This page aims to help you remove Chromesearch.win “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Chromesearch.win “Virus” is a form of software that might take control of all the browsing apps installed on your device, such as the popular Chrome, Explorer and/or Firefox (as well as pretty much all other browser apps) could also be targeted; and might lead to some really annoying modifications of the affected apps:
- Perhaps you will get redirected to unknown websites while you are on the web all the time. Thus, your surfing experience as a whole might be affected in a negative way.
- Your browser apps may launch the production of very many online ads. Banners, pop-ups and bright boxes could appear all over your browser apps, each time when you try to browse the Internet.
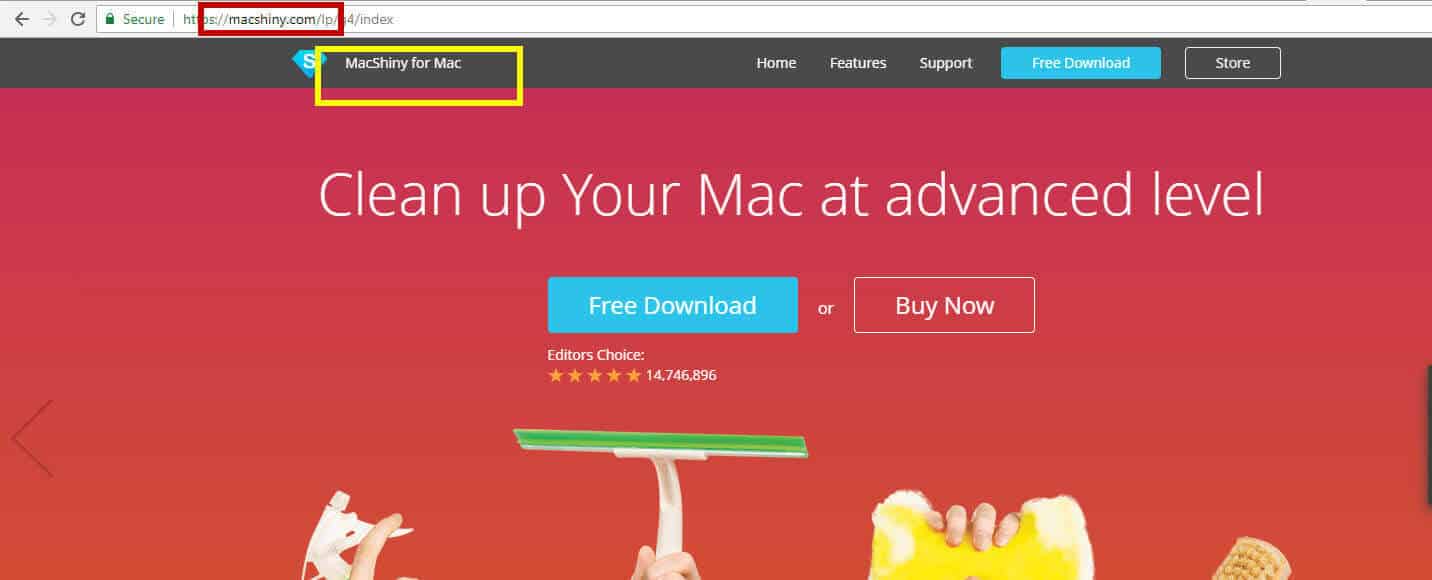
- Chromesearch.win “Virus” may even be able to substitute your usual browser homepage and search engine with some new, oftentimes completely unfamiliar ones.
This software’s family is called browser hijackers. Such programs do not really represent serious cyber threats. However, no user wants to get infected by them as they are really annoying and might seriously irritate the entire browsing experience. As you can see, browser hijackers have been characterized as a kind of software, generally focused on affecting all the installed browser apps. Actually, no other component of your system could really be modified by this program. Chromesearch.win “Virus” may only access and change your browser apps to some extent but does not harm your PC in any way.
What you may not know about Chromesearch.win “Virus” in particular
You may not be aware of the fact that all of the programs from the browser hijacker category are normally aiding the marketing industry. The efforts of manufacturers, service providers and programmers to come up with an online means of promotion (as nowadays people spend a lot of time in front of their computers) have resulted in the creation of such advertising-oriented software. Really, the redirecting and ads Chromesearch.win “Virus” and its sibling programs could cause are nothing different from all the ads we are exposed to on the radio or on TV. These are their online versions. In fact, the exact name of this online advertising scheme is pay per click. In general, it means that the more ads we are exposed to, and the more redirecting occurs, and the more new homepages are displayed; the more money the creators of hijackers could make as they are paid on the basis of the seen/ clicked on ads.
How to deal with this issue:
To remove an ongoing contamination, scroll down and find our removal guide. To prevent a future infection, master the installation skill we have described above and learn to invest in good anti-malware tools to keep your system safe.
Is this program just annoying or does it indeed cause harm?
We are more than sure that Chromesearch.win “Virus” is NOT really a member of any malware category. This program is nothing but an easy means of income for developers and an efficient means of promotion for the people who want to gain more exposure for what they produce. Of course, there are some substantial differences between hijackers and most common forms of malware we are aware of. While any standard hijacker could do no more than simply “hijack” your browser apps and somehow modify them, the Ransomware and Trojan-type programs can actually access all the components of your PC and seriously damage them – either by destroying something or locking up some vital data. What’s more, no hijacker is really able to self-install on your device while Ransomware and Trojans are perfectly able to do that without your knowledge and clear consent.
How browser hijackers are likely to get distributed:
When discussing Adware and/or browser hijackers, we have to point out that the major source of both advertising kinds of apps is called program bundling. This is actually the process of mixing games and apps together, and spreading them in bundles, normally for free. Typically, the created bundles are harmless combos, but only if you manage to install their contents in the correct manner. There will be nothing bothering you and you will be able to enjoy some new free apps and programs, you just have to bear in mind that the secret to a safe installation process is choosing the ADVANCED (or sometimes CUSTOM) installation feature at all times and under no circumstances opting for the easy Default or Automatic installation features.
SUMMARY:
| Name | Chromesearch.win |
| Type | Browser Hijacker |
| Detection Tool |
Chromesearch.win “Virus” Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

i ve got suspicious local host
Can you send us the IPs so we can tell you if you should remove them from the file?
Is it possible the virus doesn’t show up in safe mode?
Depends. Where are you looking for it?
127.0.0.1 cpm.paneladmin. pro
127.0.0.1 publisher.hmdiadmingate. xyz
127.0.0.1 distribution.hmdiadmingate. xyz
127.0.0.1 hmdicrewtracksystem. xyz
127.0.0.1 linkmate. space
127.0.0.1 space1.adminpressure. space
127.0.0.1 trackpressure. website
127.0.0.1 doctorlink. space
127.0.0.1 plugpackdownload. net
127.0.0.1 texttotalk. org
127.0.0.1 gambling577. xyz
127.0.0.1 htagdownload. space
Those IPs are certainly not supposed to be in the Hosts file, remove them and save the changes to the file.
Remove those IPs from your Hosts file as they might be responsible for the issue you are facing.