This page aims to help you remove Domclickext.xyz “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
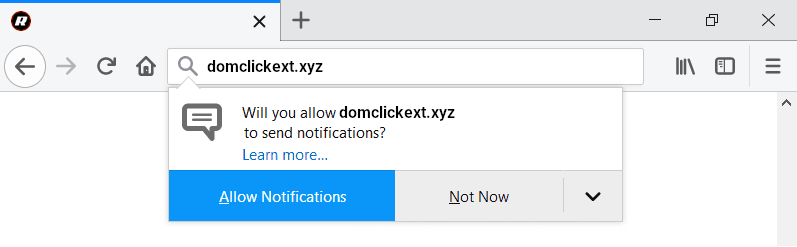
Will you allow domclickext.xyz to send notifications
Allow Notifications | Not Now
Do not press “Allow Notifications” otherwise you will be spammed with pop-ups and ads
If the ads that show up in your browser are more than usual and they don’t seem to be restricted or coming from any particular site or page that you are visiting, then this may be an indication that there is a browser hijacker present in your system. The browser hijackers are software pieces that typically try to promote certain sites and products through rather obstructive and aggressive means. Usually, the way this all happens is through a file-bundle – an installation package for another program that includes a clause that allows the installer to make changes in your browser, whatever that browser may be – Chrome, Edge, Safari and Firefox are the usual targets. If the user doesn’t uncheck the said clause, the installation process may set a new homepage to their browser, introduce an automatic page-redirect service in it, replace the search engine or modify the toolbar. All of this is meant to popularize the site, the products or the services of the hijacker’s creators as well as to flood the users’ browsers with ads for extra income through pay-per-click. One recent example of a browser hijacker software component is the one that tries to promote a page known as Domclickext.xyz. If you have this hijacker in your system, it would ceaselessly try to redirect you to Domclickext.xyz and show you ads related to it or ones that benefit the people behind it. Of course, this can quickly get quite irritating and also put your computer at risk of getting attacked by real malware like a cryptovirus of the Ransomware family or a Trojan Horse infection. The browser hijacker associated with Domclickext.xyz isn’t really a malicious piece of dangerous software – it is instead a relatively harmless component inserted in your browser to help popularize Domclickext.xyz “Virus”. However, the way it does its job could pose a risk to your system. You see, because of the different ads that may flood your screen and because can’t be sure if they won’t land you on some shady page with malware or Ransomware in it, it’s best if you keep away from them and also if you uninstall the source behind them. Uninstalling the hijacker and removing anything that may be related to it from your system will not only make the ads stop, but it will also allow you to effectively remove the changes that the browser hijacker has made to your browser while, at the same time, making your computer safer and less likely to get attacked by Ransomware, Trojans or viruses.
Avoiding this type of annoyances in the future
As we pointed out earlier, a hijacker may come to you as an element inserted in a file-bundle. Many software installers have some added clause that, when checked, allows them to install some additional app in the computer or make changes in the search engine, the toolbar or the homepage of the browser. You need to be on the lookout for such clauses and uncheck them when you see them unless you do actually agree with the changes that they could make. This is how most hijackers get distributed and it is something you shouldn’t disregard or ignore.
SUMMARY:
| Name | Domclickext.xyz |
| Type | Browser Hijacker |
| Detection Tool |
Remove Domclickext.xyz “Virus”
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment