Randex
Randex is a stealthy Trojan that can infect computers without any symptoms and can start malicious processes in their background. Hackers can use Randex to gain unauthorized access to the system, spy on their victims, steal sensitive information and more.
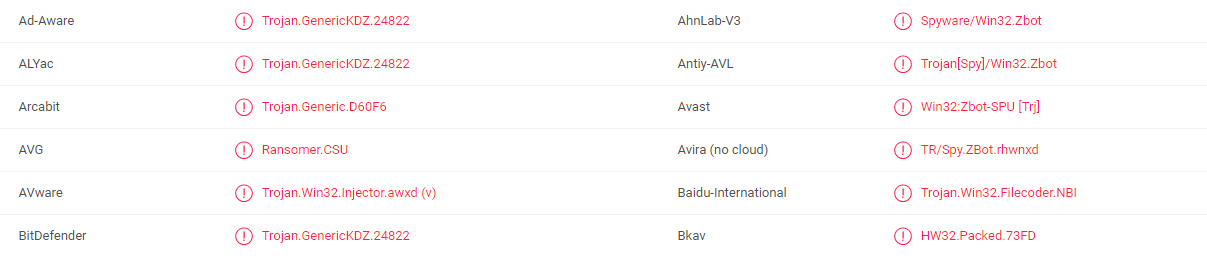
The members of the Trojan horse category of malware are commonly known to be very versatile and to be extremely difficult to detect and remove. This applies even more so to Randex, which is a new threat that infects computers without any visible symptoms and launches different malicious processes in them. What makes it especially difficult to identify and intercept such Trojan horse viruses in time has to do with the inability of most antivirus programs to correctly detect the latest Trojan-based infections and to warn users about them. This is because, in order to recognize a certain program as malicious, most antivirus programs rely on their database. The problem is if a given new threat, such as Randex for example, has not been added to the database or the user has not updated the virus definitions of their security software in some time, even if the infection is present on the computer, the antivirus program will probably not classify it as unsafe and will not take actions against it. In this case, the Trojan is practically invisible to the security software unless it is added to the database and is able to attack the machine without being disturbed. Of course, the more sophisticated the security program is and the more frequently users update it, the greater its ability to protect the computer against the latest online threats.
Sadly, detecting a Trojan without the help of reliable antimalware software is oftentimes not even possible because this malware usually does not cause red flags that would give it away. Nevertheless, there are certain things that you should look for, as they could actually indicate that a threat such as Randex has compromised your computer. The infamous Blue Screen of Death crash is one of these potential symptoms. It is a device crash error screen triggered by a serious computer problem. While Blue Screen crashes may have several triggers, a Trojan horse infection can definitely be one, particularly if this symptom is coupled with general computer instability, freezing of the screen or device or browser settings changes you haven’t authorized or approved. In general, any sort of device disruption may be a sign of a Trojan horse virus, so make sure you always check anything that seem wrong with your computer.
Due to their versatility, Trojans such as Randex are used in a variety of criminal operations and may carry out a series of harmful acts, including collecting confidential personal and/or professional information, spying on their victims online and offline activities, introducing new threats into the attacked computer (especially ransomware, spyware and rootkits), and providing the hackers with full control over the entire OS. All of this means that a single Trojan may cause very unpredictable harm. Regardless of the end goal, the virus should be removed as soon as possible, ideally with the help of the instructions below.
SUMMARY:
Randex Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply