This page aims to help you remove Idp.generic Avast Virus. Our removal instructions work for every version of Windows.
Idp.generic
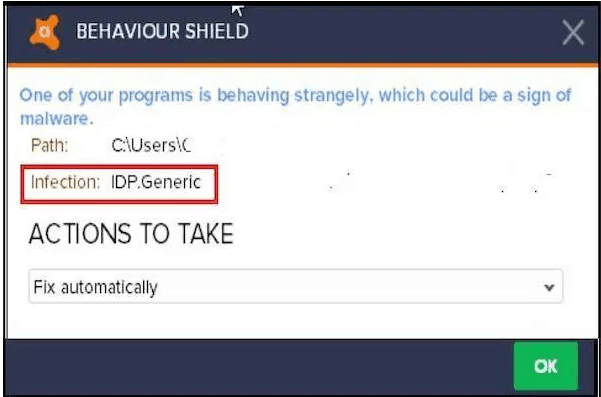
Wide range of files might be detected as infected with IDP.Generic
A new and very dangerous malware named Idp.generic has been spreading online these days, posing a threat to the regular web users. This threat represents a new addition to the family of the Trojan Horses. If you are on this page, it is very likely that this malware has sneaked into your system without you knowing about it and i may have started some very malicious background activities. Trojans are famous for their ability to undertake various damaging activities, while remaining hidden for long periods of time. That’s why it’s vital for the regular web users to know how to safeguard their systems, and how to detect and remove such threats on time, because once a piece of malware like Idp.generic enters the system, no visible signs of its presence may be present. At the same time, the damage caused by the Trojan can often be irreversible.
Security experts are informing that there has been a spike in the amount of newly created Trojan Horses in the last several years. Therefore, it does not matter what device you are using to connect to the Internet – it could be a laptop, a tablet, a smartphone or some other device. The essential thing here is that you have to protect it against these threats. That’s why we suggest you read the information that follows closely, particularly if you suspect that a Trojan horse named Idp.generic has sneaked inside your computer.
Idp.generic is an advanced Trojan Horse piece of malware, created by a group of hackers with malicious intentions. The specifics of this infection are still to be closely studied, since the nature of the Trojans is very versatile. However, so far, what we can tell you about Idp.generic is that the detection of this malicious piece of software in the system can be very challenging. The reason is, this advanced infection has the capacity to hide deep within the OS, and even imitate some essential system files and processes. This is done in order to mislead the users and stop them from identifying the infection on time.
The Idp.generic Virus can infect you secretly.
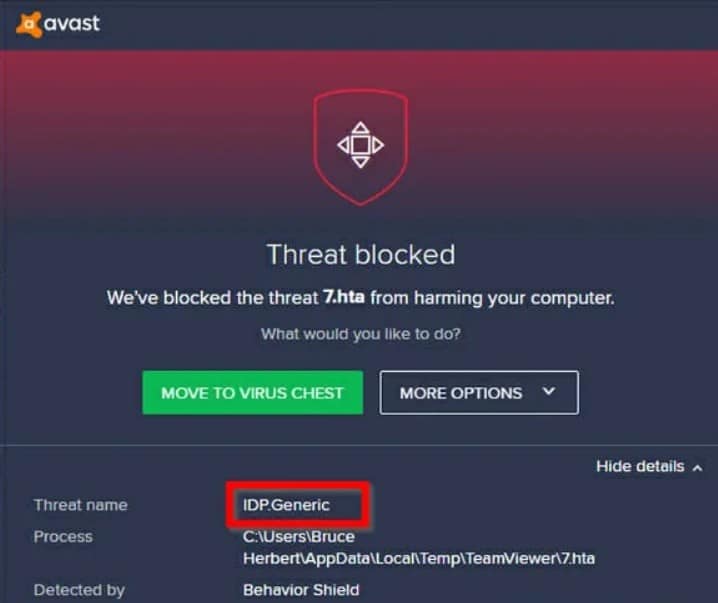
A lot of users are getting the idp.generic virus detection on their files
Typically, some legitimate-looking file, ad, or a link conceals the malicious code and acts as a transmitter of the virus. It could be an attachment to an email, a misleading ad, a torrent, a clickbait link, or some random pop-up message prompting you to visit a particular website. One click is all that it takes to contaminate you and, unfortunately, there is often no way to know that you’ve been compromised unless you have a reliable antivirus program that can detect the malware. However, sometimes, even the antivirus programs may fail to identify the infection, particularly if the virus definitions have not been updated in a long time. If this is your case, or if you do not have a reliable antivirus program, then we strongly suggest that you follow the Removal Guide below. The instructions there will assist you with quickly and reliably identifying and removing Idp.generic. In addition, investing in a security program can help you prevent other stealthy infections, such as Ransomware or Spyware, from entering your computer, and can also help maintain your system in the future.
SUMMARY:
| Name | Idp.generic |
| Type | Trojan |
| Detection Tool |
Idp.generic Avast Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment