This page aims to help you remove Darknet Email Hack Scam. Our removal instructions work for every version of Windows.
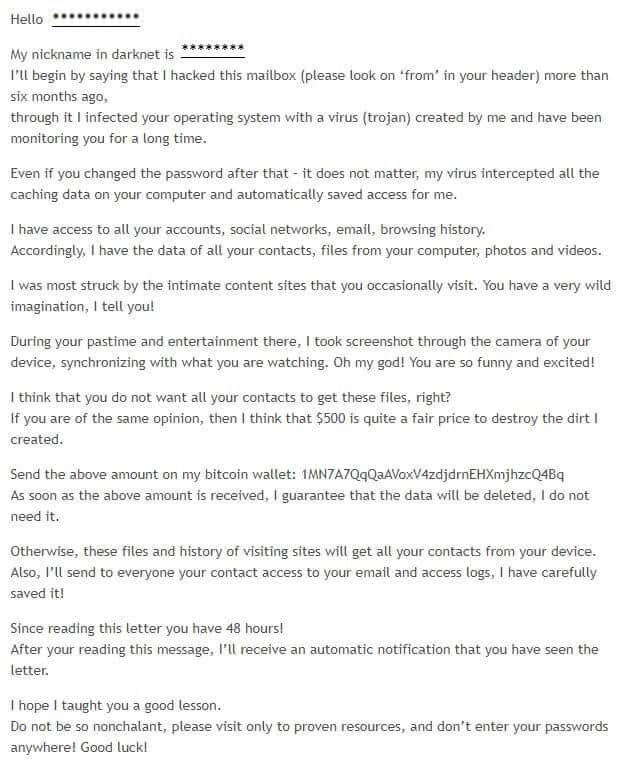
If you are the target of an Darknet email hack scam, then you might be interested to continue reading this article. It is truly a scam, trying to con you into paying bitcoins. However it might also be an indication that you indeed have security issues.
PC virus programs are everywhere and if you do not learn how to avoid them and keep them away from your computer, you are sure to face a lot of malware-related issues. It is no secret that one of the biggest groups of malware out there is the so-called Trojan Horse virus category. Malware programs that belong to this group are known for being extremely sneaky and dangerous as well as highly-versatile which makes this class of computer viruses some of the nastiest and most dangerous ones. One recent addition go the Trojan Horse family is the so-called Darknet Email Hack virus and today, we are going to tell you more about its typical traits so that you’d know how to keep your computer protected against it. However, since there’s already a quite considerable number of machines infected by this malware threat, we understand that it is quite likely that a lot of this article’s readers are actually users who have already had their PCs compromised by the insidious Darknet Email Hack. Because of this, we have also prepared a manual guide for removing this virus from nay infected machine. Any of you who need to learn how to get rid of Darknet Email Hack can do so by scrolling down this page and taking a look at the removal instructions available in the guide. Just make sure to closely follow the listed steps and if you aren’t sure about something you can ask us in the comments to further explain the guide and give you additional help regarding the virus’ removal. We have also added a recommended software tool inside the guide that you can also use in combination with the instructions to really make sure that there’s no malware data left inside your system. Just make sure that you do everything in your power to get rid of the insidious Trojan Horse threat as it is essential that the malware gets removed ASAP.
The invisible threat
We already mentioned how sneaky and stealth Trojans are and here we are going to elaborate upon that as it is really important to get a better understanding of how such a malicious virus could get inside your computer and what you can do in order to intercept it on time. First and foremost, we need to tell you more about the moment of the infection. In most instances, the user doesn’t even realize that a piece of malware such as Darknet Email Hack has managed to compromise their PC. Oftentimes there are no visible indications making it difficult to spot the threat. Also, most of the time, the sources of those viruses are actually disguised as something that doesn’t look threatening – it could be an advert at some website, a spam e-mail attachment, a (fake) update request, a pirated program installer or some other piece of online content. There really are many options. However, there’s still a way to avoid most potential malware sources – just stay away from online locations that have low reputation and never click on anything that might not be safe. Although Trojan Horse sources are typically well-disguised, it is still not that difficult to tell if something that you see on the Internet might be a security risk.
Now, let’s assume that the infection has already occurred – how could it be detected? Unfortunately, symptoms are normally rare and they could vary depending on the specific case so we can’t really tell you what to expect for sure. Some possible examples of Trojan infection red flags are increased RAM, CPU and GPU use as well as sudden crashes, errors and freezes, PC slow-downs, overall system instability and any other kind of irregularity. However, if you really want to be able to detect such threats, we advise you to equip your machine with a strong and reliable security program such as a high-quality antivirus or anti-malware tool. Just remember that in some cases even such a program might not be enough to detect the threat which is why you must still be watchful and vigilant.
Damage?
Trojans are known for being able to execute different tasks depending on what the hacker needs them to do making this malware class highly versatile. Some examples of what a virus like Darknet Email Hack might be able to do are system and/or data corruption, personal espionage, money or data (personal and professional) theft, hard-drive formatting as well as infection with additional viruses (most commonly, Ransomware viruses). In some occasions, the hackers seek to establish a botnet of thousands of infected machines and then use the compromised computers for illegal and shady tasks like DDoS attacks, further distribution of the virus through spam messages, cryptomining using the infected computer’s resources, etc. The list of potential Trojan Horse uses goes on and on but we really do not need to mention every possible way such a virus could be exploited. The important thing is that you realize the importance of eliminating this threat and keeping your machine safe in the days to come.
SUMMARY:
| Name | Darknet Email Hack Scam |
| Type | Trojan |
| Detection Tool |
Remove Darknet Email Hack Scam
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment