Pykw
Pykw is a ransomware infection that sneaks inside computers with the idea to encrypt the files stored there. After placing its encryption, Pykw demands a ransom payment from the owners of the files in order to provide them with a decryption key.
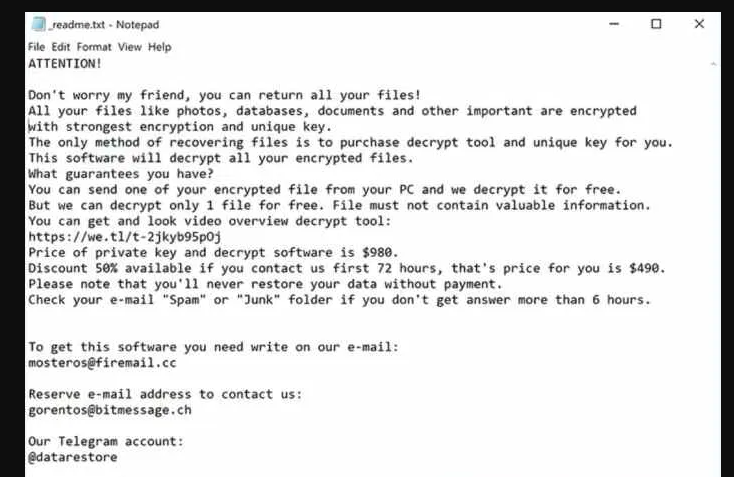
The Pykw Ransomware Note
The criminals who create ransomware threats like Pykw rely on different tactics in order to extort money from their victims. Normally, after the attack, the malware generates a scary notification on the screen of the infected computer and threatens the user whose files have been encrypted that if they don’t meet the ransom demands before a given deadline, they will not receive a decryption key and will never be able to access their information again. The crooks provide strict ransom payment instructions and typically require the payment to be made in Bitcoins or some other untraceable cryptocurrency in order to maintain their anonymity.
Unfortunately, the encryption code that keeps the targeted data inaccessible is practically unbreakable and there is no hope that any data will be retrieved without obtaining a special decryption key from the hackers. However, paying the ransom doesn’t guarantee that you will obtain one. Moreover, there are some alternative file recovery methods that may potentially help you minimize the consequences of the ransomware attack without sending money to anonymous criminals.
Perhaps you don’t even care about the encrypted files that much and you simply want to remove the infection from the computer so you can use it normally. Or you already have file backups (some files may be stored on other devices, in cloud storage, in your mail, external drive, etc.) that you want to safely copy to the clean machine. In all these cases, the removal guide below can be of use and we encourage you to take a look at it once you finish reading this article.
The Pykw virus
The Pykw virus is a ransomware-based infection that purposefully blocks access to user files through encryption. The hackers behind the Pykw virus offer to restore access to the files in exchange for a ransom payment.
Users who desperately need the encrypted files (the ransomware can lock personal or professional documents, photos with sentimental value, videos, audios, archives, databases, etc.) but don’t have backups may be tempted by the offer of the hackers to pay the required ransom and obtain the promised decryption key. After all, this seems to be the easiest solution and, if you have the money and can afford to risk it, no one can stop you. The problem is that the criminals behind ransomware viruses sometimes fail to stick to their promises and, once they receive the payment, they vanish without sending a file-recovery key or another solution to the victims. Therefore, it is always worth exhausting every other alternative and keep the ransom payment possibility as your very last resort.
The Pykw file decryption
The Pykw file decryption is a method for file recovery that allows the ransomware victims to regain access to their encrypted data. The activation of the Pykw file decryption process, however, requires a decryption key which is in the possession of the hackers behind the malware.
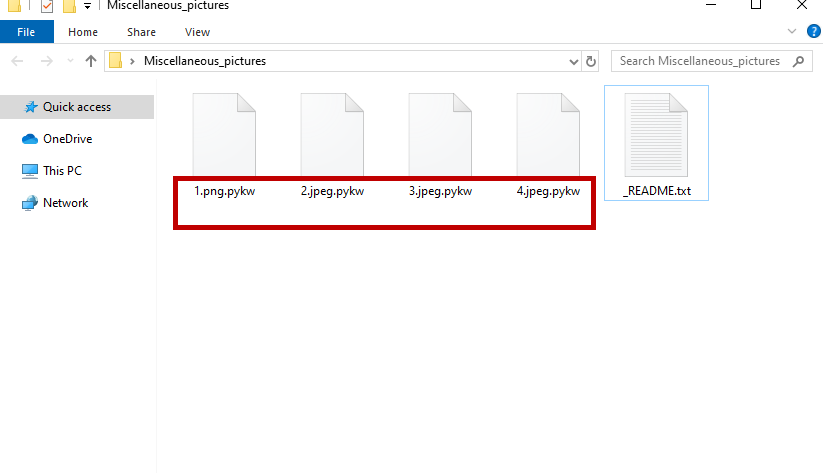
The Pykw virus will encrypt your files leaving a _readme.txt file behind.
And since receiving that key is not guaranteed in any way, our suggestion is to concentrate on the free file recovery options that are available. You can find a few in the guide below, as well as instructions on how to remove Pykw from your computer.
SUMMARY:
| Name | Pykw |
| Type | Ransomware |
| Detection Tool |
Remove Pykw Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment