on the automatically selected installation settings (Default, Basic and Fast). To protect your computer, you should choose User or Advanced instead. These settings let you uncheck the unwanted add-ons and install only the software you want.
Removing the Privatemessage.site Virus from the system is just a matter of time!
Although the majority of security specialists will tell you that removing a browser hijacker like Privatemessage.site is difficult, we cannot agree with that. As far as the complexity and the level of danger are concerned, such applications do not come close to any sort of malware (Ransomware, Trojans, Spyware) or other dangerous viruses. Therefore, we believe that if you carefully follow the instructions given below, you will be able to safely remove the irritating page-redirect.
SUMMARY:
| Name | Privatemessage.site |
| Type | Browser Hijacker |
Privatemessage.site Removal
We are sending you to another page with a removal guide that is regularly updated to counter the latest tricks malware creators use. It will show you how to:
1. Locate and clean up your phone’s apps if they are infected.
2. Find browser extensions related to the threat and how to remove them.
3. Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment