This page aims to help you remove From Doc to PDF. These From Doc to PDF removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
From Doc to PDF
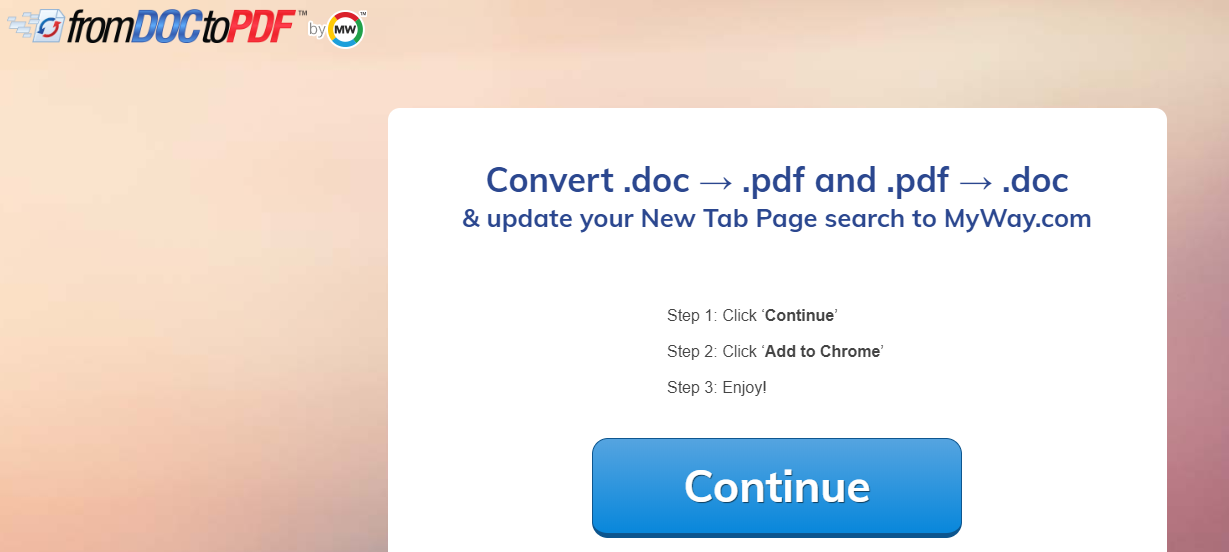
If you are seeing a large amount of pop-up Ads, banner attachments or getting redirected when you try to search in your Chrome, Firefox or IE browser, then chances are that From Doc to PDF is responsible. From Doc to PDF is a nasty program of the Adware family – it seeks to generate revenue for its creator by showering you with unwanted advertisements.
“From Doc to PDF” affecting browsers via bundling
Generally, these types of programs are not considered hazardous by security experts, but they can be very hard to remove. This is the main reason we created this article in the first place – to help people with it, as removing this Adware can require some specific steps in order to be successfully executed.
The “From Doc to PDF” Virus
First of all, we’d like to say that this is not actually a computer virus. A computer virus is a piece of code that infiltrates you computer’s defenses with malicious intent – encrypting your files, spying on your online transactions, stealing your accounts and passwords and more. Adware applications like From Doc to PDF are commonly mistaken to be computer viruses, but in reality they don’t fit the term – they are certainly annoying and they can mislead you into downloading useless software, but at least they are not malicious.
As mentioned this application excels in creating Ads, for which it gets paid by 3rd party sites. The biggest problem with that is the fact that popular and well known sites seldom need to advertise in such a manner, but less known sites with low quality goods do. Every time an Ad appears there is a good chance that it will lead to some sort of scam or at least a second hand product.
From Doc to PDF will ruthlessly create Ads and pester you with them and the only way to stop that is to remove it. You may have tried disabling the add-on in your Firefox or Chrome panel, but that won’t do much – you’ll have to get rid of the whole package. An Adware application is actually legal, since it doesn’t do any harm to your computer, but this doesn’t mean it’s easy to remove. Their creators do everything possible to make you give up before removing it and thus force the Ads upon you.
How you may have been infected by From Doc to PDF
Unlike computer viruses that typically exploit different system vulnerabilities in order to operate Adware applications like this one prefer subtlety. Most people will not willingly install such software on their computers, so the Adwares hide in the installers of other programs or on misleading advertisements that promote their “usefulness”. Indeed, most programs that promise to find “exclusive” and “best” offers for you are simply Adware applications that will filter legitimate advertisements on websites with Ads of their own. You may see hugely inflated price reductions, but this is merely a marketing trick and if you decide to actually purchasing something you will be buying it at its marketing value or even much higher than that.
Commonly the most employed trick when spreading Adware is to bundle it into the installers of other programs. Various free programs and download platforms employ this strategy. When installing such a bundled installer you’ll typically be asked if you prefer a quick or an advanced installation. The quick option is made to look convenient, but in reality it will automatically install all kinds of unwanted software that the creator of the bundle has seen fit to put inside.
- One easy way to prevent your PC from becoming infected in this way is to always read the text boxes of every installer and go for the custom/advanced option. It usually takes less than a minute to read through everything and in the process you can prevent any undesirable programs from becoming installed on your computer.
SUMMARY:
| Name | From Doc to PDF |
| Type | Adware |
| Detection Tool |
Remove From Doc to PDF
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

I have been using SpyHunter for many months. It finds “from Doc to PDF” removes the malware but does not remove the source.
Hi M Hurst, go to this page and there you can ask why is this happening.