This page aims to help you remove the .Reco Virus for free. Our instructions also cover how any .Reco file can be recovered.
.Reco
.Reco is a computer virus of the notorious Ransomware variety. A ransomware virus such as .Reco would encrypt your files and demand a ransom payment in exchange for the decryption keys.
.Reco is a Ransomware cryptovirus that can blackmail you for a ransom. If .Reco has infected you, you’re in a serious trouble.
You’ve likely been informed of the infection via a warning, generated on your computer’s desktop. No doubt that facing such a malware is a stressful experience. On this page, however, we’ve prepared a removal guide to help you effectively remove .Reco from your computer, as well as some instructions on how to potentially get the encrypted files back.
The .Reco virus
.Reco is a file encrypting type of a computer malware known as Ransomware. .Reco is a very dangerous virus which could completely distort a user’s system.
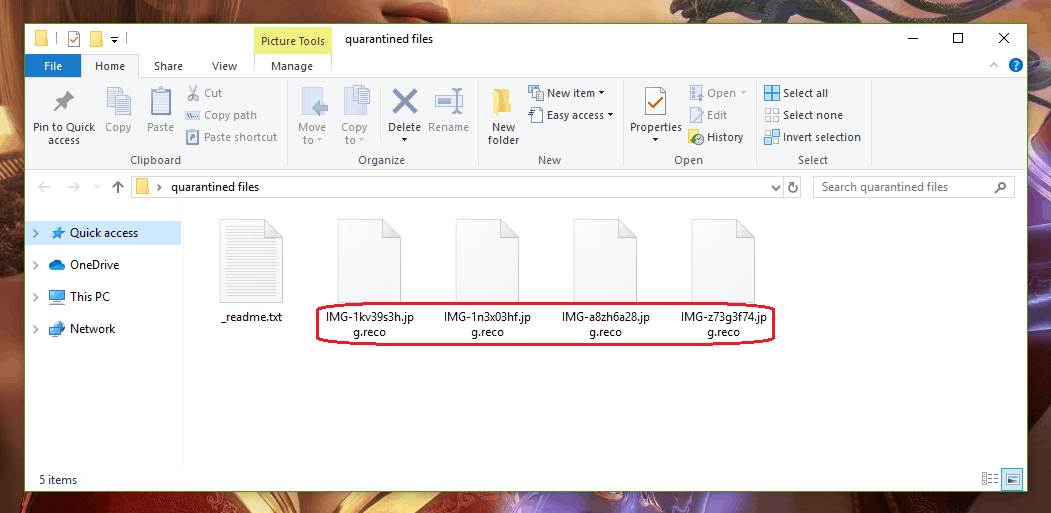
The .Reco virus is a sophisticated file-encrypting infection. The sole purpose of the .Reco virus is to block your access to some of the data stored on your computer.
Then the malware demands a ransom in exchange for a special decryption key, needed to liberate the sealed information. Sadly, this is the second most common form of malicious software, and it’s been around for over thirty years now. Over the past few years, however, the Ransomware has undergone a gigantic increase in popularity with the cyber criminals producing millions of unique samples each year.
The main reason for this is the crazy amounts of money created by these kinds of infections for the hackers who build and distribute them. At the same time, the cyber criminals are notoriously difficult to track because they often demand the ransom to be paid in bitcoins. Bitcoins is one of the most well-known cryptocurrencies and the authorities are almost unable to track it.
Usually, programs such as .Reco, .Xoza and .Noos are delivered with the help of malvertisements, which are actually advertisements that upload the malicious software to your device when you click on them, most of the time without even knowing what happened. Another very powerful and widely used method for distribution of Ransomware is by a Trojan horse virus, which installs the infection once you have let it into your network. Typically the infection occurs once you open a spam email with attachments or hyperlinks which contain a Trojan that has been designed to insert the Ransomware into the system.
After the secret contamination, an infection like .Reco will begin the encryption of your files as scheduled to do, and you will be presented with a ransom note upon completion. Normally, you won’t be able to notice the process, unless your machine’s processing power is not the strongest or there’s quite a lot of information stored on your machine. In this case, you may experience a very significant decrease in speed and overall performance on your PC which may prompt you to check your Task Manager and scan it for unknown resource-consuming processes. If you find a process that obviously does not belong to your system or arouse suspicion in some way, we advise you to shut down your computer immediately and seek professional help before turning it back on.
The .Reco file encryption
.Reco is what is known as a ransomware computer virus. .Reco would encrypt the affected user’s files and render them completely inaccessible.
The .Reco file encryption is the most unpleasant consequence of the Ransomware’s attack. Dealing with the .Reco file encryption, however may not be easy.
Normally, in order to reverse the applied encryption you will need a special decryption key. Paying ransom to the hackers in order to obtain it, however, may not be a good idea and will only put your money to risk. Therefore, we advise you to take a look at our removal guide and check out the instructions there before deciding on whether to pay the hackers or not. These steps will hopefully help you remove .Reco and get some of your files back without paying a ransom.
SUMMARY:
.Reco Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply