“Are you the one in the video” on Facebook
The most probable reason why you’ve landed on “How to remove guide”, and on this article in particular, is because you’re probably dealing are with a nasty Trojan Horse infection called “Are you the one in the video”.”Are you the one in the video” is a new addition to the growing Trojan Horse malware category and represents a great risk for your system’s safety.
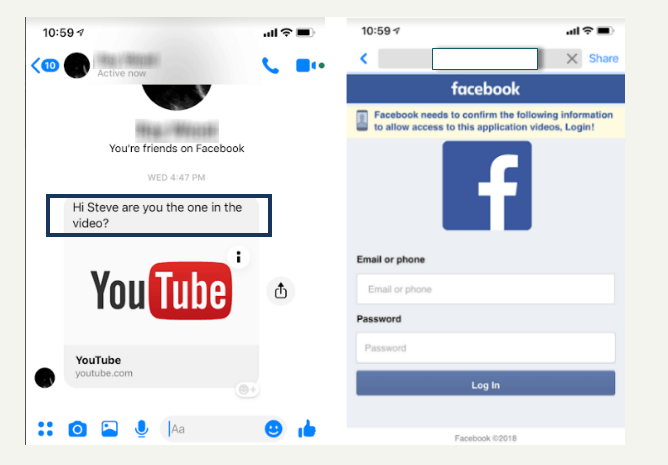
Scammers often send legitimate-looking texts from fake or hacked accounts with a message urging you to click on the link.
That’s why, in the next lines, we will provide you with some important information about its harmful abilities, and about the methods that you can use to quickly detect and remove it.Experts warn users that Trojans are very sneaky threats which can oftentimes mimic absolutely legitimate-looking files, images, ads, software installers, email attachments and more. What is more, some sophisticated Trojan-based threats may operate under the name of regular system processes in order to hide their presence from the victims and to prevent the latter from taking actions against the malicious code.
OMG Are you the one in the video on Messenger
Obviously, if you fail to detect an infection like “OMG Are you the one in the video” in your system on time, your personal information and other sensitive data are likely to leak into the hands of inappropriate people. As a result, you may face huge data or financial losses, become the victim of banking fraud, experience serious system issues and even identity theft in the long run.
Additionally, due to the presence of the Trojan horse on your computer, you may notice that the machine may start to behave “weird” and get rather sluggish. The cause of this could be related to the ability of the malicious software to exploit the resources of the computer for other processes, and tasks, such as cryptocurrency mining, distribution of spam, distribution of viruses, Ransomware, Spyware, and other malware, and more. In other words, the system may be forced to launch different activities and operate at high levels for long periods of time without that being related to any activity that has been initiated by you. This can lead to system crashes, increased latency, and freezing.
So, if you have suspect that “Are you the one in the video” might be hiding somewhere inside your computer, we advise you to check your entire system with a professional malware removal tool, such as the one on this page, and if the check results show an actual threat, you need to take the needed steps to quickly remove it. Keep in mind, though, that this type of malware is programmed to hide deep in the system, and it is of utmost importance to correctly detect the real Trojan-related files because deletion of something else may lead to even greater system damage. For this reason, you should not attempt to remove “Are you the one in the video” manually if you are not sure which files are the ones that need to be eliminated. If you still prefer the manual method, try to stick to the instructions fro the Removal Guide below. Otherwise, to avoid potential problems while trying to clean the system and protect your personal information, it’s better to use the automatic removal tool.
Ways to protect your system from Trojans
One of the most common ways in which malicious programs like “Are you the one in the video” find their way into the system is through spam email campaigns where attractive and legitimate-looking emails and attachments are used as a bait. Unreliable web pages that offer you the installation of suspicious software are another frequently used distribution method. It is usually difficult to determine if the applications from such sites are legitimate and users oftentimes tend to install different free programs without paying much attention.
Therefore, it is very important to download and install apps only from authorized web pages, to stay away from sketchy sites and their ads, and use your common sense before opening different emails and email attachments.
SUMMARY:
| Name | Are you the one in the video |
| Type | Trojan |
| Detection Tool |
Remove Are you the one in the video Facebook Message Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment