*Source of claim SH can remove it.
Re-captha-version-3-21.icu
Re-captha-version-3-21.icu is a form of browser redirect and one of the most annoying types of programs out there, as you have surely already concluded if you’ve come in contact with it. The following article is dedicated to explaining what exactly this piece of programing does, the myths and facts about it, how to avoid it and below is a guide that will walk you through the simple steps of removing Re-captha-version-3-21.icu from your computer. However, the developers would naturally also want you to mean to click on the ads, so they tend to try and tailor the many offers and “hot” deals to your taste. How? By monitoring and analyzing your browsing activity. browser redirect is known to collect this data and send it over to the developers, so things like the webpages you most frequently visit, your search queries and even personal details you may have left somewhere are all carefully stored in order to produce content that would be more relevant to you.
First and foremost, as we’re certain you must have read the misconception somewhere else, Re-captha-version-3-21.icu is not a virus. Moreover, it’s very far from that sort of malicious software and will not cause any direct harm to your computer, such as actual threats like ransomware or Trojan Horses would. This does not mean that browser redirect is completely safe, though. There are several risks related to having it on your system and we will explain those in just a bit.
Re-captha-version-3-21.icu Virus
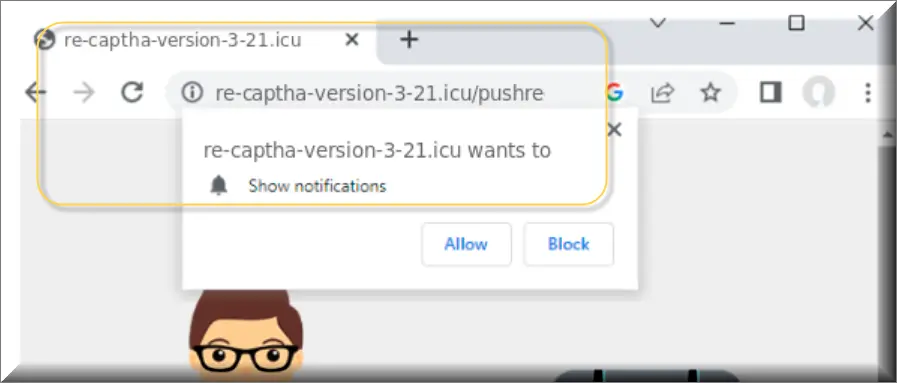
The Re-captha-version-3-21.icu virus is a browser hijacker that infiltrates your system, disrupting your web browsing experience by generating intrusive pop-ups, banners, and notifications. This unwelcome software may alter your browser settings, including the homepage and default search engine, without your consent. If you’ve encountered an influx of unwanted ads and suspicious redirects, it’s likely due to the Re-captha-version-3-21.icu virus. Browser hijackers of this kind often aim to generate revenue for developers through pay-per-click schemes. To safeguard your system and restore your browser’s functionality, it’s recommended to promptly remove the Re-captha-version-3-21.icu virus using effective removal tools or following the manual steps provided below.
What is Re-captha-version-3-21.icu?
This part is probably the most obvious one: Re-captha-version-3-21.icu distributes myriads of adverts in the form of pop-ups, banners, page redirects, box messages, etc. These can get very frustrating, due to their vast numbers and hindering placement, making navigating past them quite the difficult task. And this is probably also the very reason, why you are here. However, that’s only the tip of the iceberg and we’d like to shed some light on what happens behind the scenes. The developers of extensions like Re-captha-version-3-21.icu, Your Search Ba, iStart Search Bar make a profit based on the Pay per click scheme, which enables them to earn money literally off of every click that lands on any of the featured ads. Hence the quantity and the strategic placement of them, which increase the chances of accidental clicks.
Re-captha-version-3-21.icu Pop-ups
Common sense would immediately be sounding the privacy violation alarm. Most users would definitely be concerned with the fact that someone is able to track such information about them, and rightfully so. The creators behind programs like Re-captha-version-3-21.icu Pop-ups are notorious for selling this data to 3rd parties, who could do with it as they see fit. Another risk associated with Re-captha-version-3-21.icu Pop-ups is the fact that it has the potential of serving as a gateway for other threats, much more serious ones. It’s fairly rare that this would happen, but nonetheless, if the chance is out there – why take it? Threats like ransomware and Trojans have the capability of causing irreversible damage and this is certainly not something you would like to be faced with, just because you couldn’t resist clicking on a given ad. That ad could lead you to malicious website and who knows what could end up infiltrating your PC from there.
Re-captha-version-3-21.icu on Chrome
The key to staying safe online is in understanding the way unwanted programs, like Re-captha-version-3-21.icu on Chrome are distributed. In the case of Re-captha-version-3-21.icu, there are several popular methods, one of which is direct (but false!) marketing of it as a useful tool. Many developers try to offer their product for direct download by promoting it as a browsing enhancer of some sort, designed to improve your online experience. Needless to say how untruthful that statement is, given the fact that this very program could slow your computer down, result in browser crashes and end up ruining your day. But the most popular way of getting people to download and install Re-captha-version-3-21.icu on their PC’s is trickier yet.A technique called program bundling is a very commonly used one by legitimate and criminal programmers alike. In the case with Re-captha-version-3-21.icu, it is bundled into another program, typically some freeware or shareware that was downloaded from some semi-trustworthy source.
Once you proceed to run the installation setup of the desired program, you will be given the option of choosing the default or custom/advanced settings of the setup. By choosing the former, you will not see the included additional programs and will only begin to suspect they’re on your computer after it’s too late. By choosing the advanced option, though, you will not only be able to see the additional software, but also determine whether or not you will allow it to be installed, too.
SUMMARY:
| Name | Re-captha-version-3-21.icu |
| Type | Browser Hijacker |
| Detection Tool |
*Source of claim SH can remove it.
Remove Re-captha-version-3-21.icu Virus
To try and remove Re-captha-version-3-21.icu quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Re-captha-version-3-21.icu extension (as well as any other unfamiliar ones).
- Remove Re-captha-version-3-21.icu by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Re-captha-version-3-21.icu and any other suspicious items.
If this does not work as described please follow our more detailed Re-captha-version-3-21.icu removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Re-captha-version-3-21.icu app and kill its processes
Uninstall the Re-captha-version-3-21.icu app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Re-captha-version-3-21.icu. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Re-captha-version-3-21.icu, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Re-captha-version-3-21.icu.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Re-captha-version-3-21.icu changes made to different system settings
Undo Re-captha-version-3-21.icu changes made to different system settings
It’s possible that Re-captha-version-3-21.icu has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Re-captha-version-3-21.icu from your browsers
Remove Re-captha-version-3-21.icu from your browsers
- Delete Re-captha-version-3-21.icu from Chrome
- Delete Re-captha-version-3-21.icu from Firefox
- Delete Re-captha-version-3-21.icu from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Comment