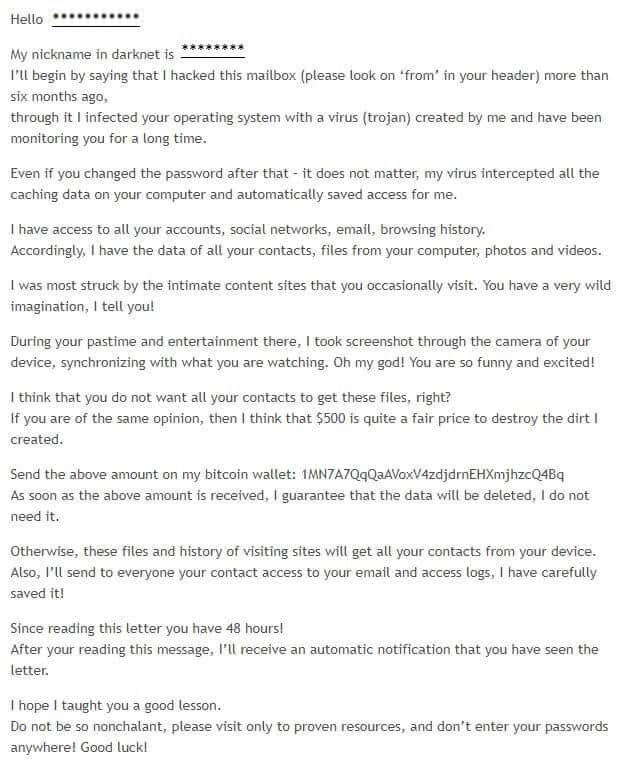
If you recently opened e-mail, stating something like this:
Then you are most probably a target of an email scam. However it is also very likely that you indeed have a malware on your device and need to take measures to rectify that situation as soon as possible.
The aim of the article that you are about to read is to reveal the malicious characteristics of a very dangerous computer threat that goes under the name of “My Nickname in Darknet Is”. This malware belongs to the Trojan horse virus family and may be used as a multipurpose malware tool. In case that you have “My Nickname in Darknet Is” on your computer, you should take immediate actions towards removing it from the machine. Otherwise, you may be faced with a variety of issues on your PC and all kinds of potential software damage. In the next paragraphs, you will learn more about the harmful abilities of this Trojan horse and about the entire software family that it belongs as well as some useful pieces of advice about prevention and protection. In the Removal Guide below, we will share with you the exact steps on how to remove “My Nickname in Darknet Is” from your machine and further down this article, you will also learn what symptoms or problems to expect if you have this nasty malware piece inside your PC. Just pay close attention to the next lines and follow the instructions as they are shown.
Trojans and their nature – here is what you should know
Nowadays, the web space is full of all sorts of programs some of which are really helpful, some are entertaining, while others are created with the sole aim to cause harm. Among the most dangerous and malicious programs that you could encounter are the insidious Trojan viruses. The representatives of this malware category can be blamed for all sorts of criminal deeds. In fact, the statistics show that more than 70% of all the malware-caused contaminations globally are caused by representatives of the Trojan Horse malware class. This percentage gives a pretty clear idea of how common these threats are. That’s why, in the paragraphs that follow, we will stop our attention at their characteristics and their harmful abilities, mainly focusing on the recently released “My Nickname in Darknet Is”. Speaking of “My Nickname in Darknet Is”, the next guide will show you how you might be able to get rid of it in case your computer has gotten attacked by this nasty cyber threat.
So, what makes the Trojans so fearful? Well, the secret lies in the way these computer threats operate. At first sight, such threats may appear completely harmless and may resemble legitimate programs, files, ads, attachments or links that you may come across on social media platforms, in your email inbox or on some random website. However, their true nature and purpose is revealed once they have infected the targeted system. Usually, such threats are created to serve a variety of insidious criminal purposes and could be used in different ways. “My Nickname in Darknet Is” is a new addition to the Trojan horse family, which comes with a full set of harmful abilities. The malware is very likely to remain hidden in the system for a long time and secretly perform a bunch of harmful tasks without the users’ knowledge.
What damage may “My Nickname in Darknet Is” cause?
There might be many ways in which “My Nickname in Darknet Is” may harm your computer. Such a sophisticated infection can easily launch malicious code for system destruction, data deletion, corruption of software, various Registry modifications or insertion of other malware. The Trojan horse may launch criminal tasks directly controlled by the hackers or may provide them with full remote access to the compromised machine. “My Nickname in Darknet Is” may also serve as a backdoor for nasty viruses like Ransomware or Spyware. It can sneak them inside the computer through system vulnerabilities or weaken the security software in order to enable other malware to enter the machine. In some cases, the Trojan could be used as an effective tool for espionage and data theft. With its help, the crooks may gain access to your passwords, login credentials, sensitive documentation, banking details and everything valuable that you keep on your PC or inside your online accounts. Basically, no data can be safe and you may end up with your virtual identity stolen or your bank accounts drained if the malware transfers your sensitive information to the hackers. All this comes to show that you should remove “My Nickname in Darknet Is” immediately and scan your PC with a reliable antivirus software for any hidden malicious code left inside your system. For assistance, check out the Removal Guide or use the professional “My Nickname in Darknet Is” removal tool.
How can you get infected with “My Nickname in Darknet Is”?
If you are careless while surfing the web, you are surely increasing the chances of getting your machine exposed to malware programs such as Trojan Horses. These threats, as we said above, are really common and also extremely difficult to detect. That’s why, the best way to protect your PC is to invest in reputed antivirus software and run regular system scans with it. It is also very likely that you get mislead by a carrier of a malware virus thinking that it is a legitimate piece of content because, in most of the cases, the malware sources tend to look legitimate and safe. That’s why, it is a bad idea to only rely on your cautiousness. Of course, this does not mean that you should click on every pop-up, spam message, ad or email attachment that comes your way. Be cautious, stick to well-known web locations and avoid downloading and installing software from non-reputed developers or sketchy sites and platforms.
SUMMARY:
| Name | “My Nickname in Darknet Is” |
| Type | Trojan |
| Detection Tool |
Remove My Nickname in Darknet Is Email Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment