This page aims to help you remove Openthis.site Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
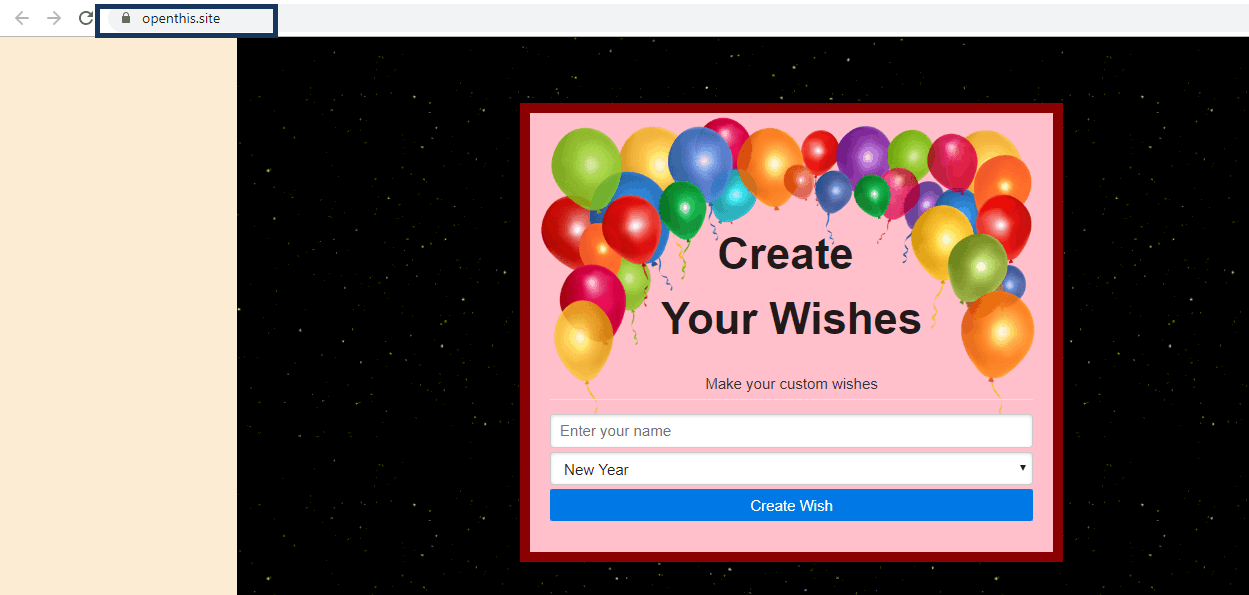
If you can hardly navigate through the web pages in your browser and your browsing gets constantly interrupted by dozens of advertisements, banners, pop-ups, and automatic page-redirects, then there is a great possibility that you are dealing with a Browser Hijacker. And more specifically, a new Browser Hijacker representative, called Openthis.site. These kinds of programs are notorious for the intrusive and unwanted advertisements they can display on your Chrome, Firefox, Explorer or any other browser, as well as the modifications they tend to apply to the homepage or the search engine settings.
The moment Openthis.site gets installed on your system, a brand new browser homepage or a new toolbar may substitute your present one and you may start to get automatic page-redirects to some different tabs, full of deals and pay-per-click advertisements. Fortunately, on this page, we will show you exactly how to remove them, and safely uninstall their source.
To do so, you will need to closely follow the steps in the removal manual below, as they will help you to identify, and manually remove all Openthis.site associated data, and its traces. When you’re done, you won’t see all these banners and posts popping up anymore, and you’d be able to restore the original browser settings. But before scrolling down to the removal manual, it’s essential to get acquainted with the specifics of this kind of programs.
Could Openthis.site be called a virus or a malware?
Safe browsing status for Openthis.site is unsafe
When random ads start popping-up all over your screen, and automatic page-redirects prevent you from visiting the pages you want, you may naturally think that this is the doing of some strange malware, that has probably invaded your machine, and has initiated those activities without your knowledge or approval. This, however, is not the case when you are facing a program like Openthis.site. There is a big distinction between Browser Hijackers and real internet threats such as viruses, Ransomware, Trojans, or Spyware. A Browser Hijacker, generally, can’t initiate any direct damaging activity on your machine. At its worst, such software can only spam you with sponsored ads, pay-per-click banners, and pop-ups. Security experts even see it as one of the relatively harmless applications that you could land, because it can’t destroy your files or damage your system. A real Ransomware, for example, can not only secretly compromise the computer, but can also take all of your data “hostage”, and ask you to pay a ransom for its release.
However, we won’t be truly accurate if we don’t point out the potential risks of keeping a Browser Hijacker on the computer for long. For Instance, there is still a small chance you may bump into threats because the online crooks are constantly using new techniques to infect unsuspecting web users. One of their most common methods is known as malvertising, and we should warn you about it. This infection method is based on the distribution of malicious ads, and attractive offers in the form of random pop-ups, along with other legitimate advertisements.
If you happen to click on such a compromised ad, and that may happen if you let a programs like Openthis.site, Bigclicker.me or The Goodcaster spam your screen with various random advertisements, you may land on some malware-infested page or get redirected to illegal web locations where you could get infected. Therefore, to eliminate that risk, it is best to uninstall Openthis.site from your computer with the help of the instructions below.
SUMMARY:
| Name | Openthis.site |
| Type | Browser Hijacker |
| Detection Tool |
Openthis.site Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment