This page aims to help you remove Chaos CC. Our removal instructions work for every version of Windows.
If your system has been infected with a Trojan Horse named Chaos CC, it is highly recommended that you remove this hazardous malware from your system as quickly as possible. Trojans like this one are very invasive programs, that can cause different problems to your PC, and require special attention in order to be deleted successfully. There’s no need for panic, tough. If you don’t know how to deal with such a malware, or you don’t want to pay to an expert from your area to resolve your issue, here’s a free removal guide that can assist you with the detection and removal of Chaos CC.
The Chaos CC Hacker Group
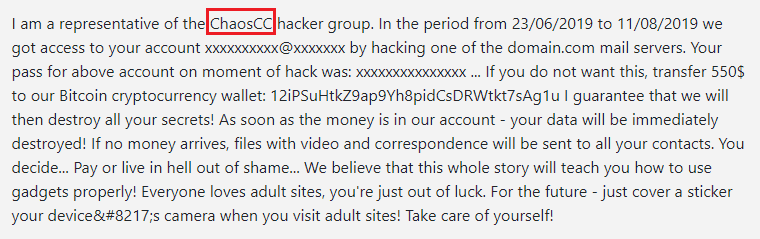
Email from the Chaos CC Hacker Group.
Our “How to Remove” team is devoted to assisting users like you combat malware and different viruses, so, in the next lines, we will do our best to provide you with a comprehensive explanation, and guidelines on how to eliminate the nasty Trojan that has invaded you. You’ll learn how harmful Chaos CC could be, what damaging actions it can do, and most importantly, how to prevent a future infection of this kind. Ultimately, we’ve included some prevention tips that might help you keep such Trojans away from your system in the future, as well as a removal guide with a professional removal tool that will show you how to get rid of this threat.
Threats like Chaos CC are very advanced computer infections that greatly differ from viruses and other malware. These malicious pieces of software typically pretend to be seemingly harmless pieces of web content such as pictures, email attachments, different free download files, links, pop-up ads, and even songs or videos. A random click on a well-camouflaged malicious transmitter like the ones mentioned above is all it takes to get infected. Usually, the users don’t realize when the infection occurs as it passes without any noticeable symptoms. Therefore, the best way to catch the threat on time is to use a reliable security program and avoid interaction with sketchy and unfamiliar web content.
What wrongdoing can Chaos CC do on your machine?
The hackers who develop Trojan-based threats are cyber criminals who are interested in different criminal deeds and would definitely do no good to your computer once they infect it. That’s why having a malware like Chaos CC inside the system is one of the worst things that could happen. Moreover, it can be a difficult job to detect and safely remove the threat from your system without proper guidelines. The Trojan’s damaging effects on your computer may include data stealing, spying, keeping track of your activity, corrupting your files, collecting personal information and passwords, or even installing other malware such as Ransomware. Unfortunately, these are just some of the criminal activities a malware of this type is capable of carrying out, and there are certainly more things that such Trojans could do. Therefore, we advise you to remove it as soon as possible with the help of the instructions in the Removal Guide below.
SUMMARY:
| Name | Chaos CC |
| Type | Trojan |
| Detection Tool |
Remove Chaos CC Hacker Group Email
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment