If your computer has been infected by [email protected] then you have a really serious problem. [email protected] infects your files with the .fff file extension and belongs to a family of viruses known as Ransomware, which are among the nastiest viruses an average user can encounter. These viruses are characterized by their ability to render all useful data on your computer worthless. This is done through a process called encryption and we’ll explain the way this virus functions in detail below. Ransomware viruses have existed since the nineties, but they only became more prominent in the past few years. The two famous ransomware viruses were named CryptoLocker and Cryptowall. By all accounts they were created and released in Russia at first, but then quickly spread all over the globe. Experts estimate that those two viruses alone have extorted more than $20 million from victims.
Typically the virus is accompanied by a pop up message titled “VIRUSFUCKEDYOURFILES” and an email where you can reach whoever created this. If you write to that email you receive the following message:
- Hello. I f you wish to get all your files back, you need to pay 3 BTC. How to get BitCoins? Google first Bitcoin ATMsSecond localbitcoins google dot com3rd Google: buy BitCoinsThis is the only way to get your files back. There’s no way to decrypt Them without the original key. The price is non-negotiable. After paying 3 BTC and emailing the confirmation of payment you will be providedwith a decoder. If you do not trust me, you can email one of your files, I will decode it and send it back to you. Referring to: if the file you’re Requesting decode it is valuable, I will send you Either a quote from it or a screenshot. I apologize for any inconvenience Caused. Let me know if you want to Proceed. Thank you for cooperation.
[email protected] – method of operation
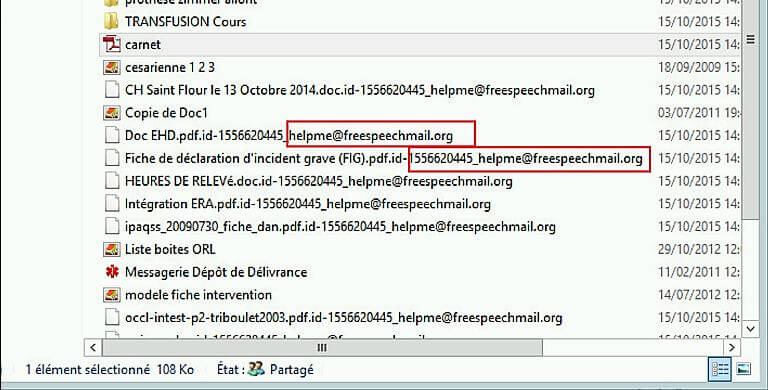
When [email protected] first makes contact with a computer it begins a search on all drives connected to the computer – this can include both Flash Drives and external HDDs in addition to the physical drives on your machine. Once the scan is complete the virus will target all popular and useful data types for encryption.
Encryption is a process where a data string is to transformed into another data string through the help of a key/code. Once encrypted with the .fff file extension, a file is completely unreadable (and unusable) without the key that can be used to reverse this process – this is called decryption. The original file is then deleted, but the encrypted copy remains. Once [email protected] finishes encrypting your files it will make itself known to you and demand ransom for the decryption key, which will always be demanded in BitCoins – an online currency that is completely untraceable. The hackers also have the gall to provide polite and detailed instructions on how to obtain BitCoins for real money. Of course, the warning will also contain warnings that if you temper with the files they will be completely unrecoverable and whatever else non-sense the hackers may think of in order to dissuade them from recovering your files for free.
Please remember that while [email protected] is a Ransomware virus and has nothing to do with your internet browsers the most likely way your PC was infected by it is via a Trojan Horse. Regardless of whether you are using Firefox, Chrome or Internet Explorer you should search your browser for the presence of this Trojan. It is recommended that you download professional software to scan your machine since Trojans are often hidden under different names and a manual search is likely to prove futile.
Lets discuss your options
Let us be clear. Removing [email protected] from your computer is important, because any new files you install will also get encrypted. Unfortunately simply uninstalling the virus won’t revert your encrypted files to normal. And to make things worse the hackers are actually telling the truth – unless you pay for the key those files cannot be decrypted and any anti-virus that promises you that is likely a scam.
What you can actually do is recover the deleted originals. The guide to do so is explained below, but keep in mind that this may not recover all files perfectly. Success rate depends on the empty space of your HDD at the time of deletion and also how many data was written on the drive afterwards. But remember – as long as you don’t delete the encrypted copies you can always choose to pay if unsuccessful.
Your other option is to simply pray and hope for the best. We STRONGLY recommend AGAINST this course of action. You are dealing with criminals that extort money from you. Anything you give them will be re-invested into other, more powerful viruses to be used on you in the future. Further they are not bound by anything to adhere to their word and there is absolutely no guarantee you will get your data back even if you decide to pay them.
Or you could always choose to suck it up and simply delete the data if it is not so important to you. Just make sure you delete the virus afterwards lest you be faced with another “VIRUSFUCKEDYOURFILES” message.
Ultimately the choice is yours, but the best course of action is to exhaust all other alternatives before paying the ransom money. Ignore whatever messages [email protected] generates to dissuade you from doing so.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Detection Tool |
Remove [email protected] Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment