Pysa
Pysa is a file-encrypting ransomware virus that can target more or less any operating system. Pysa encrypts the files on its victims’ computers and thus makes them completely inaccessible to anyone.
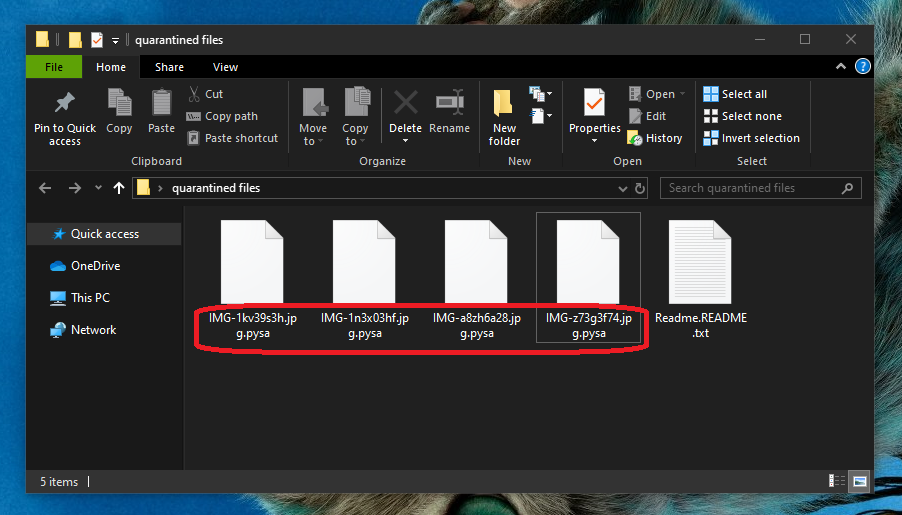
Once the Pysa Ransomware has infected you it will start encrypting your files.
In doing so, it in a sense holds the files hostage and then demands that the targeted users transfer a certain amount as ransom in order to regain access to their files. Namely, the hackers promise to send a decryption key, which is what you need in order to effectively decrypt the files. This is an age-old blackmail scheme that has unfortunately enjoyed a major boost in popularity thanks to cryptocurrencies.
As you may have noticed the hackers behind Pysa have requested that they be paid in some form of cryptocurrency. And this is because these currencies offer the shield of anonymity, and that, in turn, implies that no one will be able to track the cyber criminals and bring them to justice. This is one of the main factors that has contributed to making ransomware so incredibly numerous in the last few years.
And while we cannot really offer you any console when it comes to the future of your encrypted data, we can certainly tell you that the ransom payment is not the only option you have. In fact, we would encourage you to try the other alternatives that are available to you before resorting to sending your hard-earned cash to a bunch of criminals. Not only does doing so not guarantee that you will in fact receive a decryption key, but it’s also funding their awful extortionist scheme. Below is a step-by-step removal guide that will show you how to remove Pysa from your system, which is a vital step that you need to take anyway. And in the second part of the guide you will see what suggestions we have regarding the potential restoration of your files.
The Pysa Ransomware
The Pysa virus is infamously tricky to detect as it does not typically have any symptoms that you could be on the lookout for. This allows the Pysa virus to complete its malicious task without facing any interruptions.
This also applies to interruptions on the part of your antivirus system. If you have one installed on your computer, and it’s a fairly decent one at that, then you might be quite furious about the fact that it didn’t notify you about the ongoing infection. And this is yet another one of ransmomware’s annoying advantages over other types of malware. Because it uses encryption, which is in itself a benign process, antivirus software will not do anything to prevent it.
The Pysa file distribution
One of the leading means of distribution for the Pysa file is what is known as malvertisements. The hackers insert the Pysa file in fake online ads, and one click on an infected ad like this is usually all it takes for the attack to take place. Similarly, the ransomware can also be distributed in various other files that can be distributed via spam.
SUMMARY:
| Name | Pysa |
| Type | Ransomware |
| Detection Tool |
Remove Pysa Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment