This article aims to help users remove ad.afy11.net malware from Chrome, Firefox, Internet Explorer and Safari, as well as their respective system.
ad.afy11.net malware is a fairy new type of malware virus which has been spreading extremely fast in the last few months. It usually infects computers through an unintentional interaction done by the user like opening an e-mail attachment, downloading data from suspicious torrent sites or even during the installation of what seems a legitimate software product. Most free software products include something like that masked as an unsuspicious toolbar, downloader or something similar in a process called program bundling – when the installer of one program can install multiple others.
Dangers that go along ad.afy11.net malware
ad.afy11.net malware may have a variety of negative effects upon your browser and system. For starter it significantly slows down your browsing speed. It may change your search engine search results leading you to a variety of fake pages which looks similar to the legitimate ones. Opening one of those pages may further infect your computer with other malicious software. ad.afy11.net malware may cause unwanted popups to appear preventing normal use of your computer. Quite often those pop-ups promote dating sites (with the appropriate pictures. Imagine happening on your work computer) or fake antivirus products. It is very important not to install anything coming out from those pop ups. Each time you click them or one of the fake links you risk infecting yourself with another type of virus, making it even harder to get rid of.
The most severe threat ad.afy11.net malware is its ability to potentially access your stored credit card accounts and details and send them back to its creator. The consequences of it could be severe and will most likely overweight the effect of some slower browsing and annoying pop ups. Some versions of ad.afy11.net malware can even track data stored on your computer hard drive or even give unauthorized access to your computer.
SUMMARY:
| Name | ad.afy11.net |
| Type | Browser Hijacker |
| Detection Tool |
Remove ad.afy11.net Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
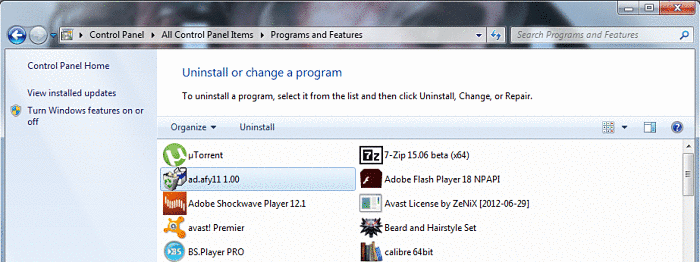
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Why wouldn’t one simply run Windows defender and have it remove it for you?