This page aims to help you remove Glupteba Malware. Our removal instructions work for every version of Windows.
Recently, a new Trojan has been reported to our “How to Remove” team, and this time the threat goes under the name of Glupteba. If you’re reading this post because this specific Trojan has secretly compromised your personal computer, it’s best to find out how to identify and remove it quickly. Trojans can be very unpredictable, particularly the latest, and advanced versions like Glupteba, and can harm your entire system before you realize it. Luckily, we’re here to assist you with avoiding this, and coping with the malware without losing any time. First, we’ll point you to the information in the next paragraphs, just to help you gain a better understanding of how severe the Glupteba infection can be. Next, at the end of the article, there is a removal guide section, and the attached professional Glupteba removal tool. Ideally, you should be able to remove the Trojan with their assistance.
What harm may be caused by a Trojan like Glupteba?
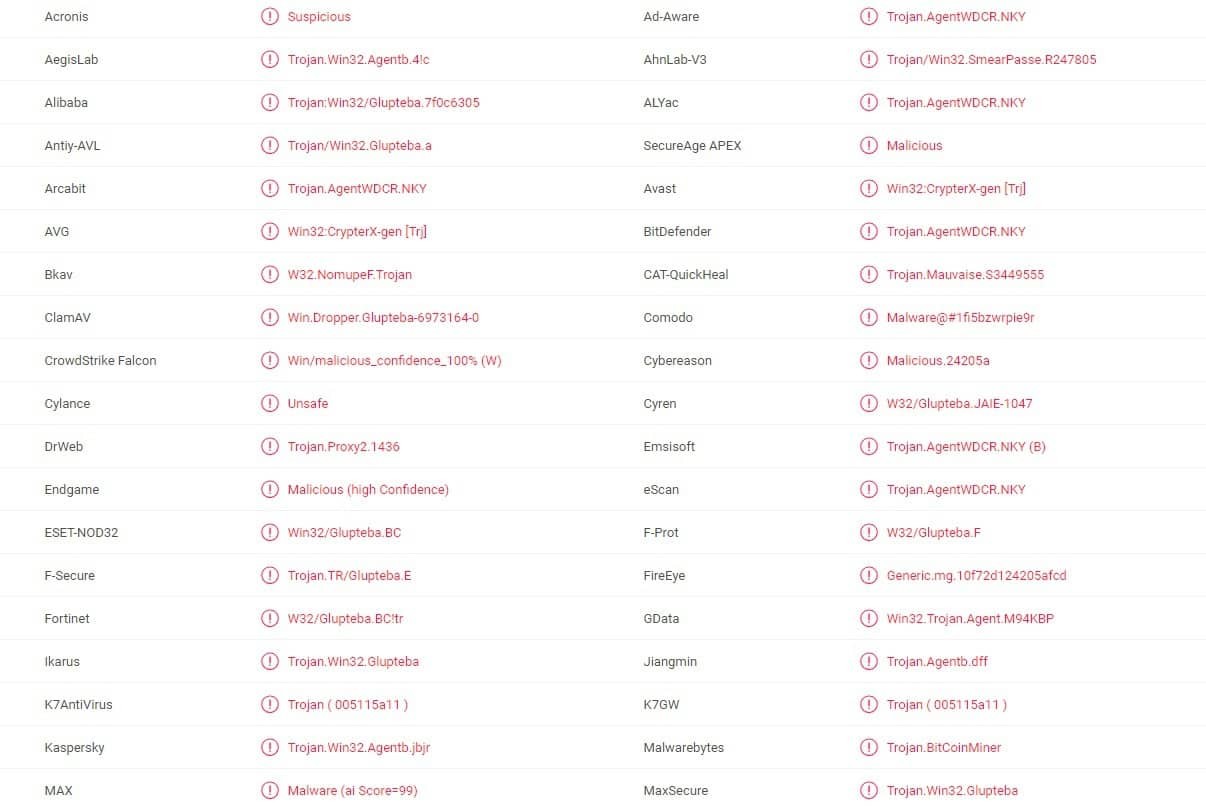
Multiple anti virus programs detecting the Glupteba Мalware
The Trojans commonly use a mixture of different techniques of infection, and a wide range of transmitters that can deliver the damaging code to your system. Their objective is to sneak in without being detected, and for that, they usually disguise themselves as some popular types of web content (most commonly as advertisements, email attachments, pop-up messages, social media links, emails with attachments, different media files, torrents, free downloads, etc.). A careless click on a random pop-up message can immediately inject into your computer an infection like Glupteba without any noticeable symptoms. Therefore, we always recommend our readers to not click on shady pieces of web content, too-good-to-be-true offers, suspicious deals, or clickbaits, while browsing the internet.
Unfortunately, this is generally not enough to protect you completely from an accidental interaction with this type of malware. It is therefore always a good idea to invest in trusted antivirus software. The reason is, in most cases, without the help of a professional security tool, it is very difficult to locate the Trojan in the system and remove it, because these threats typically hide in unusual system locations. For example, an infection such as Glupteba may imitate some regular processes or files of the system. Moreover, such a sophisticated Trojan can work quietly in the background of the OS, and launch various damaging actions without your awareness.
Trojan-related techniques of infection.
Threats such as Glupteba have damaging capacities that are very versatile. They can be programmed to undertake one damaging activity after the other, and, sadly, there is no way to know exactly how your computer can be damaged. In most cases, the Trojans can be used by the criminals who control them to acquire complete remote access to your computer. They can also use it to hack into your webcam, or microphone, and spy on you secretly. In addition, the Trojans are a form of malware often used to distribute Ransomware cryptoviruses, and execute banking frauds. The Trojans may steal your passwords, login credentials, debit card numbers, and other valuable data through a technique known as keylogging. They can also transfer data from your computer to remote servers without your knowledge, and what’s worse is that all the information stored on the infected machine can be modified, replaced, removed or destroyed.
SUMMARY:
| Name | Glupteba |
| Type | Trojan |
| Detection Tool |
Glupteba Malware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment