This page aims to help you remove Acwzmain.accde Trojan malware. Our removal instructions work for every version of Windows.
Acwzmain.accde

Acwzmain.accde is a legit Microsoft Office file, but sometimes trojans can infect it.
Acwzmain.accde is linked to the recent malware threat called O97m/mamacse.f . The path C:\Program Files (x86)\Microsoft Office\root\Office16\ACCWIZ\ACWZMAIN.ACCDE has been detected as part of the Trojan horse O97m/mamacse.f.
The types of harm that a virus of the Trojan Horse family could do to your computer are many and in a lot of cases, the users don’t even know what part of their system is being targeted by an ongoing Trojan Horse infection. What’s even worse is that most Trojan Horse victims tend to be unaware of the infection in their machines due to the sneaky nature of the Trojans. Considering all those, as well as many other aspects of this malicious group of programs, it is essential that every PC and Mac (that’s right, even Macs aren’t immune to Trojan Horse infections!) has some basic understanding of how those malicious programs operate, how they can enter a given computer, what damage they may cause in it and, most importantly, how one could manage to eliminate such a virus before the task of the Trojan gets completed.
Acwzmain.accde Trojan (O97m/Mamacse.f)
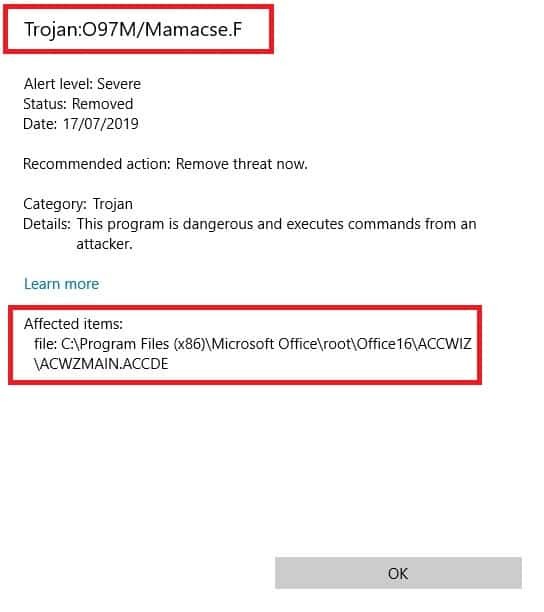
Acwzmain.accde has been infected by the O97m/Mamacse.f Trojan Horse
There is one particular Trojan Horse virus that we will be focusing on in this post. Its name is O97m/Mamacse.f and it is one of the newer Trojans – it was recently reported as many users have had their computers attacked by it in the last couple of days. One problem with this threat is that there needs to be done more research on it so that everything is known about its capabilities. This is why we cannot tell you with hundred percent certainty what its goal may be if it gets to you. Many of the Trojan Horse representatives (Idle Buddy, “Drive by exploit”) have varied abilities and, because of that, could be used in multiple ways.
In some cases, the infection may be tasked with taking over your computer in some way. This is usually done in order to make the attacked machine part of the massive network of infected computers that the Trojan controls. Such networks are known as botnets, as the machines in them are remotely controlled by the hackers behind the Trojan and are collectively used for tasks such as mining BitCoin, conducting large-scale online attacks (DDoS) or distributing other types of malware such as Ransomware and Spyware via massive spam message campaigns. In such cases, there could be various symptoms of the infection like high CPU and RAM use, system unresponsiveness, software failure with many random errors, unauthorized deletion or modification of different files, folders and registry keys as well as many more.
In other instances, however, there may be no visible symptoms at all. This is mostly when Trojans like O97m/Mamacse.f are used as espionage tools. In those cases, the malware program may be able to collect sensitive data like banking details, online passwords and usernames, different important personal or business-related files, conversations and more. In those situations, the malware would be optimized for stealth and would probably not show any signs of its presence.
What to do when faced with Acwzmain.accde
If you are here, reading our article, that means that you probably know or at least suspect that Acwzmain.accde is messing with your PC or Mac. If that’s the case, then the guide we have below is definitely what we would advise you to use in order to eliminate the Acwzmain.accde Trojan Horse. And if, for some reason, the manual steps aren’t cutting it, you can also help yourself with the suggested removal tool we have linked below as it can allow you to automatically take care of the Trojan infection.
SUMMARY:
| Name | Acwzmain.accde |
| Type | Trojan |
| Detection Tool |
Remove Acwzmain.accde Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment