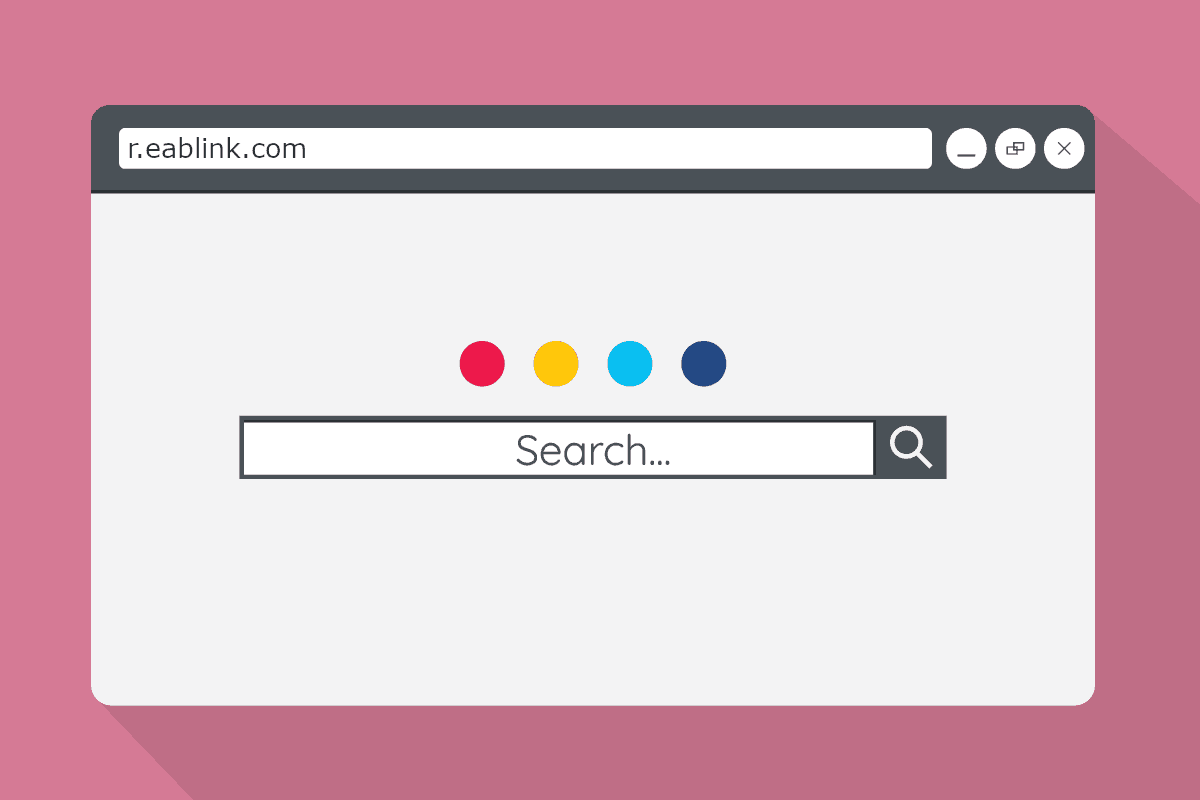
What is R.eablink.com ?
R.eablink.com is believed to be a browser hijacker. According to security experts R.eablink.com is tied to browser redirects and the promotion of sponsored content for profit in the form of pop-up ads.
The Browser Hijacker apps are not usually something that will threaten your computer, corrupt your data, or spy on you. However, they are still pieces of software that you should keep in your computer. The most obvious reason for this is the annoyance that these apps are known for causing. A browser hijacker doesn’t operate as a separate program. Instead, in order to function, it needs to latch onto a browser. The specific type of browser is usually irrelevant – it could be Chrome, Safari, Edge, Firefox and so on. Once the hijacker gets installed inside the browsing program, it would normally start to make changes in it. It may replace the precious homepage, it may introduce new toolbar buttons, set a new new-tab page, and even change the search service that the browser uses by default. Page-redirects to different sites are also known to occur whenever a hijacker is in the browser, and many hijackers also tend to display ads on the user’s screen. All of this is likely to cause quite a lot of irritation to the users who are forced to browse on a browser that has a hijacker in it. And what’s even more unpleasant is the fact that the only way to actually restore the browser’s settings to their normal state is through the full uninstallation of the hijacker. However, uninstalling a hijacker isn’t all that easy – it may take some time and tinkering with your computer, or require the use of a professional removal tool. The good news is that we have manual instructions on what you should do in order to removal such a hijacker from your browser, and below you will also find an advanced and reliable removal tool that can also help you get rid of the nagging software.
The R.eablink.com virus
The R.eablink.com virus is a security nuisance known as a browser hijacker. The so called R.eablink.com virus is characterized by the numerous browser redirects and pop-up advertisements.
A user claiming R.eablink.com is a virus
Many users have recently complained that the homepage of their browsers has been changed to R.eablink.com , and that they oftentimes receive ads on their screens that link to that page, or are coming from it. The likely reason for this intrusiveness is the recent installation of a hijacker in the affected browser, and this is not surprising. The main goal of most such apps is to promote sites, web services, software products, etc. The hijacker behind R.eablink.com is obviously one made with the specific purpose to promote this page. However, it is not excluded that you may get redirects to other similar pages, and also see ads in your browser that try to get you to purchase something.
In addition to being quite annoying, the change of your homepage to R.eablink.com, Newsmode.me or Metagmae.org , and the other unwelcome modifications in your browser, may lead to certain security hazards. A common concern that most security specialists have with regard to hijackers like this one is that their uncontrolled page-redirects may land the user on phishing sites, or on sites that spread Ransomware, Viruses, Trojans, and other forms of malware. Therefore, if you want to decrease the chances of getting your system corrupted by some Trojan, or your files encrypted by a Ransomware cryptovirus, we strongly advise you to make use of the following removal steps and uninstall the hijacker ASAP.
SUMMARY:
| Name | R.eablink.com |
| Type | Browser Hijacker |
| Detection Tool |
R.eablink.com Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment