This page aims to help you remove the Gloyah.net “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
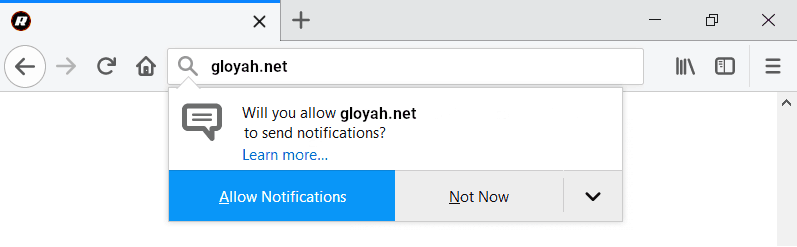
Will you allow gloyah.net to send notifications?
Allow notifications | Not now
Choosing the “Allow notifications” option will spam you with unrelated pop-ups and ads.
Unwelcome and unauthorized changes in the browser can be annoying and they may sometimes seem like an infection with some serious threat like a malware virus or a Ransomware attack. However, in most cases, what’s behind such unexpected changes in the search engine of the browser, in its homepage or toolbar or new-tab page address, is a software piece that got installed in your computer without your knowledge. The said software piece can be referred to as a browser hijacker and it’s job is to add some extra elements to your browser that force your Firefox, Chrome or whatever other program you are using to start promoting certain ads and pages on your screen. One very recent example of this is the hijacker responsible for promoting the Gloyah.net page or search engine. If you are frequently getting page-redirected to a page with the Gloyah.net “Virus” logo on it or if there is a new search engine in your browser that has that same logo, then you can be pretty sure that you’ve been targeted by this browser hijacker. This is definitely not perfect for you or for your browser and system – while most browser hijackers are not particularly dangerous, they may oftentimes lead to the generation of unreliable advertising materials during your browsing sessions. As you probably know, clicking on random ads with unverified origins while surfing the Internet really isn’t a good idea – it may lead to Trojan Horse infections, Ransomware cryptovirus attacks and more similar issues. Therefore, we definitely advise you to keep away from any ads that this hijacker may show you and also to not use the Gloyah.net homepage, search engine or any toolbar buttons that may also be related to it. Usually, the presence of a hijacker in your system is nothing but an aggressive attempt at advertising something, and in this case that something is the Gloyah.net “Virus”. Still, there is no real reason to keep the new and unwelcome elements in your browser.
This is, however, where most users tend to struggle. Restoring a browser infiltrated by a hijacker to its previous state may be tricky if you don’t know how to get rid of the software elements responsible for the imposed changes. This is why you will find a guide included below this article that will show you what you need to do and where you need to look in order to locate all data related to the hijacker and responsible for the promotion of Gloyah.net inside your browser. Once you go through all the steps from the guide, the unpleasant changes made to your browser should no longer be there and the unpleasant page-redirects and ad disruptions should have stopped. In case you are, for some reason, unable to deal with this issue solely with he help of the guide, the removal tool linked in it can help you to quickly and automatically liberate your computer and browser from the invasive hijacker and bring things back to normal without any risks for the health of your system.
SUMMARY:
| Name | Gloyah.net |
| Type | Browser Hijacker |
| Detection Tool |
Remove Gloyah.net “Virus”
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment