This page aims to help you remove the FLVTO.biz Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
FLVTO.biz
FLVTO.biz is a browser hijacker type of malware. FLVTO.biz will add unwanted elements to your browser such as a search engine that doesn’t show relevant results, and a homepage filled with ads.
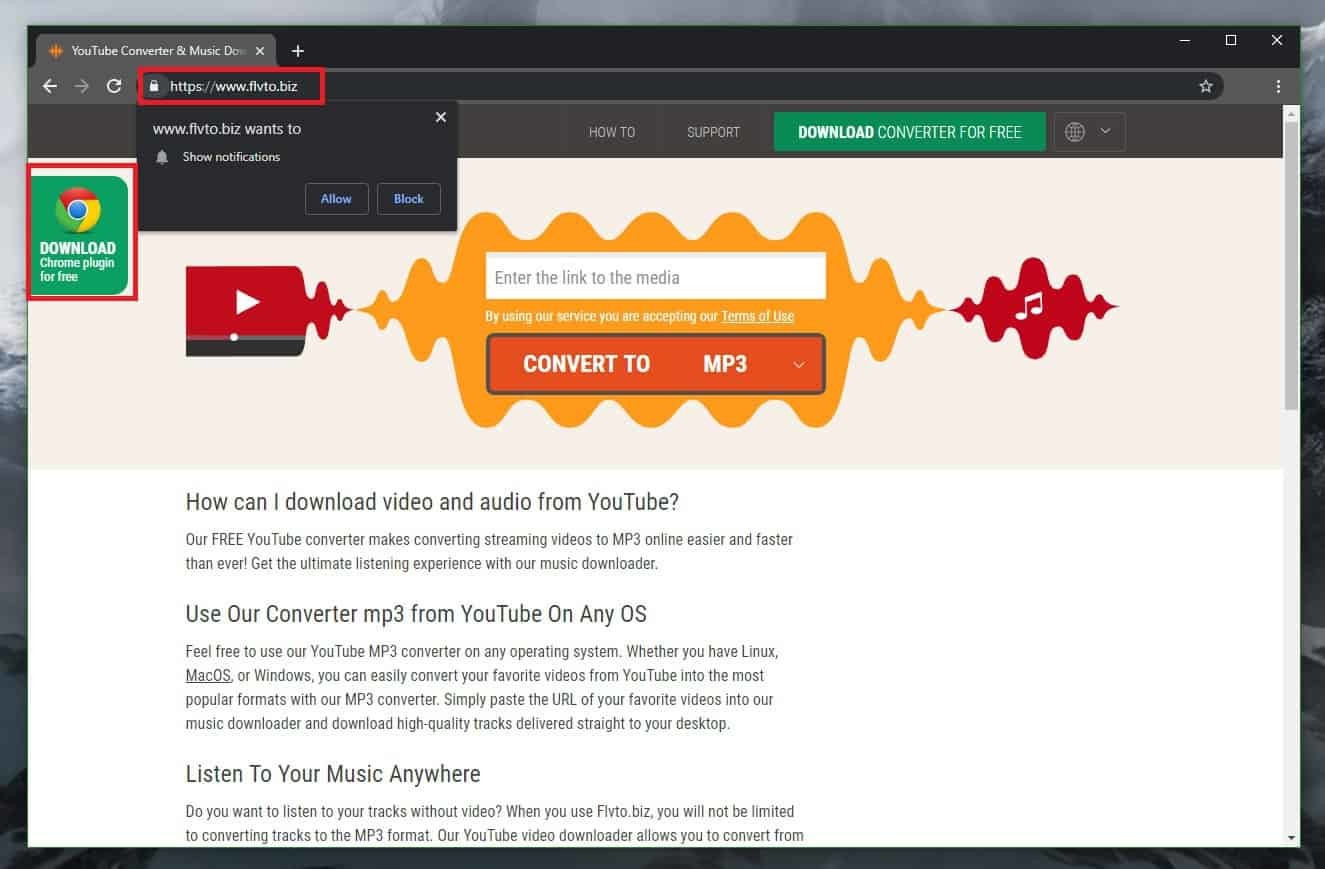
Homepage of FLVTO.biz
A browser hijacker that takes over popular web browsers like Chrome, Firefox and Explorer without an informed permission from the user has recently been reported to our “How to remove” team. The name of the application is FLVTO.biz and if you have it on your PC, then you have likely started to notice some aggressive ads, pop-ups and banners all over your screen as well as some unauthorized browser changes such as homepage or search engine replacements, which you haven’t approved. This is because the primary function of this application is to display sponsored search results within the normal searches of the user and also to page-redirect the web users to third-party sites. If you have started to see different sponsored links and click-prompts every time you open your browser, however, your sense of virtual security must has probably been decreased. And although the browser hijackers are generally not serious computer threats, in the majority of cases, their ad-generating and page-redirecting activities are considered as potentially unwanted. Usually, most of the web users don’t find the modifications that applications like FLVTO.biz, DevTool: Remove CSP, IFrame option, The Goodcaster impose on their browsers to be reliable or desirable. That’s why they seek methods to remove such applications and uninstall their changes.
Fortunately, once the hijacker is eliminated from the system, the preferred settings of the browser can be restored as if nothing has happened. This is because this type of software usually doesn’t have any harmful effects on the computer and, unlike viruses and malware (such as Ransomware, Trojans or Spyware), a hijacker isn’t typically aimed at corrupting, destructing or causing other damage to the OS. Uninstalling it, however, is highly recommended for preventing unwanted browser interruptions or future computer problems such as sluggishness and unresponsiveness caused by overuse of RAM and CPU. Moreover, the browser hijacker is only used to promote related sites and make money for its creators without actually providing any useful functionality for the end users. The longer such software remains on the system, the more it may fill the search results with sponsored links and redirect people to different web locations with the sole purpose of increasing the traffic to certain sites.
Getting exposed to random links and unfamiliar web locations, however, may not only be very unpleasant but may also hide certain security risks. For instance, the users can easily visit a dangerous website and not even realize that it is unreliable while using the FLVTO.biz redirects and sponsored links. They may also accidentally click on misleading messages or fake ads which could act as transmitters of nasty infections like Trojans, Spyware or Ransomware viruses. That’s why we strongly recommend you do not trust everything that gets displayed on your screen by this hijacker because some of the content may turn out to be misleading.
Remove FLVTO.biz
If you find the activities of FLVTO.biz as annoying or as undesired as we do and are looking for a way to repair your browser after it has gotten hijacked, we suggest you take a look at the instructions we have prepared for you in the Removal Guide below. Browser hijackers, unlike dangerous computer viruses, are relatively easy to get rid of, so do not miss the opportunity to uninstall the hijacker yourself or with the help of the professional removal tool that is added to this page.
SUMMARY:
| Name | FLVTO.biz |
| Type | Browser Hijacker |
| Detection Tool |
FLVTO.biz Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment