This page aims to help you remove Jollywallet. These Jollywallet removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Online adverts covering my screen – is my PC infected by a virus?
If you’re one of the many users asking this question, keep on reading so as to find out what exactly is happening to your PC. In the past 48 hours we have been bombarded with questions in a variety of languages but regarding one and the same thing – “o que é jollywallet”, “como tirar jollywallet”, “como remover jollywallet“. It was obvious to us that we need to help our readers.
In this article, we will explain to you both what program is causing those intrusive adverts and how you can get rid of the nagging piece of software.
The infamous Adware
Obstructive online ads are usually caused by a program called Jollywallet or any other similar piece of software. However, since Jollywallet is one of the latest of its type, it has the highest chances of being the one that’s currently messing with your PC. The term used to describe programs that cause unwanted and annoying adverts is Adware. This is exactly what Jollywallet is. There are many free programs that have the advert-generating feature. However, a big part of them have some kind of useful value and are simply supported by the ads. The difference between such programs and Adware is that the latter usually does not have any actual usefulness for the user. Sometimes, it might be hard to tell whether a program is simply supported by ads or is Adware. Often, it all depends on the personal perspective. Still, more often than not, people get heavily annoyed and aggravated by those ads and want to have the software that’s causing them removed from their machine. That is why we’ve written this article – to help those of you who want to get rid of Jollywallet ASAP.
Is Jollywallet a “Virus”?
The simple answer would be no, Jollywallet is not a virus. It should be obvious by now that Adware is something very different from a virus. Still, for clarity’s sake, we need to inform you how problematic Adware can be and why it cannot be referred to as a virus, as opposed to actual malicious threats such as ransomware. First of all, programs like Jollywallet are almost always legal. Of course, they are still very annoying, but at least they are not developed and distributed illegally. Secondly, adware itself is very unlikely to attempt to harm your PC. The worst thing that such a program can do, for the most part, is slow-down your PC due to the higher CPU and RAM consumption required by the Adware. Some more aggressive programs of that type have been reported to monitor and record your browsing activity, but this is usually done just so that the they might optimize the displayed ads according to your recent searches. All in all, Adware programs are quite safe and even though they can really be a pain in the neck, they should not be a reason to panic.
However, we ought to tell you that it is still possible that Adware might trick you into exposing your machine to more serious threats via the ads it displays. Though most of the adverts you see are safe, there’s always a chance that by clicking on some of them, you might get redirected to some potentially harmful and malicious pages. This happens very rarely, but is a real possibility. Thus, make sure that you stay away from those ads – do not click on them no matter what. Or better what read on and learn how to “o que é jollywallet”, “como tirar jollywallet”, “como remover jollywallet“ or in plain english words remove Jollywallet.
Better safe than sorry
Preventing Jollywallet from getting into your system is always the best option when dealing with such programs. Even though they are not that problematic, it’s that much easier to keep them away from your PC than it is to have them removed. Therefore, here we will list the most commonly used Adware distribution methods along with what precautions you can take so as to keep your machine clean.
- File-sharing sites are a favorite tool of Adware developers to spread their intrusive products throughout the net. Often, such sites have hidden and/or deceptive links that serve as a direct download link for the Adware. Therefore, be careful when using such sites and also make sure that you only download content from those that are reliable and trustworthy. Avoid the shadier corners of the internet and don’t visit any illegal pages.
- The notorious spam e-mails are a very common method for distributing unwanted software. Although most such letters go straight into your spam folder, it won’t hurt being careful when opening messages from your regular inbox. If any newly received ones seem suspicious, deleting them might be the best course of action.
- File-bundling is regarded as the most successful method of the three. With this one, the adware is bundled with some other, more desirable program. If you install that other program using the default installation settings, you’d get all content that’s been added. Therefore, from now on, make sure that you always use the custom installation settings, where you can see what added installs there are and leave out anything that might seem shady or unwanted.
SUMMARY:
| Name | Jollywallet |
| Type | Adware |
| Detection Tool |
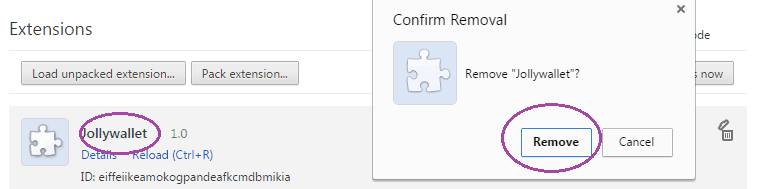
Remove Jollywallet from Chrome
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.




Leave a Comment