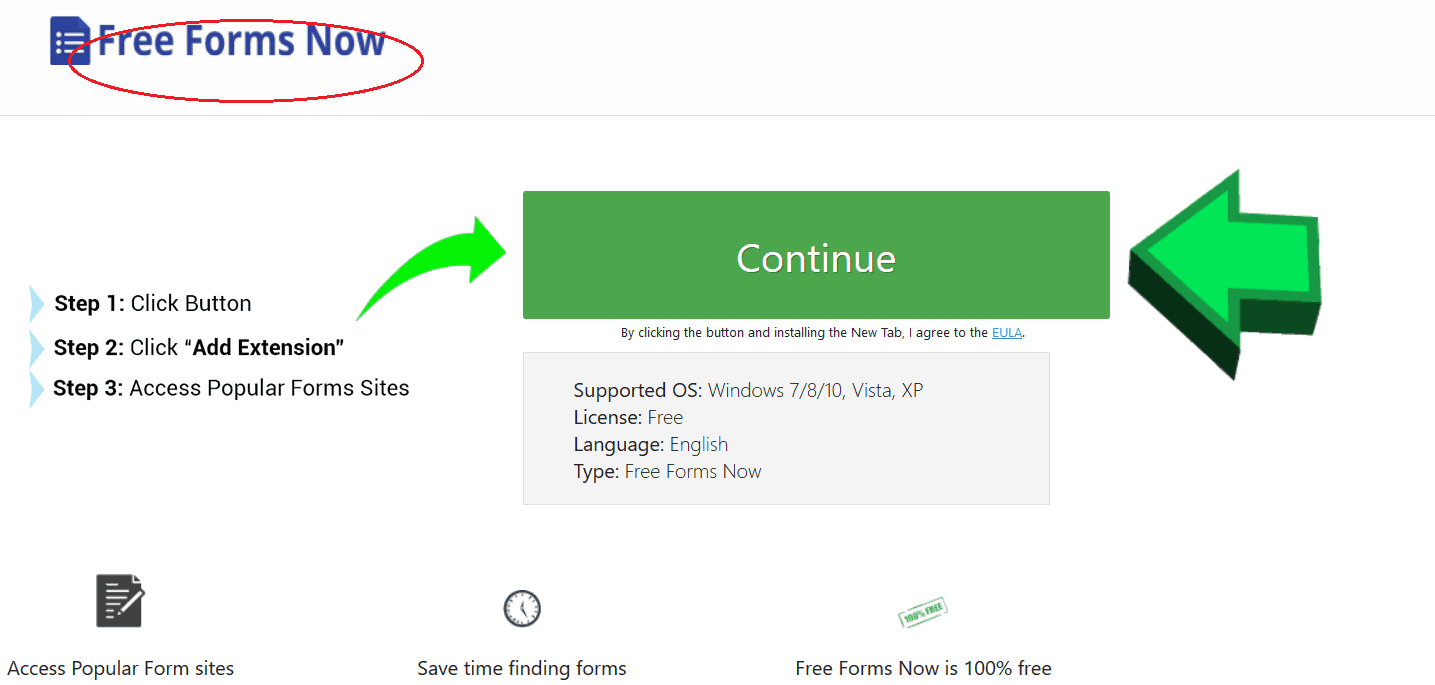
Freeformsnow
Freeformsnow looks like a normal browser component, which can easily get installed on popular browsers such as Chrome, Firefox, Explorer or others. However, the moment it starts to operate, Freeformsnow usually tends to modify the default browser’s settings by setting a new homepage, installing some undesirable apps, toolbars or search engines and spamming the screen with automatic page-redirects, ads, pop-ups, banners.
Freeformsnow.com Pop-up Ads
Freeformsnow.com belongs to the so-called browser hijacker software category and has some specifics, which need to be carefully addressed before you decide how to deal with it. The application is not malicious and does not contain harmful scripts similar to the ones that popular virus threats such as Trojans, Spyware or Ransomware have. That’s why, you should not get panicked if you find it on your system. In fact, after you remove it correctly, the browser hijacker is unlikely to have any negative long-lasting consequences to your PC. This type of software and the applications that fall under its category are nothing more than browser components which are used for aggressive online advertising. They are typically programmed to generate pay-per-click profits for their developers by displaying sponsored ads and redirecting the web users to paid links and web pages. However, many users find it challenging to deal with the hijackers’ ads-generation activity, which could be extremely aggressive and annoying. Users may also face some difficulties while trying to remove the popping messages from their screen or revoke the undesired changes because the hijacker would likely re-impose the said changes on the browser at the start of the next online session. That’s why, in most of the cases, a professional removal tool or a manual removal guide is needed for the effective uninstallation of the undesired software. In the next lines, you can find a suggested tool and detailed instructions for the uninstallation of Freeformsnow.com. We recommend that you carefully study them and chose the method that you are most comfortable with in order to get rid of the ads disturbance.
What issues may Freeformsnow.com cause if it remains on my PC?
Whichever method you decide to use in order to remove the browser hijacker, be it the manual removal guide or a removal application of your choice, the important thing is to ensure that the annoying application is no longer operating on your system. The reason is, if such a page-redirecting and ad-generating piece of software is present on your PC, it might create a lot of browsing-related disturbance and may contribute to your exposure of your machine to various security hazards. Now, as we mentioned at the beginning of this article, the browser hijacker is not a virus-like type of software but an advertising one. Therefore, applications such as Freeformsnow.com cannot directly harm your machine or initiate criminal activities. They are not capable of stealing sensitive information unlike what Trojan horses are able to do or encrypting your data which is something Ransomware cryptoviruses are known for. However, the ads that they may generate might not be the most reliable types of online content that you should interact with. The reason is, in most of the cases, the creators of the browser hijacker typically do not take responsibility for the reliability of the content that their software may display. The pages that you may get redirected to and the pop-up offers that may appear on your screen are usually randomly generated from some third-party ad platforms, some of which might be of questionable origin. With this in mind, it is perfectly possible that you may bump into some shady or hazardous web locations that could threaten your security. For this reason, it is a good idea to avoid clicking on the hijacker’s content and consider the unwanted app’s removal removal.
How to keep browser hijackers away from your PC in future?
A lot of browser hijacking applications may have official sites from where they could be freely downloaded. They usually are promoted as useful free tools, which could enhance your web experience and offer you the best deals on the Internet. These pieces of software are also distributed as “bonus” or “recommended” components to some other applications and could be found bundled in their installer, in different spam messages, free download links, torrents, and ads. That’s why, if you don’t want to land on your PC an application such as Freeformsnow.com, it is really important that you pay close attention to the software that you install and also that you customize its setup settings. Opt for the Advanced or the Custom installation every time when such options are available and take your time to review any pre-selected checkmarks that might allow some changes to your browser or to your system.
SUMMARY:
| Name | Freeformsnow.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Freeformsnow Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment