R2U
R2U is an infection that applies encryption to a list of commonly used user files and then demands a ransom payment from the owners of these files. According to the way it operates, R2U is classified as a ransomware cryptovirus and represents a serious danger to any computer.
The internet is not a safe place and there are serious cyber threats that can be waiting for you there. In this post, we will explain one of the most dangerous threats known to users – ransomware. The most obvious effect of its presence on the victim’s PC is that all the most used files can be encoded. The virus then blackmails you for a ransom. The following guide addresses this topic in-depth and offers instructions on how to remove the infection on your own.
The R2U virus
The R2U virus is a dangerous ransomware virus that is aimed at extorting money from its victims by encrypting their files. The R2U virus infects the system in a secret way, places its encryption over some of the most used files and then demands a ransom payment.
The file-encrypting ransomware representatives like Oori, Ooxa are particularly hazardous programs. They have harassing and intrusive effects. R2U, for instance, will first infect the device secretly. There are several methods of infection that it likely used to do this. The sources of ransomware might include emails from unknown senders, attachments such as zip folders and documents inside your email; malicious notifications and pop-up alerts; fake ads that lead you to infected sites and software installers that have been compromised. The virus will only creep into your computer automatically once you have interacted with some of the above-mentioned possible sources. Sadly, you probably won’t get a clue that something is wrong until you get a ransom notification on your screen.
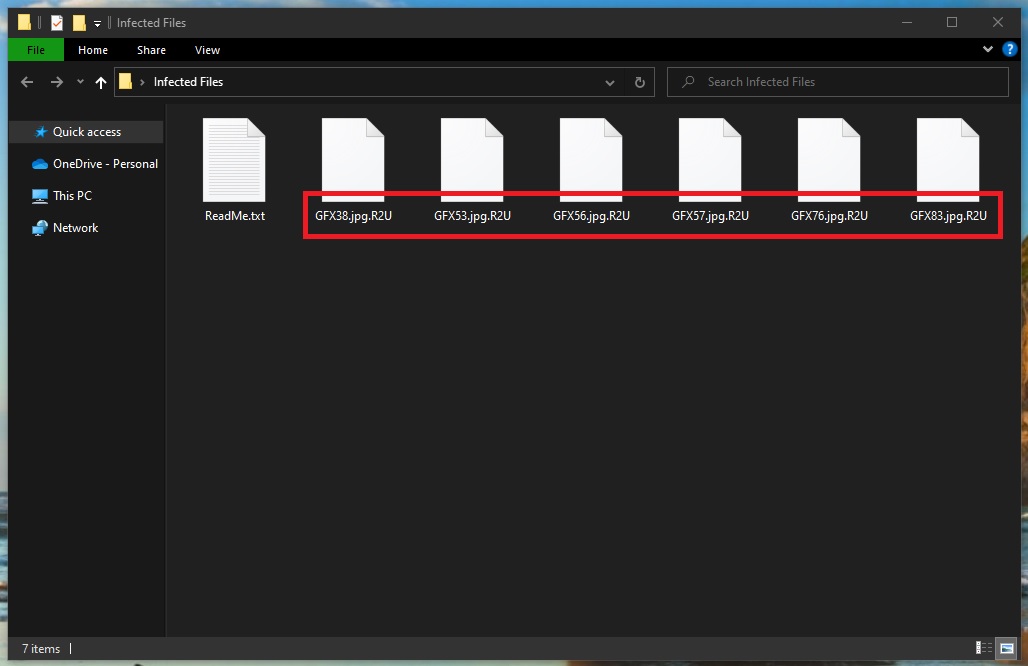
The .R2U file encryption
The .R2U file encryption is a form of malicious attack in which your most valuable files become inaccessible. The .R2U file encryption is a process that runs without visible symptoms and is almost undetectable even by professional security software.
The victim whose files have been encoded usually gets a message containing ransom payment instructions, applicable deadlines and other specific warnings from the hackers behind the ransomware immediately after the encryption process has been completed. Such notices usually include additional threats regarding possible destruction of the encrypted files if the ransom is not paid on time.
So, how should you proceed if you have been unfortunate enough to catch R2U? Naturally, you may be very anxious and concerned about the future of your PC and your files, particularly if you use and need these files on a daily basis. Nevertheless, it doesn’t make sense to hurry to pay the required ransom immediately after you get the ransom alert, because there might be some other solutions.
For instance, an alternative way to deal with R2U and possibly remove it is to consult a Ransomware expert. You may also have the option to purchase a specialized program that may help you deal with the infection. There is also the self-help method which includes using a free removal guide like the one below. If you are lucky enough you may be able to delete R2U with its help and even recover some of your files from system backups. However, we do not guarantee that the Ransomware nightmare will be over just like that. Additional steps may be needed to free your files and your machine. So take your time and research your options wisely.
SUMMARY:
| Name | R2U |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove R2U Ransomware
To remove the R2U virus, the victim must delete the malicious program responsible for infecting the PC with the virus, and then restore any system changes made by the malware.
- Delete any suspicious programs that are in the Programs and Features list.
- See what processes are listed in the Task Manager and quit the ones that seem harmful.
- Delete/disable/revoke any changes that the virus has made in the System Registry, the Hosts file, and the Startup Items.
- To remove the R2U virus, also delete any virus data found in the AppData, LocalAppData, PrigramData, WinDir, and Temp folders.
If you need more help with any of the steps shown here, read the more detailed instructions we’ve prepared down below.
Expanded Removal Guide

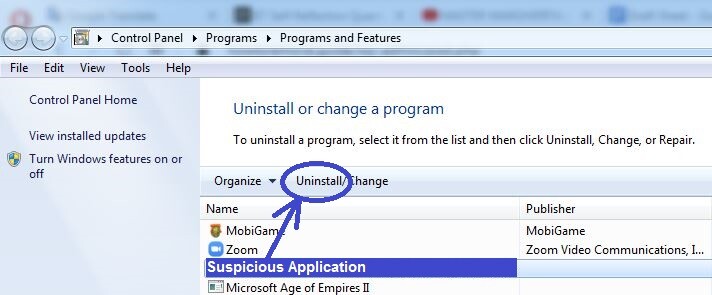
Search in the Start Menu for Programs and Features, click on the first icon, and look through the programs shown in the list that shows up. Anything that you think may be the reason from the R2U infection must be deleted. In most cases, the malicious program would have been installed not long before you noticed the virus in the system, so focus on the programs installed around that time.
When/if you find a program that you deem suspicious, click on it, select Uninstall, follow the on-screen steps and complete the installation while making sure that nothing from the suspicious program remains on the computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press the Ctrl + Shift + Esc combination from your keyboard and go to the Processes tab when the Task manager appears on your screen.
In there, try to find any processes that may be coming from R2U. Anything with high CPU and/or RAM usage that also has a strange name you don’t think you’ve seen before should be seen as potentially liked to R2U. However, we suggest that you first search for information on the internet regarding the suspicious process.
If your search confirms that the process may be malicious, the first thing to do is right-click on it, then select the option that opens its File Location Folder (the first one), and then, whatever files you find in the newly-opened folder, scan them with the free scanner that you will find right below (you don’t need to install anything, the scanner is used directly from the browser).


If you detect malware in the File Location folder of the suspected process, you must first quit the process as shown in the next image and then delete its folder. If the virus is not allowing you to remove the folder, delete whatever files you can from inside the folder and proceed with the rest of the guide. Upon finishing it, you should be able to remove all remaining malware data alongside the location folder, so make sure that you don’t forget to do that.
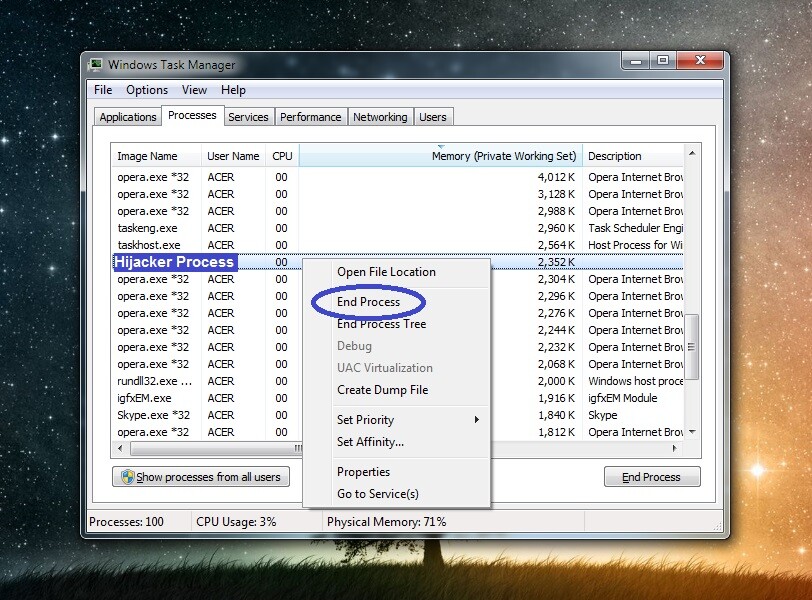
Note: If the scanner didn’t find malware in any of the files, but you are fairly certain that the process is malicious, go ahead and quit it and then delete its data.

You should now enter Safe Mode on your computer to prevent R2U from running any more of its processes. To help you go into Safe Mode, we’ve prepared a separate guide for that which can be accessed by clicking on the provided hyperlink.

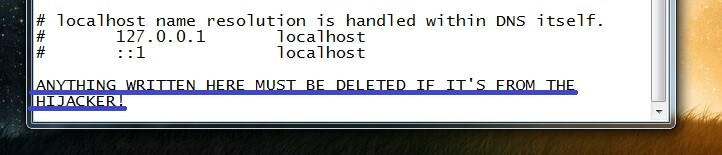
Check your PC’s Hosts file by entering this: “notepad %windir%/system32/Drivers/etc/hosts” in the Start Menu search field and hitting Enter. If you are asked to pick a program with which the file will be opened, select the Notepad icon.
When you see the Hosts text file open, look at what’s written at the end of the text. The presence of any text below “Localhost” (especially if that text is strange IP addresses) indicates that the file may have been hijacked by the virus. Copy anything that may be written below the Localhost lune and send it to us in the comments section. We will get back to you with a reply on what needs to be done next once we take a look at your comment and determine whether the text in your Hosts file that you’ve sent us indicates that the file has been compromised.

Start the Registry Editor by typing regeit in the Start Menu, clicking on the first icon, and then selecting Yes
Next, press the Ctrl and F keys, write the name of the virus, and initiate the search for related items in the Registry. Anything that gets found for this search must be deleted. Keep repeating the search and removing what it finds until no items related to R2U remain. Also, be warned that you must not delete something that you aren’t certain should be deleted until you ask us in the comments about it, and we tell you to go ahead and delete it. Only malware items should be removed from the Registry – the deletion of anything else may cause severe system problems!

You should also check the next Registry locations (by navigating to them in the left panel of the Registry Editor) for rogue items. Anything that has a very long name composed of random letters and numbers is probably unwanted. Still, before you delete anything, we once again advise you to consult our team by writing us a comment.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main

One by one, copy the next lines, paste them in the Start Menu, and hit Enter after each.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
In the folders you will be taken to, you must delete all recently created data files – any files that have been created after R2U infected you. The only folder in which you must delete everything is Temp.
Use Professional Removal Software
Ransomware threats are often too advanced to be removed manually and so if the steps we’ve shown you this far have proven to be ineffective, it may be time to try using a professional anti-malware tool to help you resolve the problem with R2U. One thing to mention here is that Trojans often times help Ransomware viruses enter the computer and gain persistence in it which is yet another reason why you may need the help of a specialized malware-removal software. Because of this, we strongly recommend using the powerful anti-malware program offered on this page in case you have thus far been unable to resolve the problem with R2U.
How to Decrypt R2U files
If you manage to delete R2U, this won’t automatically release your files, yet it is important for the virus to be gone from your system before you attempt to restore your data. There are several ways you can bring back your files. Paying the required ransom is one of them, but it is the most inadvisable since you don’t know if you’d get any files back for your money.
Therefore, we’ve done our best to provide our readers with the most effective alternatives out there, and we’ve compiled them in our How to Decrypt Ransomware article that we advise you to visit once you are done with the R2U removal. On the other hand, if you still have any doubts that some malware data may be left in the computer, remember that you can always use the free online scanner that we have on our site to test suspicious files for malicious code.

Leave a Comment