Reha
Reha is a Ransomware program created for blackmailing purposes. Typically, Reha is programmed to encrypt user files and to keep them inaccessible until the victims agree to pay ransom for them.
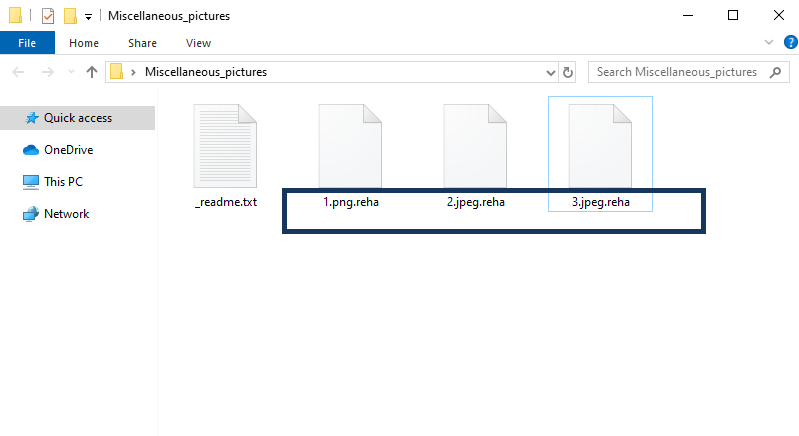
The Reha Virus will encrypt your files and leave a _readme.txt file behind.
You probably came across our article while looking for a solution on how to remove Reha. If this is the case, you should know that on this page we have prepared a comprehensive removal guide that will not let you down. Reha is one of the worst computer hazards ever created but this should not discourage you from dealing with it, because we will suggest possible ways to address this problem and will provide you with some general information about the malware you are facing.
The Reha virus
The Reha virus is a ransomware representative intended to encode user files and keep them hostage for ransom. What is typical about the Reha virus is that it will notify its victims about the attack by placing a ransom-demanding alert on their screen.
One thing to remember about Reha and Ransomware viruses in general is that they can be hidden on a website or be incorporated into a spam mail or a foreign email and its attachments. Besides, these threats can also be hidden inside different software bundles or torrents. But most commonly, the Ransomware infections get distributed in a combo with a Trojan horse and be introduced in the system thanks to security vulnerabilities. The Trojan secures the “safe passage” of the Ransomware through those security vulnerabilities and then the Ransomware is free to explore the infected device.
Once Ransomware like Reha becomes a part of your system, it often operates very subtly at first. It only gathers some information about the files you like to use or visit. Then it starts encoding them one by one with a secret encryption algorithm. To reverse the encryption, you are typically offered to pay for a decryption key which is kept in secret by the hackers behind the Ransomware.
The Reha file recovery
The Reha file recovery is a process that requires either a full personal data backup source or a file decryption key. The Reha file recovery may also be possible if you manage to extract files from the backups of your system.
In order to deal with the Reha file encryption, the ransom payment is always an option. Yet, keep in mind that the people you are paying to are usually interested only in your money and once they get it, there is nothing that can make them keep their word and help you recover your files. So, before considering the ransom payment as an option, take into consideration the fact that your money may go to someone’s wallet for nothing and you may never get a decryption key from the hackers. To avoid that risk, and to save your money, you can try to remove the Reha virus with technical help or a guide like ours. Alternatively, you can use professional software to clean your computer and recover your files from available backup copies.
SUMMARY:
| Name | Reha |
| Type | Ransomware |
| Detection Tool |
Remove Reha Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

All my file is affected due to reha. My file showing .reha and if i select then remove .reha file can damage.
So i need ur help to recover my file
Hi Abdul wazid, Look for a decryptor on our page, if you don’t see one that means we cannot help you recover your files yet.