Pxj
Pxj is a ransomware threat that cybercriminals use to extort money from web users through the methods of file encryption. Pxj is a stealthy infection that can sneak inside a computer without being detected and can restrict access to valuable digital information without the owner’s knowledge.
Many fear the loss of access to files they hold in a computer, particularly those users who don’t normally maintain backups of their important documents on an external drive. A group of cyber criminals has found a way to make this a lucrative business by creating a malware called Pxj. This program is classified as a ransomware cryptovirus and its agenda is to secretly encrypt the files stored on a given computer and to ask a ransom to decrypt them. Pxj usually notifies its victims that they have been infected by displaying a terrifying ransom-demanding notification on their screen. The message includes payment guidelines and explains to them how to transfer some money to the hackers’ cryptowallet. The crooks promise to send the victims a decryption key for recovering their information if all their demands are met. However, security experts do not encourage the victims to risk their money by funding such a criminal scheme and focus on solutions that can remove the ransomware.
The Pxj Ransomware
The Pxj virus is a sophisticated ransomware infection that threatens web users to transfer money in order to liberate their files from a secretly applied file encryption. The Pxj virus is one of the most malicious programs to deal with and falls in the sub-category of the cryptoviruses.
Email attachments, spam messages, and links are a very common way of getting infected with a threat like Pxj. Some low-quality web pages, free downloads, and advertisements may also distribute infections of this type. It is important to mention, however, that Ransomware normally never comes by itself and usually takes advantage of some past device faults created by a Trojan horse or another malware that has already affected your computer. That’s why if you want to effectively remove Pxj, you will have to scan your entire machine to detect and delete the malicious code and to clear your device from other harmful infections.
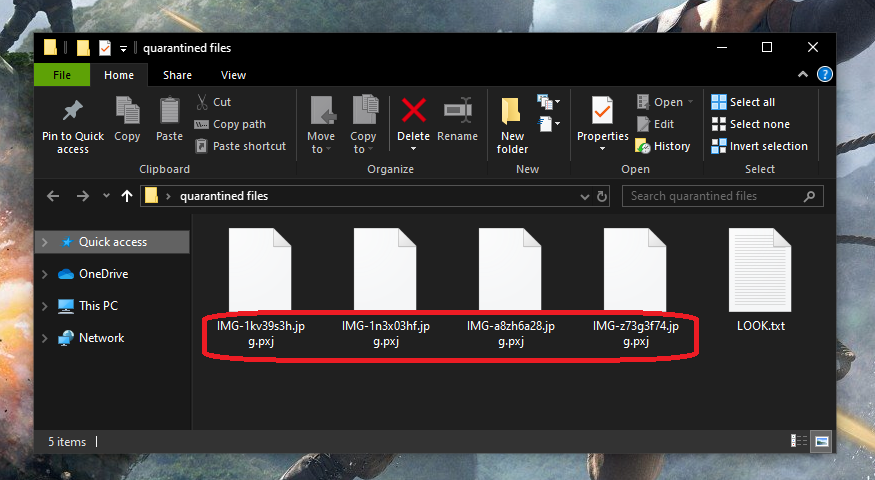
The Pxj file encryption
The Pxj file encryption is a process that converts user files into bits of data that no program can read or open. Once the Pxj file encryption is applied, it is basically impossible for the owners of the encrypted files to access them without applying a decryption key.
Essentially you don’t have to pay ransom to anybody if you have an external drive or cloud backup of your records. All you need to do is remove Pxj from your device using the guide below or run a full scan using a qualified removal tool. However, you may be in great trouble if you don’t have backups. Without a special decryption key, the Pxj encryption is almost unbreakable. Therefore, you might be willing to pay the ransom to get your files back if you really need them. However, that’s a bad idea, because there is no assurance that the hackers will really provide you with a decryption key. Besides, if you receive a key but it fails to reverse the encryption successfully, you will be left with no data and no money. Furthermore, your computer cannot be used normally unless the Ransomware is removed because any new files that you create or old files that you manage to recover will most probably get encrypted again. That’s why we suggest you to focus on the steps in the guide below and check out our file-recovery section which offers some suggestions for free data restoration.
SUMMARY:
Remove Pxj Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply