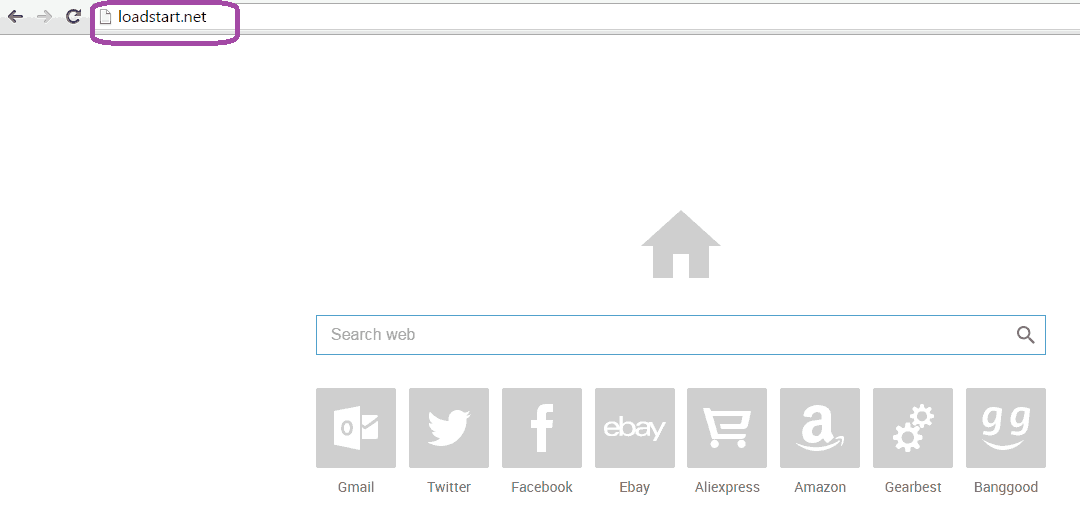
This page aims to help you remove Loadstart.net “Virus”. The removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
If you’ve been infected by Loadstart.net “Virus”, this article is just the thing for you. We’re guessing you must be searching for a way to remove this obnoxious “thing” from your computer and rid yourself of all the intrusive ads that it keeps hurling at you every time you try to surf the web. In addition to this, the program has most probably also changed your homepage and default search engine, which doesn’t really help matters either. Well, our removal guide is there to set things right. You will find it at the bottom of this page, simply follow the steps listed in it carefully, and you won’t have any trouble removing Loadstart.net “virus” from your computer.
What is Loadstart.net?
You’re dealing with a program that is generally referred to as a browser hijacker. It’s not a virus or malware of any kind, security experts would rather prefer placing it in the potentially unwanted program or PUP category. The reason for this is because this particular kind of software is actually legal for the most part, but there are some actions it performs that are a bit controversial and might not be considered quite safe. To name a one, hijackers are known for their ability to spy on your browsing activities and record your each and every search, visited location, etc. Even the occasional personal details that you could have typed in somewhere could be subjected to close monitoring. This data then promptly collected and analyzed in order for the program to begin producing myriads of ads that would match the preferences of the specific user, which would be estimated based on the gathered information. This is necessary in order to attract more clicks, as the developers of the software get paid each time someone clicks on one of the many ads. Of course, most people would be uncomfortable with the idea that someone is watching them and Loadstart.net’s bad reputation among users is also due to the fact that the developers may often sell this precious “intel” on to third parties.
More bad rep…
Another rather unsettling quality of Loadstart.net and others of its kind is the ability to produce fake ads. For example, you find yourself looking at a promotion of a certain product, which is showcased on one of the numerous banners that have been appearing lately. So you decide to check it out and click on the ad of interest only to be redirected to a page with completely different and irrelevant to you content. That can be a bit frustrating, but it’s nothing to worry about in comparison with what other scenarios could be in line. Though this is fairly rare, there can be malvertisements distributed among the other adverts. Malvertisements, in case the term isn’t familiar, are ads that have either been created by hackers or have simply been meddled with by them in order to infect them with malicious payload, most commonly – ransomware. Alternatively, the ads could be programmed to redirect you to a malicious website, filled with viruses that could infect you instantly, provided they can detect a weak spot in your system.
Avoiding browser hijackers from now on
You can learn from every experience, especially the unpleasant ones and contracting a hijacker does qualify as a pretty unpleasant experience. So, you might or might not be aware of how and where Loadstart.net came from. In the event that you’re not quite sure, think back and try to remember what software you downloaded recently. Chances are that the hijacker came bundled with it, especially if the software came from a questionable source like a file sharing site, torrent website or open source download platform. These are all likely places where developers would distribute their freeware or shareware, bundled together with other programs like adware or browser hijackers. A simple way to disable the bundled in contents would be within the setup wizard: just choose the advanced or custom installation settings and don’t let the name scare you. This option will basically just be allowing you to see the constituents of the bundle and will let you choose what will be included in the main install, if anything at all. If you don’t recognize any of the added programs or aren’t sure that you’d want them on your PC, simply untick the boxes opposite them and continue with the next steps.
SUMMARY:
| Name | Loadstart.net |
| Type | Browser Hijacker |
| Detection Tool |
Remove Loadstart.net “Virus”
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.




Hey, i have problems regarding step 4: The Folder ‘User Data’ of Chrome isn’t showing anything, even after activating that I can see hidden folders. What can I do?
If that’s the case, you can skip this part of the guide since there’s nothing to delete in that folder.