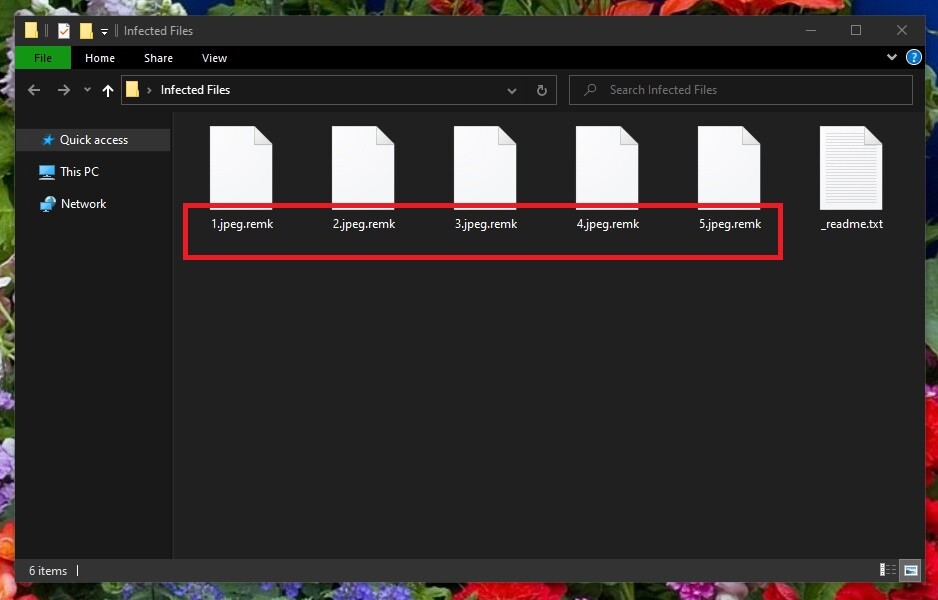
Remk
Remk is a file-blocking malware program categorized as a Ransomware virus. The creators of Remk use this piece of malware to extort money from the attacked users by blackmailing them for the access to their own files.
File-encrypting Ransomware attacks are very common nowadays and, sadly, there’s still no universal solution against this particular type of malware. The best thing one could do is to back up their most valuable files, thereby ensuring that even if Ransomware attacks the computer, the backed up files will still remain safe. This, of course, doesn’t solve anything if you have already been attacked by a Ransomware virus and you don’t have any previously made file backups. In a case such as this, you’d have to really carefully consider the potential options you can go for and pick the one that best suits your specific situation. We will try to help you with that to the best of our abilities but know that, unfortunately, we cannot give you any guarantees with regard to the outcome of this Ransomware attack.
The Remk virus
The Remk virus is a threat recognized as a Ransomware infection that starts encrypting user files in order to lock them the moment it enters the system. The Remk virus can be removed, but to release the files, you’d need a special decryption key.
The hackers behind the virus seek to coerce you to send them money for that key and they even give instructions to their victims on how to transfer the ransom. The instructions are provided within a ransom message that the virus generates once it finishes the encryption. Usually, the message is in the form of a notepad file that is placed on the Desktop or inside any of the folders where encrypted files are stored.
If you have suddenly realized that you are no longer able to open your most important files and if there is such a ransom-demanding note somewhere on your computer, know that following the instructions from that note is not advisable. Even if you have the needed money and are ready and willing to spend it in order to release your files, it’s still not something you should do straight away. Instead, what we’d advise you to do first is to check the instructions in our guide and then follow them to see if they help you with the recovery of your files.
The Remk file encryption
The Remk file encryption is the process that this virus launches in your computer in order to block the access to your files. The Remk file encryption needs to be decrypted in order for the locked files to become accessible once again.
However, without the key held by the hackers, it may not be possible to release the files. Still, there are a number of things you can try in an attempt to release your data through alternative means. Some recovery suggestions can be found in our guide, but before you move on to them, do not forget to remove the virus by completing our removal instructions you will see next.
SUMMARY:
Remk Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply