ProLock
ProLock is a new and advanced version of the Ransomware virus category – a type of malware known for blocking important user files. ProLock employs a complex encryption algorithm through which it is able to make all targeted files inaccessible via conventional means.
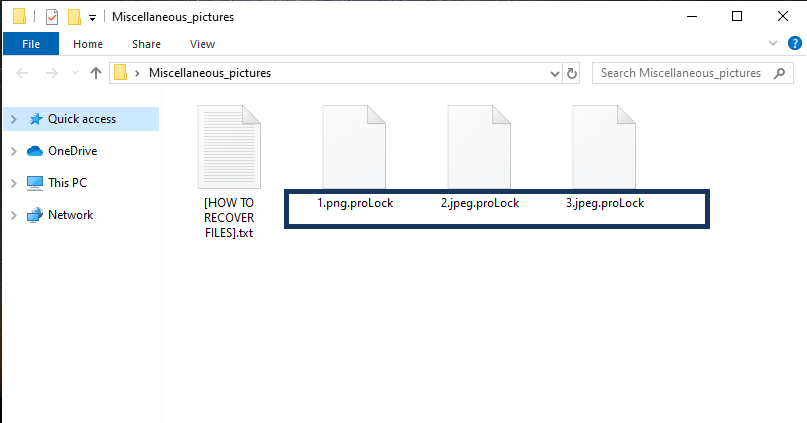
The ProLock virus will encrypt your files and leave a message in a [HOW TO RECOVER FILES].txt file.
The goal of this virus isn’t to harm the files or to steal them but to keep them locked until the user gives in to the hacker’s demands. Those demands, of course, are the payment of a certain amount of money to the criminals. According to a note that the Ransomware puts on the Desktop once it completes the encryption, the victim is supposed to send a certain amount of money in Bitcoins to the hackers’ online wallet. If the payment is made, the blackmailers promise to send their victim a unique access key that can be used to make the encrypted files available once again.
The ProLock virus
The ProLock virus is an extortionist type of malware that places the user’s files under lockdown and uses this as blackmailing leverage. The ProLock virus informs the user that an access key would be provided to them if the ransom is paid.
Since the virus doesn’t damage the computer and doesn’t conduct any other harmful activities, if you can afford to lose the encrypted files because they aren’t of any significant importance to you, the attack of this malware shouldn’t be a particularly serious issue. As far as the virus itself is concerned, it can be removed from the computer to prevent more unwanted encryption in the future. We will even give you a guide on how to do that. However, since the removal of the infection doesn’t automatically make the encrypted files accessible again if any of those files are important to you and you don’t have backups of them from where you can restore them, then you will need to take a careful look at your options and decide what to do next in order to minimize the harm caused by this malware.
The ProLock file decryption
The ProLock file decryption is the main method that is supposed to release your encrypted files. The ProLock file decryption, however, requires a unique key generated by the virus and that key is kept by the hackers, who want a ransom for it.
Of course, you pay the ransom, it is indeed possible that you will get that key and be able to restore your files. However, it is just as possible that the criminals trick you and only take the money without giving you the needed means to recover your data.
On the flip side, there may be other methods of restoring your files that do not require you to contact the hackers or to send them your money. Some of these alternatives will be explored in the second part of our removal guide. However, you will first need to ensure that the ProLock malware is removed from your computer so as to prevent the future encryption of any new files or of any files you may manage to recover. Also, bear in mind that the alternatives aren’t guaranteed to work in all cases. Nevertheless, it is still preferable to try them first, before you decide to try the ransom payment.
SUMMARY:
| Name | ProLock |
| Type | Ransomware |
| Detection Tool |
Remove ProLock Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment