This page aims to help you remove Px.adhigh.net. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
About The Px adhigh net Malware
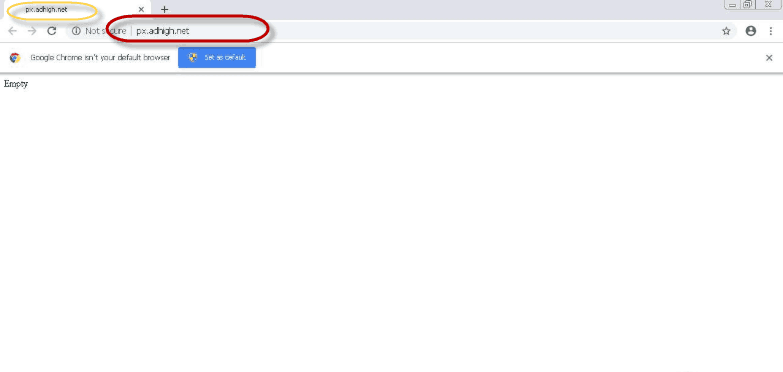
An example of Px.adhigh.net’s initial redirect
In case that your browser (it could be Chrome, Firefox, Explorer, or any other) has recently started to spam you with dozens of ads, pop-ups, page-redirects, and banners during your regular web searching sessions, and you have noticed a change in the browser’s main search engine or the homepage URL, then the chances are that you might have installed a Browser Hijacker such as Px.adhigh.net on your computer. The installation itself has likely happened after you have unknowingly given your approval, especially if you have recently installed a software bundle or some new free application inside your system. The changes in the browser’s behavior, however, you have probably noticed right away. This is because programs like Px.adhigh.net, Search Baron, Myloginhelper.com typically modify the default settings of the main web browser without the authorization and the knowledge of the user. Unfortunately, since the uninstallation of this type of software usually requires some advanced knowledge, most web users wrongly take the Browser Hijackers for some form of malware, similar to Ransomware or Trojans, and mistakenly refer to it as a “redirect virus”.
To your relief, however, Px.adhigh.net is not a virus – this is just an advertising program that tries to make you click on different pay-per-click ads, banners, and pop-ups during your web surfing sessions.
Here is what this program may do while on your system:
- The starting page of the affected browser may get replaced with a sponsored URL. The user may automatically get directed to that predefined page when they start their browser.
- The search engine may also be replaced and may not show the regular search results. Instead, it may redirect to third-party pages filled with ads, pop-ups banners, and promotional messages. The creators of the Browser Hijacker typically earn money on every click that leads to these pages through pay-per-click advertising.
- When you try to access a particular website, a page that belongs to an advertiser associated with the hijacker may be displayed instead, without your approval.
All this may not cause serious damage to your system, but it may seriously interfere with your regular web browsing and may constantly disturb you when you try to search for something on the web. That’s why, if the activities of Px.adhigh.net irritate you or don’t let you browse the web in peace, you may want to remove this program and uninstall its related components from your browser.
How to uninstall Px.adhigh.net and prevent such programs from hijacking your browser in the future?
The removal of a program like Px.adhigh.net usually does not require some specific computer skills. Yet, the process may be a bit confusing, and if you don’t know what exactly you need to delete, you may accidentally remove some important system file and corrupt the OS on accident. That’s why, in order to minimize the risk and to eliminate the unwanted software quickly, it is a good idea to use a professional removal tool, such as the one on this page, or a combination of the tool and the manual steps from the guide below.
To avoid Browser Hijackers, download software only from official or trusted websites and avoid using sketchy installers, P2P networks as torrent clients or other unreliable channels. Always, check the advanced, custom, and the remaining options of the software installation wizards and do not give permission for additional software to be downloaded or installed. Avoid clicking on intrusive ads, especially if they appear on some suspicious and unofficial websites. Once clicked, those ads may redirect you to suspicious sites (gambling, adult dating, pornography, etc.), or even worse – infect you with some real viruses like Ransomware or Spyware.
SUMMARY:
| Name | Px.adhigh.net |
| Type | Browser Hijacker |
| Detection Tool |
Px.adhigh.net Malware Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment