This page aims to help you remove the Notification-list.com Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Notification-list
Notification-list.com is a Browser hijacking piece of software that can change the way a browser works. Most commonly, Notification-list.com may modify your search results by replacing the default search engine with another one that generates sponsored results.
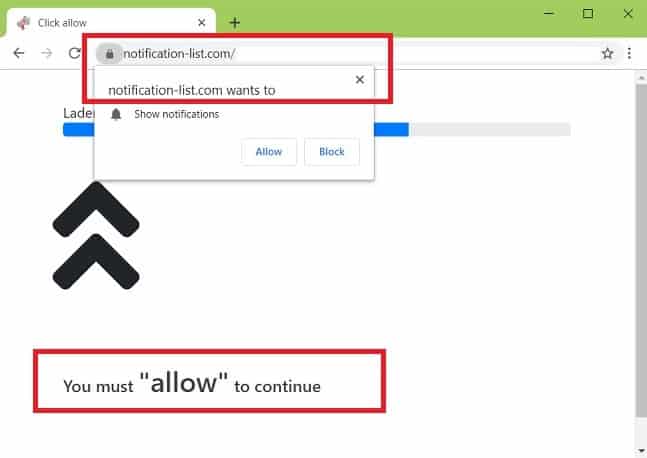
Recently, a number of web users have been confused by the activity of a program called Notification-list.com. Some people have reported an aggressive stream of ads, pop-up messages and colorful banners all over their screens, while others have been disturbed by the new search engine or homepage URL which Notification-list.com has imposed on their browsers. Understandably, there has been a great deal of speculation and confusion about this program among the users of popular browsers such as Chrome, Firefox, and Explorer. This article, however, is dedicated to clearing some of the misunderstandings and assisting the users to remove the unwanted application and uninstall its changes.
To put it simply, Notification-list.com is a kind of ad-generating software that is designed to take over your browser, enforce its own settings, and redirect you to sponsored web locations. You may also notice that such software may set another search engine, or a specific URL to the new tab’s default page that may be different from what you’re used to seeing, or what you have manually set.
The Notification-list.com is on Chrome
According to researchers Notification-list.com is a browser hijacker. Security problems such as Notification-list.com are known to cause website redirects, intrusive advertisements and even phishing attempts.
First, however, let’s be clear about one thing – Notification-list.com isn’t a virus, but a browser hijacker. The viruses are malicious pieces of code, designed to inflict terrible harm on your computer. Furthermore, such threats can steal data, destroy records, and mess with the OS in a really bad way. Malicious threats such as Ransomware or Trojans, for instance, will not spare your machine until they complete their harmful agenda. Compared to that, a Browser Hijacker like Notification-list.com is just an annoying ad-generating program that constantly fills your screen with pop-up ads, colorful banners, and redirect links.
This is basically a type of software tool used by the online advertisers who are looking to place their ads directly on the users’ screens. At the same time, such software allows the developers to earn pay-per-click profits from displaying sponsored ads, and from redirecting the web users to specific web pages quickly and efficiently. There are many examples of browser hijacker programs out there, and they are widely used every day to display and promote advertising-related information on the people’s screens.
Yet, sometimes, browser hijackers like Notification-list.com can be exploited by people with malicious intentions to display and distribute links to potentially harmful and malicious web pages that may contain viruses. This can happen if they insert a malicious ad or a harmful page-redirect link inside the flow of regular ads the hijacker displays. And, if you happen to interact with such content, you may accidentally get infected with a Ransomware, a Trojan Horse, or with some other form of malware.
The bottom line is that it is not a good idea to click on everything that a program like Notification-list.com may display. At this point, you might also be wondering if it is a good idea to uninstall the Browser Hijacker, and remove all of its ads permanently. And this is exactly what we would encourage you to do if you want to eliminate the above-mentioned risk. In fact, we will show you how to safely remove this irritating program from your machine, and how to uninstall the changes that it might have imposed on your browser.
SUMMARY:
| Name | Notification-list.com |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Notification-list.com Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Reply