The Proxyware platforms
Once again, threat actors are making use of legitimate platforms, this time the targets are proxyware solutions like Honeygain and Nanowire, to generate revenue by monetizing their malware operations.
The Honeygain app
According to Cisco Talos researchers, currently, there is malware that actively targets these internet-sharing platforms like Honeygain with the idea to monetize the internet bandwidth of victims.
As per the analysis that was published on Tuesday, internet-sharing apps are often abused in sophisticated malware attacks that include many attack stages and payloads, which provide cybercriminals numerous ways to profit.
These internet-sharing apps like Nanowire, often known as proxyware, are legal services that let users share a portion of their internet bandwidth with other devices, typically for a fee. The researchers said that such services are promoted to customers as a way to bypass geolocation checks on streaming or gaming platforms, and that they provide users with a way to earn money by offering up their bandwidth.
At the same time, as useful as this could be, the use of proxyware also allows threat actors to camouflage the source of their attacks, making it seem like the attacks are coming from valid home or corporate networks. Additionally, it makes conventional network defenses ineffective, since IP-based blocklists are rendered ineffective.
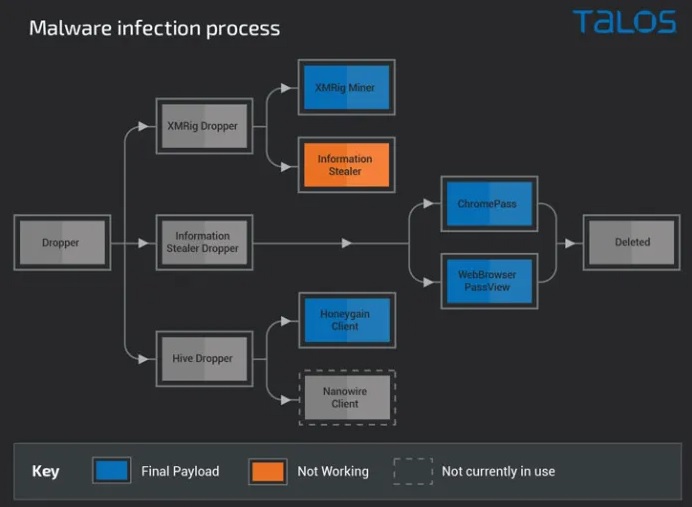
That’s not the end of it. Researchers discovered various methods used by malicious players, including Trojan proxys installers, which enable stealers and remote access trojans (RATs) to be steadily distributed without the awareness of victims. Cisco Talos discovered that some attackers were employing proxyware programs to earn money by utilizing their victims’ network bandwidth and CPU processing power to mine cryptocurrencies.
The analysis of some more cases has shown that attackers were using multi-stage tools that went beyond cryptojacking to also include the installation of info-stealers, cryptocurrency mining payloads, and proxyware software, which further broadens the varying approaches the criminals can choose from to monetize successful infections and steal sensitive data from their victims.
Even more worrying, during their analysis, the researchers found malware which was configured to install Honeygain in a stealthy manner on compromised machines, allowing the attackers to benefit from the victims’ internet bandwidth use. The fact that Honeygain accounts may be created and used by an attacker, implies that they can scale their operation by signing up for numerous accounts depending on the number of infected computers they control.
In relation to these revelations, the researchers concluded that users face two main problems coming from such proxyware platforms: resource abuse and blocking due to activities out of their control, both of which are the attacker’s responsibility and not the user’s.
Based on the published research, organizations who want to follow the best security standards are advised to ban the usage of these apps because of the numerous security concerns that are associated with them.

Leave a Comment