RAGNAROK Ransomware
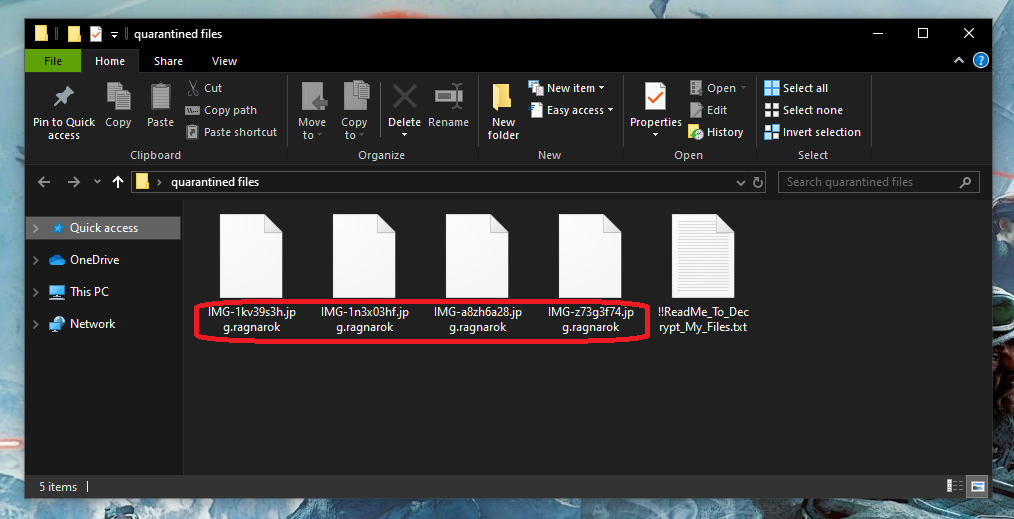
RAGNAROK is ransomware of the utmost dangerous type. Namely, RAGNAROK is a file-encrypting ransomware variant. And this means that once it invades its victims’ computers, it proceeds to encrypt all the most-used file types on it. As a result, users are no longer able to access these files and they are forced to pay a certain (usually quite large) amount of money in order to regain this access.
If this is your case, then you most likely only found out about this terrible infection thanks to the chilling notification that appeared on your screen informing you of the malicious process that had already taken place. Normally, the hackers behind the virus will also include payment details and instructions on when and how to make the transfer. And as a rule, they always tend to request that the money be paid in Bitcoin or some other type of cryptocurrency, because this enables them to remain anonymous and prevent being tracked by the authorities.
Our advice to you is to take a deep breath and not take any drastic action right away. Whatever you do, it’s important that you first remove RAGNAROK from your system, because otherwise you risk repeating the whole process again even if you do manage to recover your files in the meantime. For this we can provide you with a handy removal guide which you will find on this same page, below the current post.
The RAGNAROK virus
The RAGNAROK virus is among the trickiest types of malware in existence. The encryption that the RAGNAROK virus uses can be incredibly difficult to reverse and is what makes this ransomware so harmful. In addition, the encryption is also what allows ransomware like this particular variant to go unnoticed and work under the radar of most antivirus programs.
The thing is that encryption is not in itself a malicious process as it does not damage or harm the affected pieces of data. Much on the contrary, originally encryption is actually used as a means to protect data and it’s what we all rely on to safely make purchases online, for example, so that no one can get ahold of our banking details. However, the hackers in this case use it for criminal purposes and with the intention of extorting money from their victims.
The RAGNAROK file distribution
The RAGNAROK file distribution typically happens with the help of a backdoor virus. Normally, the RAGNAROK file distribution is ensured by a Trojan horse. And how it happens is you can get infected with a Trojan by opening a contaminated email attachment or clicking on a malicious ad, for example. Then, the Trojan immediately downloads the ransomware, which in turn gets to work and begins to scan your system for the target file types right away.
For this reason, after you have removed RAGNAROK from your computer, we recommend running a scan for Trojans as well. This is among the most common distribution tactics, and if it’s how you ended up infected, then you don’t know whether the Trojan might download another ransomware virus onto your computer later.
SUMMARY:
RAGNAROK Ransomware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply