*Source of claim SH can remove it.
Remcore
Remcore infects the browsers installed on macOS devices and turns them into platforms for online advertising. Therefore, Remcore fall into the category of the so-called browser hijackers.Specifically, browser hijackers get their name from their ability to override your browser’s configurations and instate new ones. For example, Remcore can easily change the homepage of your Safari, Chrome, Firefox or whatever other browser you may be using. And in the same way it may also change its default search engine to some Google or Bing rip-off. Furthermore, programs of this type also cause your browser to trigger spontaneous page redirects that land you on pages you probably had no desire on visiting at all.

These are only a few of the different unwanted effects that typically accompany the presence of applications like Remcore on the infected device. But the good news is that you won’t have to put up with it for much longer. With the help of the removal guide we’ve put together for you below, you will be able to quickly handle this infection by yourself. It contains step-by-step instructions that will show you how to thoroughly remove Remcore and all of its components from your computer.
Remcore for Mac
Remcore for Mac is a particularly annoying piece of programming that acts as an advertising tool. Normally, developers create applications like Remcore for Mac to benefit from Pay Per Click ads.How this works is that the browser hijacker generates online advertisements in the forms of links, banners, popups, box messages and what have you and displays them directly on the screens of users. Usually, the placement of the ads is highly aggressive so that users are often left with no choice but to interact with them. And this, in turn, generates revenue for the developers.
What is Remcore?
The way that hijacker like Remcore operate is not always entirely straightforward. As a result of the activities Remcore performs, your machine could become more susceptible to virus attacks.For example, if as a result of a page redirect, you land on some website that has been infiltrated by Trojans, ransomware or other viruses, you could get infected. The same goes if you happen to click on an ad that leads to some unsafe web location, which the hijacker developers hold no responsibility for.Furthermore, browser hijackers like Remcore are often tightly associated with data-collection practices that are also widely frowned upon – especially among end-users. After all, you were hardly too happy to find out that this hijacker is on your computer, let alone that it may be gathering information from your browser.
The Remcore app
The Remcore, Ryder or Pipidae, app could have been added to the setup of another program that you recently downloaded. This is a common practice known as program bundling that developers use to distribute software like the Remcore app to the end user.But typically if you customize the installation process of any new software manually, you should be allowed the chance to opt out of any added components.
SUMMARY:
| Name | Remcore |
| Type | Adware |
| Detection Tool |
*Source of claim SH can remove it.
Remove “Remcore will damage your computer” from Mac
The following instructions will allow you to remove “Remcore will damage your computer” in two ways:
- The manual instructions will allow you to remove it on your own by downloading 2 software suites which will show you the folders the threat is located in. Installing, scanning, and deleting everything will require 1-2 hours of your time, depending on your speed and the threat itself.
Note: If “Remcore” has an in-built ability to restore itself on a restart, the manual steps will not prevent that. We recommend the automatic removal. - Download SpyHunter for Mac (one of the apps used in the manual instructions), scan with it, and if you decide to use the program, it will likely require about 15-20 minutes. This, however, requires an active subscription for SpyHunter, which means either to use the trial version or purchase the software.
Removal instructions:
1. Download EtreCheck from the Appstore and scan for any “Remcore” unsigned files. Delete them. (You can skip this step altogether and download and scan with Spyhunter instead if you don’t want to double-check things).
2. Download and install Spyhunter for Mac. Scan for any malicious files.
3. The app will show you which files are infected. Either use SpyHunter to delete them for you (the automatic removal) or do it manually, which means tracking down each detected location by yourself and deleting the file.
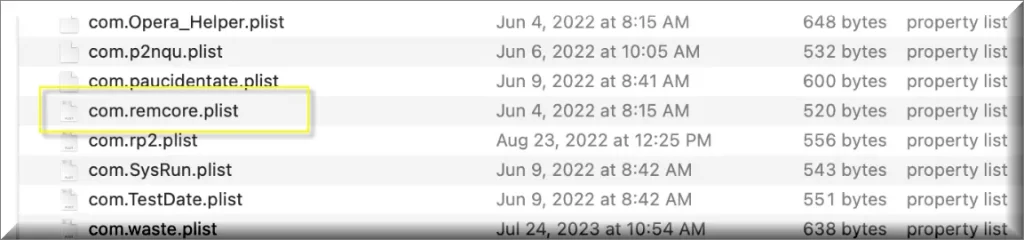
4. In most cases start with /private/var/root/Library/Application Support/.”Remcore”/”Remcore”
5. In Finder press Shift+Command+G to open the Find window.
6. Search for the /var directory. Then proceed and look for the /root folder inside.
7. It will most likely be locked and you will need additional permissions to meddle with it.
8. Press command+I and scroll to sharing and permissions. Add your user name to permissions.
9. Now you should be able to access the /root folder and proceed and locate the /Library folder inside it. Proceed to do the same until you are inside the /Application Support folder.
10. It is possible that the folder you look for is hidden, if that is the case use command+shift+. to locate and find the file you want to delete.
11. Delete the “Remcore” file.
12. If none of this helps, try the steps in this guide.

Leave a Comment