.Ranzy
.Ranzy is malicious software intended to force you to give a ransom to its developers, by stopping you from accessing your data. .Ranzy is a representative of the Ransomware class of malware which is known to data encryption technique to restrict access to user files.
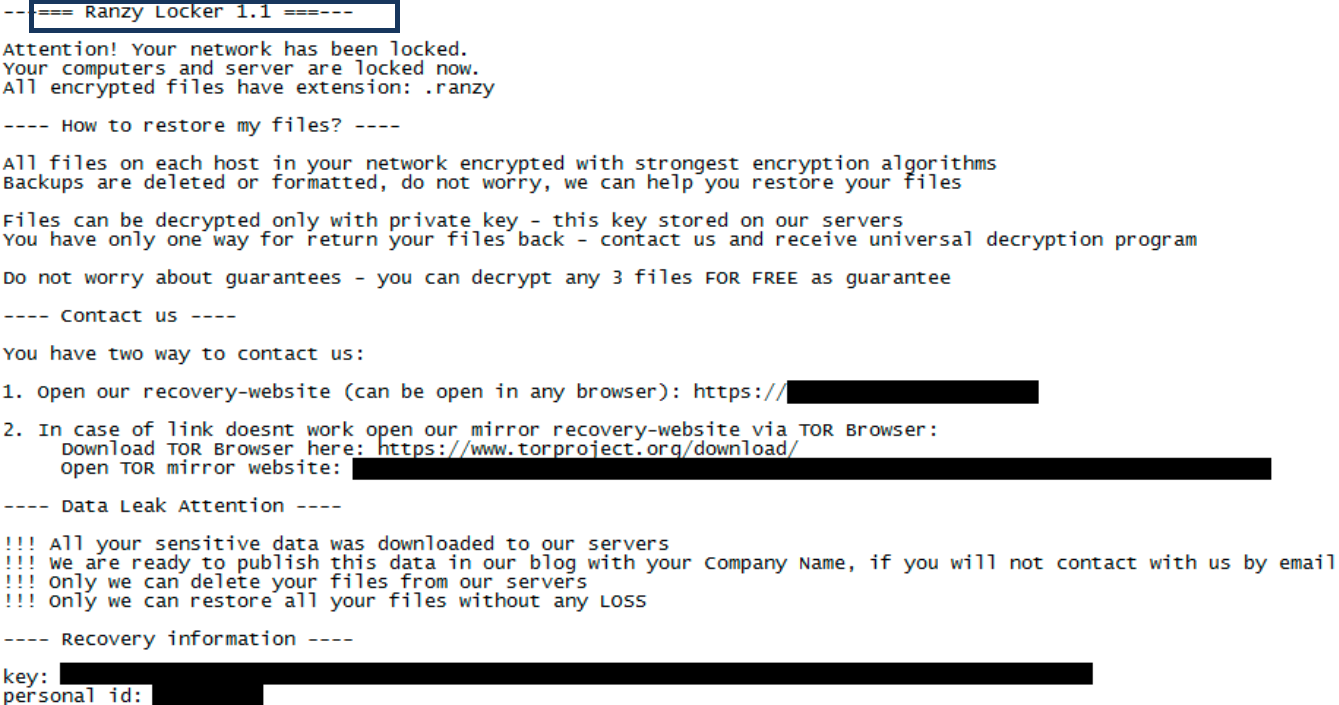
The Ranzy Locker ransomware (before ThunderX) is now “Ranzy Locker 1.1”.
The Ransomware malware category has undergone a massive boom over the past couple of years. The number of viruses of this type has grown tremendously and nowadays, threats like .Ranzy, .Booa or .Igdm can be encountered all over the Internet. Fake ads, spam messages, infected software installers, torrents, malicious links and questionable websites could be potential carriers of the infection and one careless click is usually enough to invite the malware inside the computer. Once the virus enters the user’s machine (which typically happens without notice) it starts a process that encrypts most or all of the user’s personal files. The moment a given file is encrypted, no conventional program can open it and the victim becomes unable to open, use or modify any of his or her files after the Ransomware encryption is applied. This provides the perfect opportunity for the hackers behind the virus to blackmail their victims for a ransom.
The crooks typically promise that if the person pays the demanded ransom money within a given deadline, they will provide him with a special decryption key that can make the data on that specific computer available again. Of course, not all people will be prepared to pay the ransom – some may not have the demanded money while others may simply not want to take the risk of making a payment to anonymous hackers without having a guarantee about the recovery of their information. In any case, paying the ransom is not advisable as this only encourages the hackers to continue with their blackmail scheme.
The .Ranzy Ransomware
The .Ranzy ransomware is a piece of malware that uses stealth to infiltrate computers and encrypts the files on their hard drives. During the file-encryption process, the .Ranzy ransomware does not show any warning flags which is why it is very difficult to detect and remove it in time.
Many users come to know about the infection after the ransomware has already finished the job of encrypting their data and has placed a notification with ransom demands on their screen. Usually, such demands are delivered in the form of a computer pop-up or a notepad file that includes the amount for the ransom and guidance about how to pay it. Even if you highly value the files that the virus has encrypted, however, your first move shouldn’t be to pay the ransom money. The reason is, the cyber criminals who use Ransomware to blackmail their victims sometimes don’t keep their word and only take the money without sending back a decryption key.
The .Ranzy file decryption
The .Ranzy file decryption is a process that will enable victims of the ransomware to recover access to their data. The .Ranzy file decryption usually needs a special key to complete successfully, however, there might be several other methods that can help.
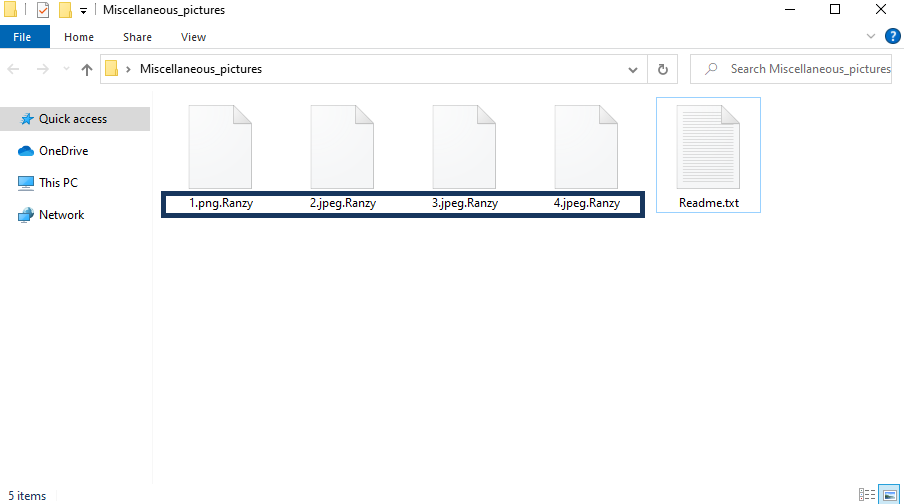
Encryption of the files by the .Ranzy virus file
In the file-recovery section of the removal guide below, you will be given some alternative solutions that can be used for free. However, before you give them a try, we highly recommend that you remove .Ranzy by completing the removal steps in the first part as this will prevent the ransomware from encrypting any data you manage to recover.
SUMMARY:
| Name | .Ranzy |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
.Ranzy Ransomware Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt .Ranzy files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment