*Source of claim SH can remove it.
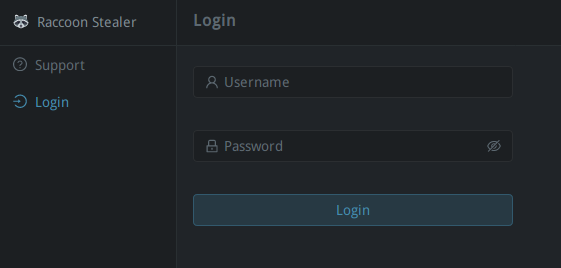
The Raccoon Malware
Raccoon Stealer is a trojan horse application which will stealthily infect your system and gather personal information. This trojan will most likely lead to various issues with your computer so it’s removal should be a prority.
The Raccoon Malware is a Trojan-based malware that can secretly launch different malicious activities in the infected system. The Raccoon Malware can hack the computer’s webcam or mic and allow hackers to watch and listen to their victims. The Trojans are among the most terrible online threats in existence. Getting infected with one of them is the last thing you would want to happen to your computer. Yet, sometimes, you may end up in a situation where you may need to deal with such malware as fast as possible. Today’s article is dedicated to one of the recently released Trojan Horse viruses called the Raccoon Malware and if you’ve found that your machine has been infected with this particular piece of malicious code, here we will try to share with you some helpful information about it. More importantly, we will provide you with a set of instructions on how to remove the Raccoon Malware from your machine so that you prevent any further harm this Trojan may cause.
Racoon Infostealer Malware
The thing about the Raccoon Infostealer Malware is that it is very flexible and can be programmed to achieve a whole range of different malicious tasks. Therefore, it is really hard to tell for sure what exactly an infection such as the Raccoon Infostealer Malware can do in your system unless you face the malicious consequences of its attack.
In addition, the Trojan is considered to be very stealthy. That’s the reason why it is called a Trojan Horse in the first place. Such malware can enter your system like a file or a program that seems to be harmless, and then start to perform whatever it has been programmed for. Most importantly, it rarely causes any visible symptoms that would prompt the victim to scan their device for malware.
As for the various types of damage a threat like the Raccoon Malware could potentially cause, the list is pretty long. It can involve the destruction of important documents, system destruction, theft of information, espionage, exploitation of resources, and so on. If a Trojan is set to steal your information, for instance, it may launch a process known as keylogging to keep track of your keystrokes. If the malware is set to destroy your information, it may delete, modify, or replace certain files or wipe clean the entire disc they are stored on.
Sometimes, the hackers behind the infection can be after some private or sensitive data. In this case, they may use the Trojan to keep track of your online and offline activity and watch everything you are doing, as well as everyone you are talking to through your webcam and mic. Another very disturbing possibility is that an infection like the Raccoon Malware may secretly attach other malware, such as Ransomware, to your computer. That’s why you need to make sure to use our removal guide below to quickly remove the Trojan before it manages to complete its agenda.
Just keep in mind that if you go for the manual removal method, you will need to access system files which will require more care and attention. Therefore, you should follow the steps exactly as they are shown to prevent accidental removal of important system files. Deleting vital components of the OS can make your computer unusable, so if you don’t feel confident enough to handle these files manually, we recommend you use a professional removal tool to do the job for you.
SUMMARY:
| Name | Raccoon Malware |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Remove Raccoon Malware
If you are looking for a way to remove Racoon Malware you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Racoon Malware and any other unfamiliar programs.
- Uninstall Racoon Malware as well as other suspicious programs.
Note that this might not get rid of Racoon Malware completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


*Source of claim SH can remove it.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!


Leave a Comment