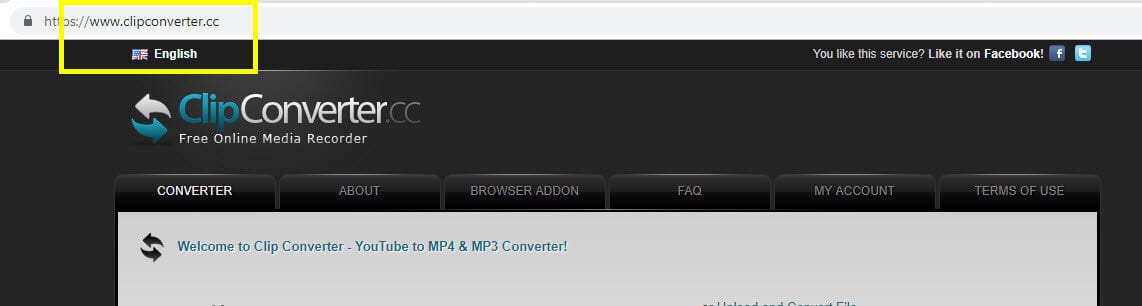
This page aims to help you remove Clipconverter.cc “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Clipconverter.cc is not among the worst pieces of software that you may encounter. This application doesn’t have the harmful abilities of a Ransomware cryptovirus or the stealthiness of a Trojan horse infection. However, if you have it on your PC, then you are very likely to experience some of the following disturbances:
- Generation of annoying and hard-to-remove ads, pop-ups and banners on your screen.
- Modifications in the settings of your browser such as homepage replacement, new-tab page replacement or automatic page-redirects.
- Installation of new search engine tools, unfamiliar toolbars, and browser add-ons.
- Traffic data collection and exposure to sponsored commercials and promotional websites.
Browsers such as Chrome, Firefox, Edge or Explorer could easily get hijacked by this or any similar application and be forced to operate in the above-mentioned way. They may start to become unresponsive to the users’ search queries and may display certain links, ads or web pages, which are predefined and are thus supposed to get traffic and exposure. Other possible unwanted effects of having Clipconverter.cc “Virus”on the computer may include sluggishness, sudden browser crashes, and excessive exposure to pay-per-click ads. These are potential results of the quite aggressive online advertising activity, which the software is trying to implement. Luckily, there is nothing harmful or criminal in such activity. Applications like Clipconverter.cc “Virus” are not viruses created to destroy the user’s system but online advertising tools, that are supposed to promote certain products, services, offers, and software programs through the users’ browsers. Due to their rather aggressive behavior, however, such pieces of software are better known as browser hijackers. Many web users face the disturbance of dealing with browser hijackers on a daily basis and that’s why it is really important to understand their nature in order to effectively handle them without risking the safety of your computer.
The representatives of this software category are usually challenging to uninstall, but definitely not as hard as dealing with a computer virus. Still, for the effective and safe removal, we usually recommend that our readers either use a professional removal tool or the instructions of a trusted removal guide like the one below.
Why do so many people fear the browser hijackers?
The fear and panic that the browser hijackers tend to cause are usually not justified because such pieces of software do not initiate any criminal activities and do not aim to cause harm to the users. However, many people seek methods to have them uninstalled and remove all of their imposed browser changes and ads from their computer. The main reasons for that are the obvious ads irritation and browsing disturbance, which are very likely to appear the moment such software gets installed on the system as well as the potential interaction with security hazards. An application such as Clipconverter.cc might not only install some sponsored custom search engine tool or toolbar on your default browser without your approval but may also force the browser to redirect you to some predefined web pages, links, and offers, which generate income from paid clicks and traffic.
This uncontrolled stream of random ads and redirects, as well as the browser’s changes might be quite unpleasant and make your machine more likely to get exposed to different types of malware and viruses such as Trojans, Rootkits, Ransomware, or Spyware. That’s why, the general advice we usually give to our readers is to be cautious when applications like Clipconverter.cc operate on their system and try to avoid interaction with their advertising materials because the legitimacy of the randomly popping-up ads might not be verified and there could be content with malicious or fake origin.
How can applications like Clipconverter.cc get installed on your system?
Typically, the users may get potentially unwanted or hazardous applications on their systems when they interact with different spam messages, shady websites, torrents, different email attachments, ads, and free download links. In the case with the browser hijackers like Clipconverter.cc , however, the most probable way to have them installed on the computer is when you perform a careless software installation of a given application bundle without customizing its configuration settings. This is so because, in most of the cases, the browser hijackers are bundled with other free applications, attractive toolbars, browser add-ons or software update installers. Usually, they are promoted as “optional” or “bonus” components to the main application and get installed alongside if you don’t disable them manually. That’s why, in order to prevent them from getting installed, you should always make use of the Advanced/Custom installation settings from the setup wizard and remove any components that seem potentially unwanted or shady.
SUMMARY:
| Name | Clipconverter.cc |
| Type | Browser Hijacker |
| Detection Tool |
Remove Clipconverter.cc “Virus”
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment