The PwnedPiper vulnerabilities
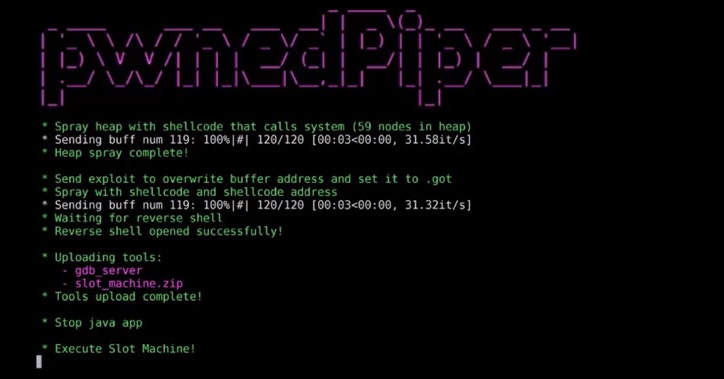
Nine major security flaws, referred to as “PwnedPiper,” were made public on Monday that exposed a widely-used pneumatic tube system (PTS) to a number of attacks, including complete takeover by malicious actors.
American cybersecurity company Armis revealed serious security vulnerabilities affecting the Translogic PTS system – a Swisslog Healthcare system that is used by more than 80% of all North American and 3,000+ other hospitals across the globe.
As per the information that has been published, a target hospital’s PTS network may be taken over by an unauthenticated attacker if its Translogic PTS stations are exposed. With such an unrestricted full access, a threat actor can easily perform sophisticated ransomware attacks, as well as collect critical medical information and make it available to other attackers.
Here is how the nine PwndPiper vulnerabilities are being tracked:
- CVE-2021-37161 – UDP receiver thread underflow.
- CVE-2021-37162 – SCC ProcessMsg Buffer overflow.
- CVE-2021-37163 – Two hardcoded passwords that are exposed via the Telnet server.
- CVE-2021-37164 – A stack overflow in tcpTxThread.
- CVE-2021-37165 – Overflow found in hmiProcessMsg.
- CVE-2021-37166 – GUI socket Denial of Service.
- CVE-2021-37167 – A user script that runs as root is vulnerable to being exploited for PE.
- CVE-2021-37160 – Unauthorized, unencrypted, unsigned firmware upgrade.
Internal logistics and transport solutions such as Pneumatic Tube Systems are commonly utilized to transport blood samples from hospitals to diagnostic labs, where these samples are stored.
As per what has been revealed, successful exploitation of the vulnerabilities may lead to very serious consequences such as leaking of sensitive information, data manipulation, and even a MitM attacks. Unauthorized access to the PTS network may allow attackers to infect it with ransomware and essentially shut down the hospital and its operations.
In brief, the nine flaws listed above concern privilege escalation, memory corruption, and denial-of-service attacks, which could be used to enable root access, achieve remote code execution, and allow attackers to gain persistence on compromised PTS stations.
To reduce the likelihood of exposure to any risks that may emerge in the real world as a result of possible real-world exploitation of system weaknesses, customers that use the Translogic PTS system are encouraged to upgrade to the latest Nexus Control Panel version 7.2.5.7 as soon as possible.

Leave a Comment