Qtwebengineprocess
Qtwebengineprocess is one of the latest Trojan horse threats reported and is a highly dangerous piece of malicious code. If you have detected Qtwebengineprocess on your machine, it is important that you remove it immediately.
The Qtwebengineprocess.exe is a legitimate file of the Qt Web Engine software which is used to run the web-based applications. It uses the Qt Web Engine for embedding the web content for specific applications such as Dropbox, Origin, Bit lord, RingCentral, etc. Keep in mind that malware developers have been misusing legitimate files’ names to hide them on the system. Having that In mind we recommend you continue reading this article so you can get a better understanding of the Qtwebengineprocess.exe process.
If some strange and disturbing spam e-mails have been flooding your inbox lately, telling you about a hidden Trojan horse infection present in your computer and demanding that you pay a certain amount of money to the person who has sent them, then stay with us on this page until the end of this post in order to learn what the best course of action is in such a situation.
First, we need to tell you that such phishing e-mails and blackmailing messages aren’t something to be trusted. In most cases, the people behind them do not actually have access to your computer or data and are simply trying to scare you in hopes that you’d fall for the bait and send them the demanded sum. Of course, it may not always be easy to spot the scam at first – the crooks behind them can be very creative and convincing in their money-extortion tactics. However, unless you have actual solid proof that there may indeed be a virus in your computer, there shouldn’t be a real reason to worry at the sight of such messages.
What to do to secure our computer
One of the main problems related to the Trojan horse infections is that their symptoms may be inconsistent and in many instances, there may be no visible infection indications whatsoever. This is part of the reason why e-mail scammers oftentimes choose to threaten their victims with this precise form of malware. Even if you see no infection symptoms, this doesn’t necessarily mean that no Trojan is present on your computer.
Due to this, it’s important to check your system for potential malware hazards of this type if you receive any such blackmailing messages. The best way you can do that is through the use of some reliable software security program like antivirus or an anti-malware tool. On this page, you can find such a program – it is linked in the removal guide below. The removal guide itself is focused on a specific Trojan horse threat named Qtwebengineprocess. If you detect this or another similar infection (Bloom.exe, Great Discover) in your machine, you can use the guide to remove it. The anti-malware tool can also automatically remove the virus in case you don’t want to use the manual steps.
Qt Qtwebengineprocess
Even if you are one of the few unlucky users who do indeed have a Trojan like Qt Qtwebengineprocess in their machines, the best course of action is to try to remove the malware yourself rather than send your money to the blackmailers who are harassing you. There’s no telling whether or not the virus will go away if you pay them – for all you know, it may get activated right after you issue the payment, in which case you would have simply wasted your money. Therefore, we have made sure to offer you an alternative solution in the form of the guide you’ll see below and we advise you to use it as well as the removal tool that’s in it if you have any suspicions about the presence of Qt Qtwebengineprocess or another Trojan in your computer.
SUMMARY:
| Name | Qtwebengineprocess |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Detection Tool |
Remove Qtwebengineprocess Virus
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
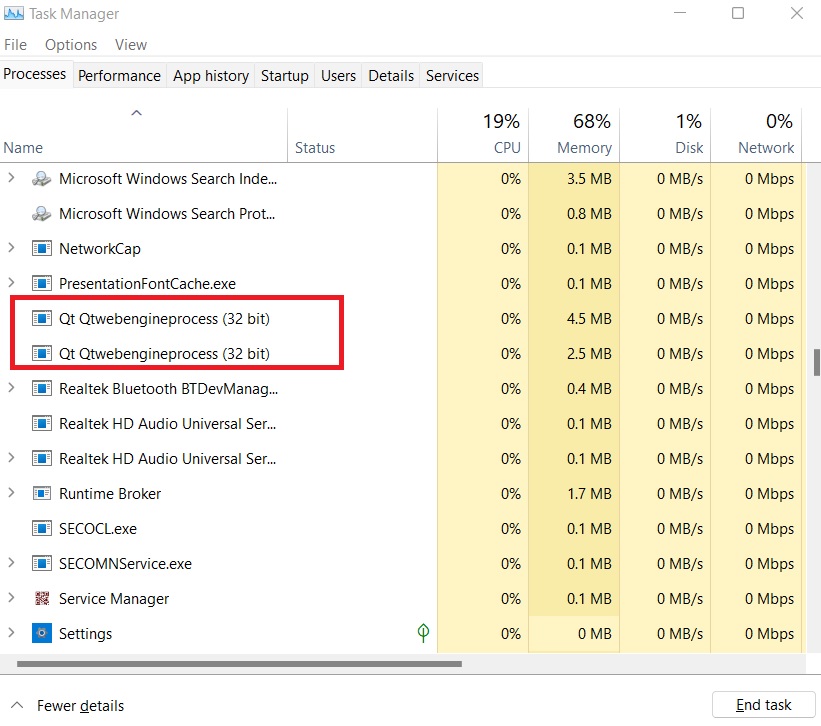
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment