This page aims to help you remove Jeanson Ancheta Email Virus. Our removal instructions work for every version of Windows.
Jeanson Ancheta
Hello,My name is Jeanson Ancheta. They also know me as the trade king of dark web: ancheta-2yoI am an experienced software developer and I am the best hacker. 10 months ago, I hacked this email address. You can check it.. My first idea was to block and encyript your files. And than I would ask for a small fee to release them back. But than one day, You visited some dirty websites. You know what I mean naughty thing. And I silently activated your front camera and recorded You. Yes! You were playing with yourself. What a funny video. Now, I stole contact list of yourself. I have all the friends list. A lot of information is downloded to my system.I am asking from you a small fee of 750 USD. If you don’t pay, all the naughty screen videos will be sent to your friends and family.I will distribute them to everywhere.
Jeanson Ancheta is a series of slightly differing email virus scams. The main purpose behind Jeanson Ancheta emails is to extort money from the targeted users. However there are reasons to believe that in some instances real virus threats might be behind Jeanson Ancheta emails. In those cases the affected users should be wary of dealing with potential malware infections.
Jeanson Ancheta generally hides well and camouflages itself as a something that seems harmless – it could be a link, a photo, an email or an attachment. Basically, it could be virtually anything the users could click on, as the malware’s aim is to infect the victims without them even realizing it. Unfortunately, oftentimes no visible symptoms may indicate that a malicious infection has occurred once the users have clicked on the camouflaged transmitter. This way the Trojan can sneak, and perform the harmful acts for which it has been programmed without any interruption. In some cases, it may take a while until the threat activates its malicious operations, but once it does, they are usually highly destructive, and could lead to all sorts of unexpected negative consequences. That is why, without doubt, such threats should be removed with all possible techniques, and as quickly as possible.
Jeanson Ancheta is an Email Scam
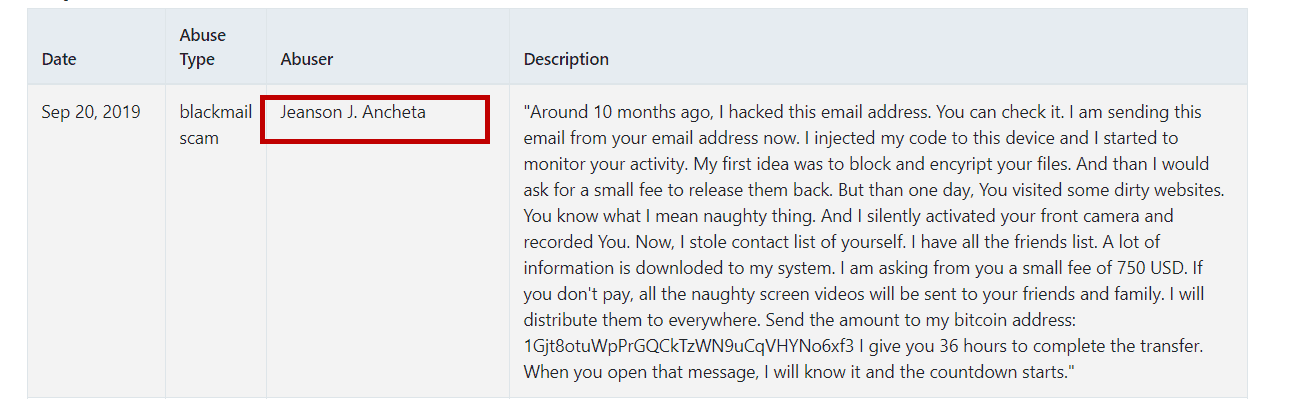
The James Ancheta Email Virus will try to trick you into sending money to the hacker.
That’s a good question, and you’d better learn its answer here, instead of experiencing the unpleasant consequences of a Trojan Horse attack on your own. If you’ve been infected with Jeanson Ancheta, the hackers who control it have almost limitless possibilities to mess with your system, and compromise your privacy. Spying on you, stealing information, and destroying your system are just some of the most common malicious activities that can be done with the help of this Trojan on your computer. For instance, the hackers can use the infection to secretly monitor every single thing you type on the keyboard, and gain illegal access to all your debit and credit cards, your online banking details, your social profiles, and more. An infection like Jeanson Ancheta can act also as a backdoor for other types of malware such as Ransomware, and viruses.
Of course, no one wants to end up with a Ransomware, or another malware on their machine, which is why removing the threat once you come to know about it is absolutely essential.
How to remove Jeanson Ancheta from your system?
Removing Jeanson Ancheta is a delicate task, and it’s best to follow the instructions we’ve prepared in the removal guide below if you’re going to do it all on your own. Pay attention to all the steps tough, as the Trojan usually hides deep within your system, and if you delete some of vital system data by mistake, you may cause corruption rather than remove the infection. To avoid this risk, and to deal with the virus quickly, we suggest you double check your PC with the professional removal tool attached to the guide.
SUMMARY:
| Name | Jeanson Ancheta |
| Type | Trojan |
| Detection Tool |
Remove Jeanson Ancheta Scam
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment