*Source of claim SH can remove it.
Akamaihd
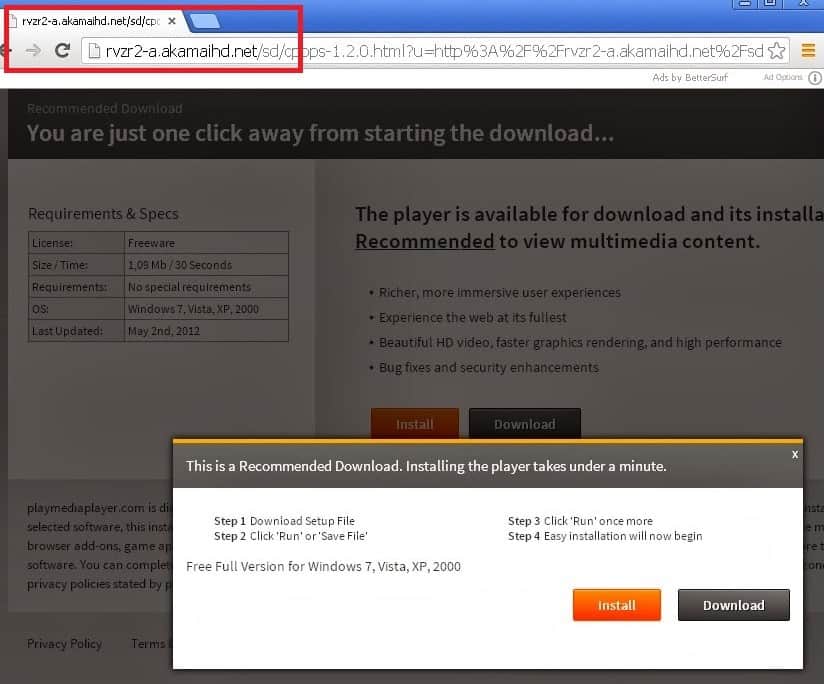
Akamaihd.net is a content delivery network primarily used to speed up websites. It is very often abused by suspicious websites for webpage redirects and more. Numerous complaints about Akamaihd.net include webpage redirects, unwanted advertisements and unapproved changes to the user’s browser.
Akamaihd.net
If you are looking to remove Akamaihd.net from your Mac:
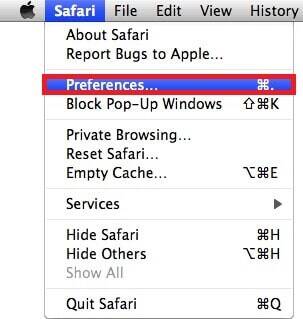
- Go to the Preferences tab in Safari (or any other Mac browser).
- Check the Homepage tab. Make sure that your homepage is the one you have selected and not search28374278-a.akamaihd.net or something similar.
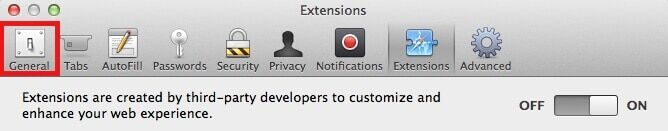
- Now go to the Extensions tab.
- Look for any Akamaihd.net extension as well as other suspicious entries.
- Remove any Akamaihd.net extension and other unfamiliar ones.
Search28374278-a.akamaihd.net
Search28374278-a.akamaihd.net is a website often used as a redirect destination for the akamaihd.net affected users. Search28374278-a.akamaihd.net should be immediately closed and not interacted with in any way.
Websites associated with the Akamaihd virus include but are not limited to:
- am-a.akamaihd.net
- asrv-a.akamaihd.net
- assetsnffrgf-a.akamaihd.net
- cdncache-a.akamaihd.net
- default120617-a.akamaihd.net
- default21076355-a.akamaihd.net
- default01088758-a.akamaihd.net
- default290967113-a.akamaihd.net
- default06091388-a.akamaihd.net
- default290941114-a.akamaihd.net
- download-a.akamaihd.net
- fbcdn-dragon-a.akamaihd.net
- fbcdn-gtvideo-a.akamaihd.net
- fbcdn-external-a.akamaihd.net
- fbcdn-sphotos-a-a.akamaihd.net
- lumiere-a.akamaihd.net
- pxlclnmdecom-a.akamaihd.net
- search6188182-a.akamaihd.net
- search9693448-a.akamaihd.net
- search0184386-a.akamaihd.net
- search82298264-a.akamaihd.net
- search8952443-a.akamaihd.net
- search93117247-a.akamaihd.net
- search9683493-a.akamaihd.net
- search46107304-a.akamaihd.net
- search4315454-a.akamaihd.net
- searchinterneat-a.akamaihd.net
- soprod-a.akamaihd.net
- steam-cdn-a.akamaihd.net
- steamuserimages-a.akamaihd.net
- lkysearchds1086-a.akamaihd.net
- lkysearchds5012-a.akamaihd.net
- lkysearchex1488-a.akamaihd.net
- lkysearchds9437-a-akamaihd.net
- lkysearchds4694-a.akamaihd.net
- lkysearchds2884-a.akamaihd.net
SUMMARY:
| Name | Akamaihd.net |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Hijackers reveal themselves by altering the functionality and appearance of your browser and also by triggering irritating page redirects and ads generation. |
| Distribution Method | Most hijackers get distributed through spam letters, deceitful ads and low-quality downloads with the hijacker bundled with them. |
| Detection Tool |
*Source of claim SH can remove it.
If you are being constantly redirected to Akamaihd.net then you probably have a browser hijacker. There are several methods through which this type of malware has been spreading in recent years. By far in most cases, the virus has reached your system through an installation bundle with another software. Most likely the carrier would be a freeware program or game, and often times you will not even notice that Akamaihd.net Virus has been installed until it’s too late. The only way for you to prevent this from happening in the future is to very closely monitor what exactly is being installed onto your hard drive, do not give permission for anything that might seem unfamiliar or strange to you.
You should try your best to avoid interacting with the pop-ups altogether. Don’t click on the advertisements in any case. Some of the displayed information might be legitimate but most often you will be redirected to some phishing site where if not careful your personal data might get stolen. This specifically implies to the billing information, do not be fooled even if the website looks like something real, it can be very tricky to notice the difference from the real thing. Also, you should not under any conceivable circumstances download software prompted by Akamaihd.net. Even if it’s not a virus, which it most likely will be, this software will be at very least some sort of bloatware. Meaning a completely useless for your program that will eat lots of your Mac resources for breakfast without any practical implications whatsoever.
Akamaihd.net is the stereotypical malware virus. Its type – Adware. The main function of this malicious software is to spawn endless advertisements onto your screen without your explicit permission to do so. Most often the “trigger” for the appearance of the aforementioned Ads would be you loading a web page or opening a link while browsing. As you have noticed these pop-ups are very annoying and can quickly become quite bothersome especially if you are operating on a company-owned device. Unfortunately, this is not the only negative side of Akamaihd.net Virus. This program will try to make you buy lots of stuff you definitely don’t need, mostly completely useless programs but in some cases even malware applications. For this reason, we think it a good idea to give you some do’s and dont’s when encountering the Ads.
In any case, you definitely need to remove this harmful software from your Mac and the sooner the better. Learn how with our free removal guide.
Remove Akamaihd on Mac Chrome
If Akamaihd as installed an extension in your browser, you can try to remove this extension and thus get rid of the unwanted hijacker. This may not always do the trick but it is a quick and easy to execute removal method that can save you lots of time trying to complete any of the more advanced uninstallation steps that you will see further down our Akamaihd removal guide.
- To remove the Akamaihd extension from Safari, open the browser, click on the Safari menu, and choose Preferences.
- Open the Extensions tab and there you will see the currently available extensions that are installed in Safari. If there is an item there with the Akamaihd name, select its Remove/Uninstall button to remove it from the browser.

- If there isn’t an extension with that name, look for other items that may not belong in the browser. If you are having difficult time singling out the extension placed in your browser by Akamaihd, then start removing all of the extensions, one at a time, and testing how the browser behaves after each removed add-on item. This will hopefully allow you to determine the one responsible for the Safari disturbances so that you can then safely bring back the other extensions that are not causing any problems.
- After you are done with clearing the browser from the unwanted extension(s), restart the computer, open Safari, and return to the Extensions’ section to see if what you have removed from there is still gone. If the unwanted extension has been added to the browser again without your permission, go to the next steps and complete them. Do the same if the browser keeps experiencing symptoms associated with Akamaihd.

*Source of claim SH can remove it.
Before you begin the removal of Akamaihd, you must first close Safari but the hijacker may sometimes prevent you from doing this so, if you cannot close Safari or the browser keeps opening after you close it, go to the Apple Menu and choose the option labeled Force Quit. From the Force Quit window, highlight the Safari entry and click on the Force Quit button to close the app.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
You must go to the Activity Monitor app of your Mac – you can access it from Applications > Utilities > Activity Monitor. When you open the Activity Monitor, search for Akamaihd among the list of processes. If you find a process with this name, select it and then quit it using the Quit/X button above the list. If you don’t find a process with the Akamaihd name or anything similar to that, then you should look for other questionable entries in the list – ones that seem to be using lots of RAM memory and/or CPU time without being connected to any resource-intensive programs that you are currently running.
If you see such a process, first Google its name to determine whether or not it is related to the OS of your Mac. If it is not, select that process from the Activity Monitor and click on then click on the Information icon. From the information window that shows up, select Sample and then, in the next window, select Save. Save the file to a location that will be easy to access (such as the Desktop).

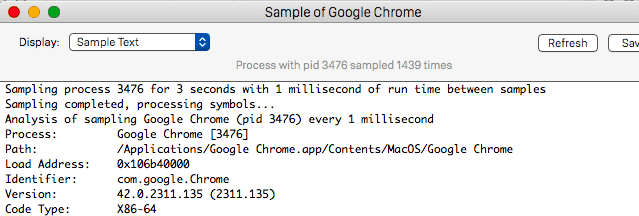
Next, scan the process sample file using the next online malware scanner. It will quickly determine if there’s any malicious code contained in the file.

If the sample file gets flagged as containing malware code, you should Quit the process from where the sample came.

Open Safari again but this time hold Shift pressed while starting the browser. This will Safe Launch Safari which means that the browser won’t load any pages that were opened during the last browsing session. This must be done because if any hijacker-related pages load again, this may hinder your attempts to remove the unwanted software. In case the Safe Launch didn’t work and pages related to Akamaihd load again, Force Quit the browser like in Step 1, block your connection to the Internet and try to Safe Launch the browser once more.
- To disconnect your Mac from the web, you can either pull out the Ethernet cable from your Mac if that is how the machine is connected to the Internet or, if you are using Wireless connection, you can press and hold Option from your keyboard, then click on the Wi-Fi menu, and click on Turn Wi-Fi Off. To turn back on your Wireless connection, use the Turn Wi-Fi On button from the same menu.

Once Safari is safe launched, check the browser’s extensions again and if any of the ones removed earlier by you have been reinstalled automatically, delete them once again and then visit the Privacy section of Preferences.
In Privacy, you must select Remove All Website Data and confirm the action to delete any data remnants from Akamaihd that are stored in the browser. This action will delete site cookies and browser cache data, hopefully removing anything that could be related to the hijacker. However, remember that this action will also result in getting logged out of all your site accounts so you must know you usernames and passwords for them to be able to enter them again.

Next, open General from the Safari Preferences and make sure the homepage address of the browser is one approved by you.
Oftentimes, a hijacker would alter this in its attempts to spam you with more ads and automatic page-redirects so you must make sure that the browser’s homepage isn’t hijacked and that it’s address is from a legitimate and reliable website.

The last thing you must do in Safari is to clear the browsing history and you can do this from the History menu of Safari. Click on it and then select Clear History. Safari will give you the options to choose a time period for which the history would be deleted and we recommend that you pick the longest one (from the beginning). Select the Clear Browsing History to complete the action and wait for the deletion to finish – in instances where the browsing history hasn’t been deleted in a while, this may take a couple of minutes to complete.

Browser hijackers oftentimes affect not only the main browser but also any other ones that may be installed on the computer so you must clean them too from any residual hijacker data.
![]() Removing ads from Firefox for Mac:
Removing ads from Firefox for Mac:
First, we will show you how to do this on Firefox. Open the browsing app and select its menu – in it, you will see an Add-ons button so select it and then select Extensions. This will bring you to the extensions page of Firefox where you must find and delete the extensions that you think may have been placed there by Akamaihd. Needless to say, if there is an item in the extensions list named Akamaihd (or anything similar), you should delete it too.

Next, you must clear the browsing data like you did with Safari – instructions on how to do it are available on this page.
![]() Removing ads from Chrome for Mac:
Removing ads from Chrome for Mac:
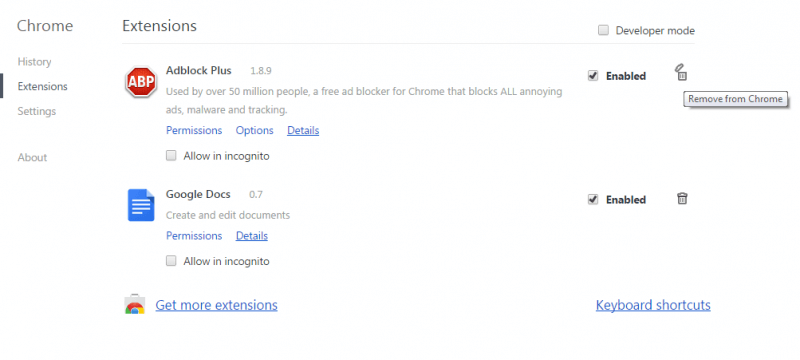
To remove extensions installed by the hijacker from Chrome, start the browser, enter the browser’s menu and, from the More Tools/More Options sub-menu, select Extensions. Uninstall the potentially unwanted, suspicious, or unneeded extensions as well as those that carry the Akamaihd name.
Next, choose Settings from the browser menu, select Search Engine from the right side of the screen, and click on Manage Search Engines. This will show you what search engines the browser uses and if any of the entries listed there seems to have anything to do with Akamaihd, it must be removed by clicking on the three-dot icon next to the specific search engine and then clicking on Remove from list. Make sure that the only search engines used by Chrome are reliable and familiar ones that you know you can trust.
To finalize cleaning Chrome, visit this page and follow the guidelines there that will show you how to delete any leftover hijacker data from the browser.
Final Notes
If you have successfully completed the steps from this guide, the hijacker should no longer be on your Mac. However, in some rare cases, the unwanted software may have managed to stay in the system, in which case we suggest contacting us through the comments section and/or using the professional anti-malware tool we have recommended on this page.

Thank you so much for the video….I’ve searched everywhere for a solution to this virus and nothing else seemed worked.